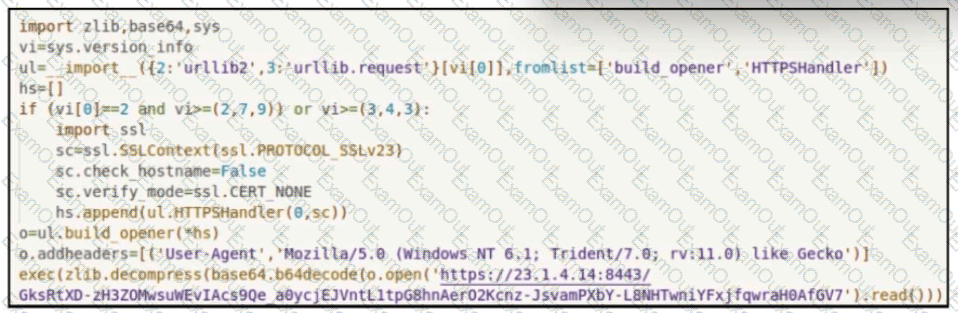
Refer to the exhibit.
Which encoding method is used to obfuscate the script?
An “unknown error code” is appearing on an ESXi host during authentication. An engineer checks the authentication logs but is unable to identify the issue. Analysis of the vCenter agent logs shows no connectivity errors. What is the next log file the engineer should check to continue troubleshooting this error?
A security analyst receives a notification from SIEM that an internal host has active connections to Tor exit nodes. The analyst investigates SIEM events related to the workstation and identifies that the host scans networks for servers with an opened TCP port 1433 An antivirus scan of the workstation does not determine any suspicious activity Which two actions must the analyst take to mitigate this behavior? (Choose two.)
An engineer must advise on how YARA rules can enhance detection capabilities. What can YARA rules be used to identify?
A financial company handling international transactions recently experienced a complex security incident The incident involves simultaneous DDoS attacks, suspected internal data leakage and the discovery of sophisticated malware implants that have remained dormant until triggered remotely During the incident it became clear that the current procedures are inadequate and plans to tackle issues were created on the go To counter this problem going forward, the IR team is developing an incident playbook to be used if a similar incident reoccurs Which set of elements of the playbook must be introduced?
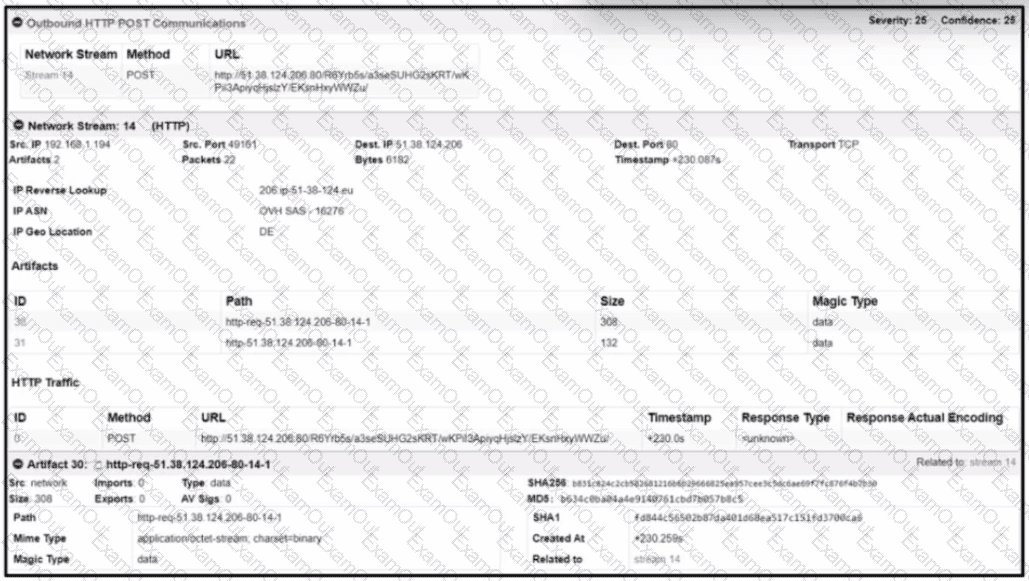
Refer to the exhibit.
What should be determined from this Apache log?
Data has been exfiltrated and advertised for sale on the dark web. A web server shows:
Database unresponsiveness
PageFile.sys changes
Disk usage spikes with CPU spikes
High page faults
Which action should the IR team perform on the server?
A security team is discussing lessons learned and suggesting process changes after a security breach incident. During the incident, members of the security team failed to report the abnormal system activity due to a high project workload. Additionally, when the incident was identified, the response took six hours due to management being unavailable to provide the approvals needed. Which two steps will prevent these issues from occurring in the future? (Choose two.)