How does SR policy operate in Segment Routing Traffic Engineering?
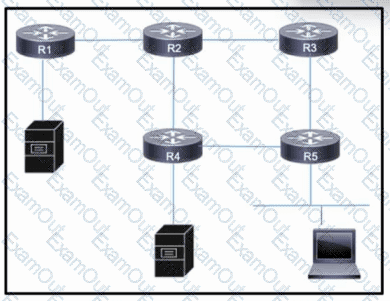
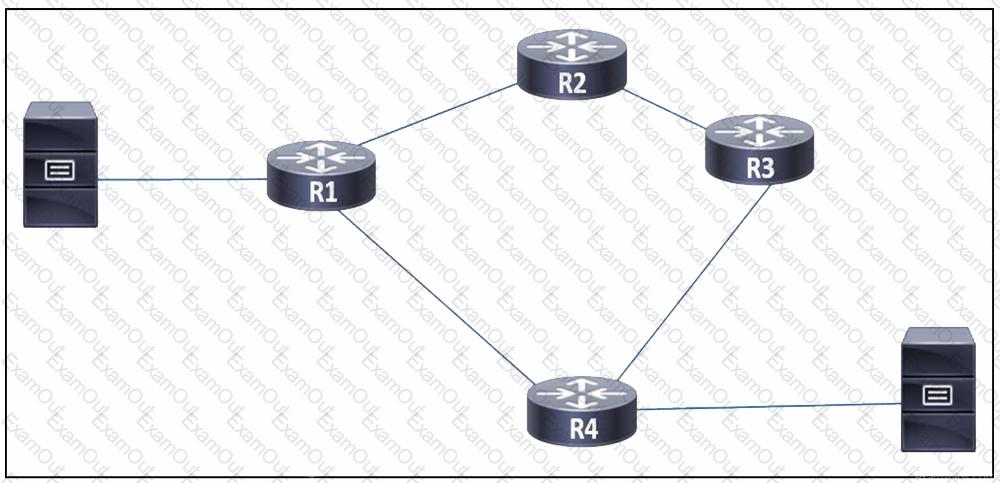
Refer to the exhibit. Users on a LAN connected to router R5 frequently open high-traffic connections with servers connected to R1 and R4. Users on R2 also require access to the servers, but performance is not a major concern and their traffic can be treated as secondary. As traffic on all links grows, the network architect wants to mitigate the potential for congestion on the link between R2 and R4.
Which action must the engineering team take to improve performance on the R2-R4 link for users on R5 while still allowing other traffic to flow?
Refer to the exhibit:
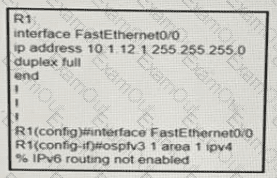
A network engineer is implementing an OSPF configuration Based on the output, which statement is true?
Refer to the exhibit:
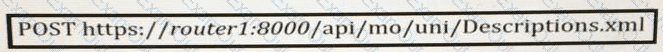
What does the REST API command do?
An engineer is moving all of an organization’s Cisco IOS XE BGP routers to the address-family identifier format. Which command should be used to perform this upgrade quickly with the minimum service disruption?
When implementing a REST API, how does an engineer mitigate security risks?
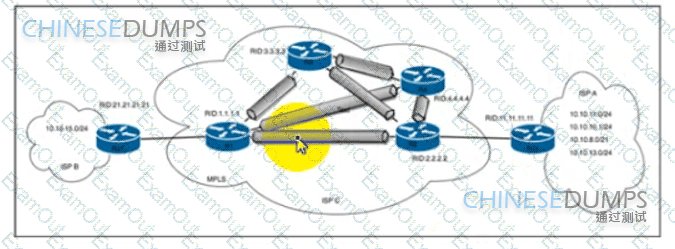
Refer to the exhibit An engineer at ISP C is configuring a new interconnection with ISPs A and B using the BGP protocol After the initial configuration the engineer noticed high memory usage and an abnormally large LIB table on router R2 Which two actions must the engineer take on R2 to minimize memory usage? (Choose two.)
How can shared services in an MPLS Layer 3 VPN provide Internet access to the customers of a central service provider?
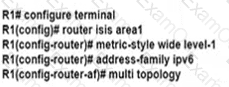
Refer to the exhibit.
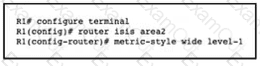
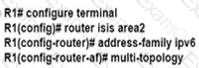
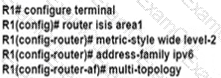
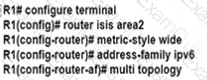
An engineer is configuring multitiopology IS-IS for IPv6 on router R1. Which additional configuration must be applied to complete the task?
A)
B)
C)
D)
What is the purpose of OSPF-TE extensions to MPLS traffic engineering functionality?
What is a feature of model-driven telemetry?
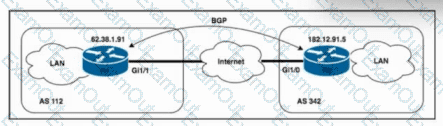
Refer to the exhibit. Routers R1 and R2 are connected over the internet, with the connection passing over four different autonomous systems. The company must mitigate potential DDoS attacks and protect the CPUs of the routers. A network engineer must secure all external connections on edge router R1 based on RFC 5082. R2 has already been secured. Which task should the engineer perform on R1 to achieve the goal?
Refer to the exhibit. A network engineer observed congestion between routers R1 and R4, which are connected on a point-to-point link. Two servers that reside on networks on R1 and R4 generate heavy traffic between them with most traffic going from R4 to R1. To improve overall performance, the engineer wants to drop inbound packets that exceed a configured threshold, without disrupting traffic that passes from R4 to R3. Which action must the engineer take to resolve the issue?
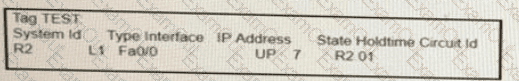
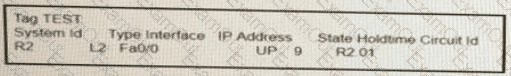
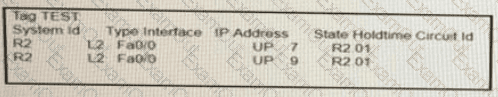
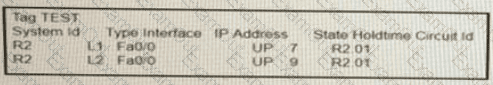
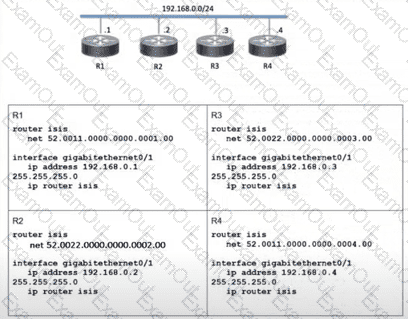
Refer To the exhibit:
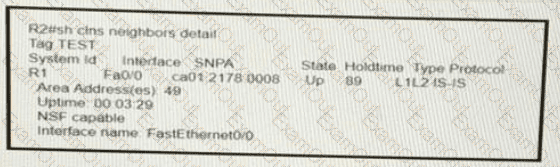
On R1, which output does the show isis neighbors command generate?
A)
B)
C)
D)
Refer to the exhibit.
Which two topology changes happen to the IS-IS routers? (Choose two.)

