An incident response analyst is preparing to scan memory using a YARA rule. How is this task completed?
Refer to the exhibit.
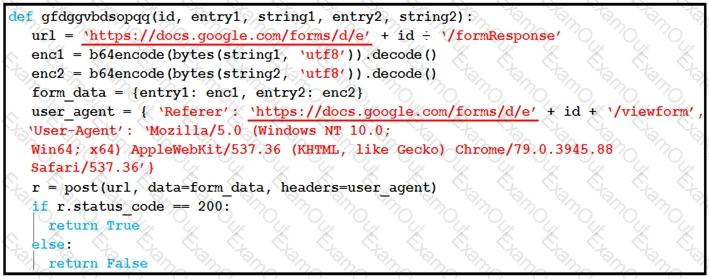
Which type of code is being used?
What are two features of Cisco Secure Endpoint? (Choose two.)
Refer to the exhibit.
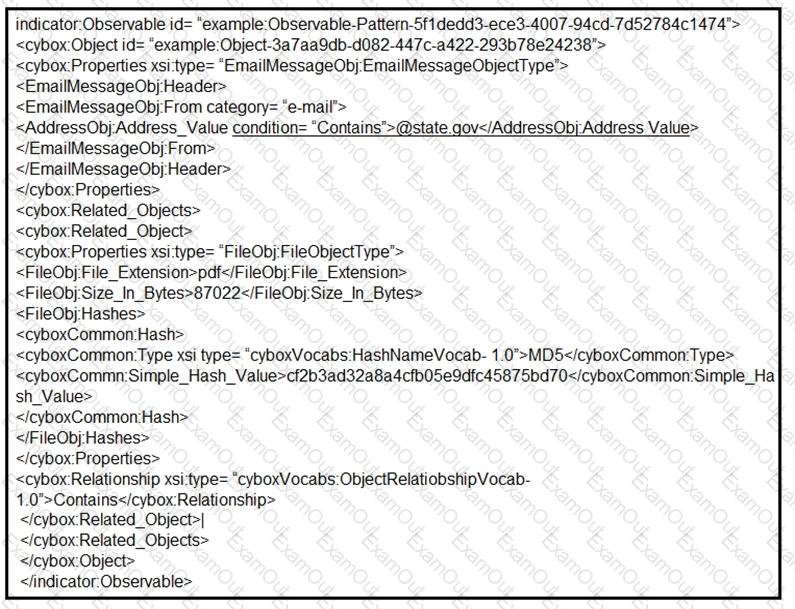
Which two actions should be taken as a result of this information? (Choose two.)
An organization experienced a sophisticated phishing attack that resulted in the compromise of confidential information from thousands of user accounts. The threat actor used a land and expand approach, where initially accessed account was used to spread emails further. The organization's cybersecurity team must conduct an in-depth root cause analysis to uncover the central factor or factors responsible for the success of the phishing attack. The very first victim of the attack was user with email 500236186@test.com. The primary objective is to formulate effective strategies for preventing similar incidents in the future. What should the cybersecurity engineer prioritize in the root cause analysis report to demonstrate the underlying cause of the incident?
Which tool should be used for dynamic malware analysis?
What are YARA rules based upon?
Which technique exemplifies an antiforensic technique?
A security team needs to prevent a remote code execution vulnerability. The vulnerability can be exploited only by sending '${ string in the HTTP request. WAF rule is blocking '${', but system engineers detect that attackers are executing commands on the host anyway. Which action should the security team recommend?

