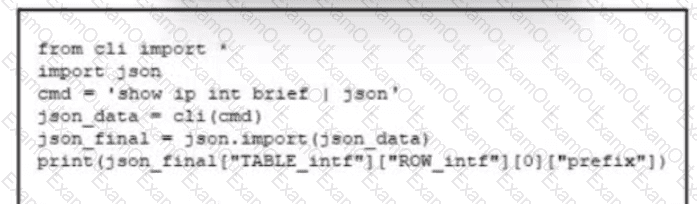
Refer to the exhibit. As part of the preparation for network automation, a client network is deployed with on-box Python. The test script fails to convert the output type from a string value to an object. Which line of code enables the output to be printed in JSON object format?
A wireless network engineer must configure a WPA2+WPA3 policy with the Personal security type. Which action meets this requirement?
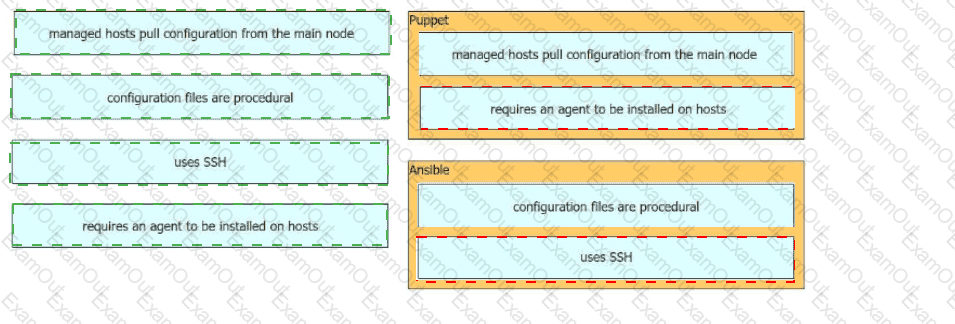
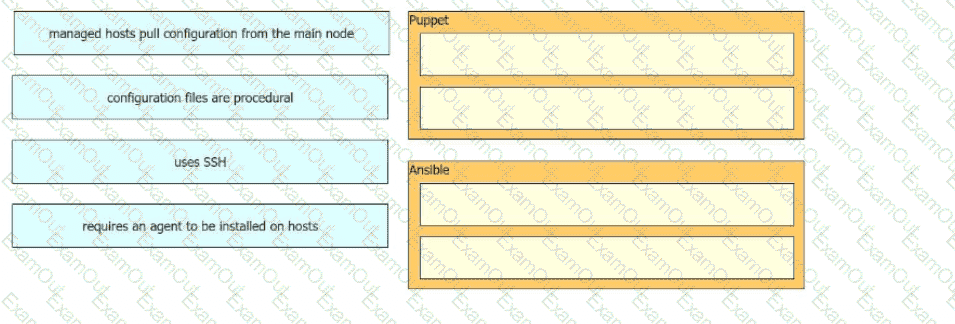
Drag and drop the characteristics from the left onto the corresponding orchestration tool on the right.
What is an advantage of utilizing data models in a multivendor environment?
Which new security enhancement is introduced by deploying a next-generation firewall at the data center in addition to the Internet edge?