An administrator is deploying a vSphere Supervisor with NSX. What will determine the deployment size for the load balancer?
An administrator is maintaining several Kubernetes clusters deployed through a Supervisor Namespace in a vSphere Kubernetes Service environment. One of the micro-services (a containerized API gateway) is failing intermittently after a recent configuration update. The pod is entering aCrashLoopBackOffstate. The administrator needs to collect detailed runtime information directly from the pod, including both thestandard output (STDOUT)andstandard error (STDERR)streams, to analyze the application ' s behavior before the crash.
Which command produces the required output?
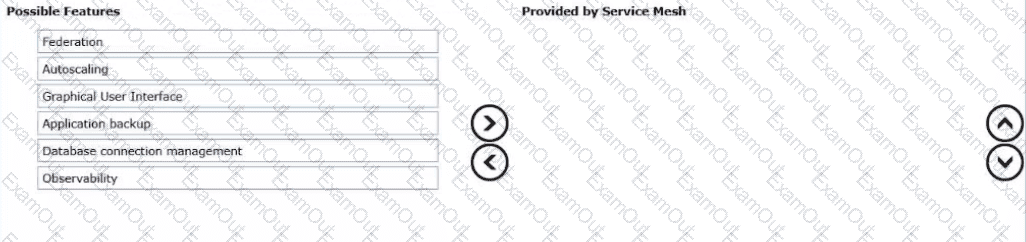
Drag and drop the three features into the correct order from Possible Features list on the left and place them into the Provided by Service Mesh on the right side. (Choose three.)
Which two types of groups can be created to collect and manage objects in an Istio-based service mesh environment? (Choose two.)
A VKS administrator is tasked to leverage day-2 controls to monitor, scale, and optimize Kubernetes clusters across multiple operating systems and workload characteristics.
What two steps should the administrator take? (Choose two.)
An organization has standardized on the following configurations:
vSphere Kubernetes Services upgrade is separate from vCenter upgrades.
A private registry will be utilized.
What is the recommended solution to adhere to these standards?
An administrator is tasked to install Istio service mesh for the vSphere Kubernetes Service (VKS). What command installs Istio?
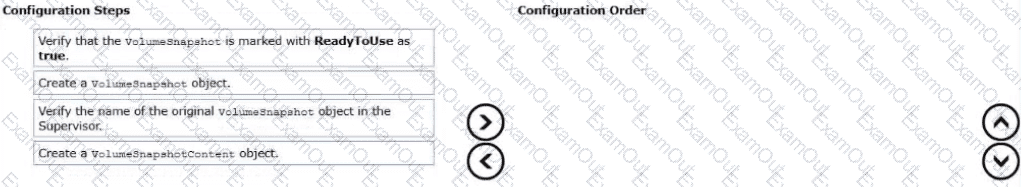
An administrator is tasked to protect a VKS cluster at a point in time. To satisfy the request, the administrator creates a pre-provisioned snapshot of the target cluster.
Drag and drop the four configuration tasks Into the correct order from " Configuration Steps " on the left and place them into the " Configuration Order " on the right. (Choose four.)
A remote site has a requirement for VMware vSphere Kubernetes Service (VKS). The environment has minimal storage available. Which action ensures the Content Library does not consume all available space on the datastore?
What component is used to provision VMware vSphere Kubernetes Service (VKS) service mesh workload clusters?



