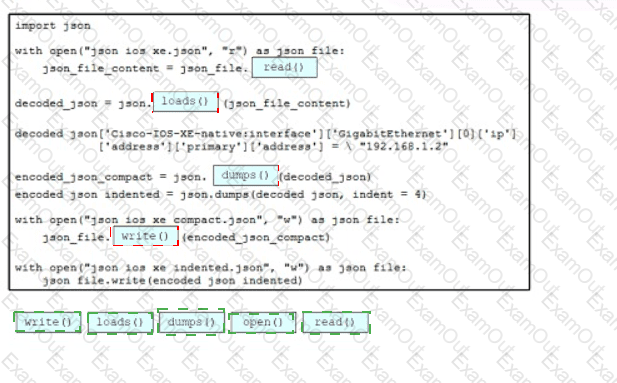
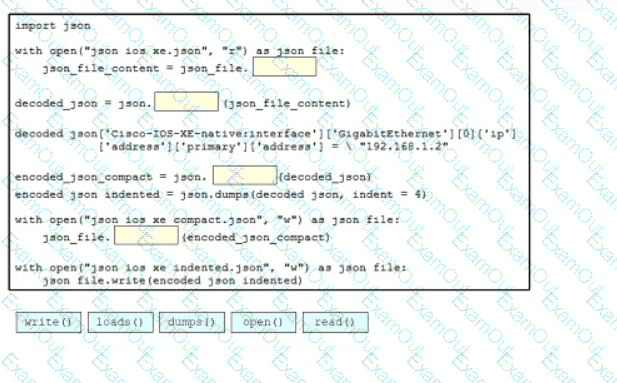
Drag and drop the code snippets from the bottom onto blanks m the Python script so that the program changes the IP address and saves It as a new JSON Me on the disk Not all options are used
What is one characteristic of an AP that is operating in Mobility Express mode?
In a virtual environment, what is a VMDK file?
What is the calculation that is used to measure the radiated power of a signal after it has gone through the radio, antenna cable, and antenna?
Which feature works with SSO to continue forwarding packets after a route processor failure until the control plane recovers?
What are two device roles in the Cisco SD-Access fabric? (Choose two.)
What is a TLOC in a Cisco SD-WAN deployment?
In a Cisco SD-WAN solution, which two functions are performed by OMP? (Choose two.)
How is the OAuth framework used in REST API?
Refer to the exhibit. A customer reports occasional brief audio dropouts on its Cisco Wi-Fi phones. The environment consists of a Cisco Catalyst 9800 Series WLC with Catalyst 9120 APs running RRM. The phones connect on the 5-GHz band. Which action resolves this issue?