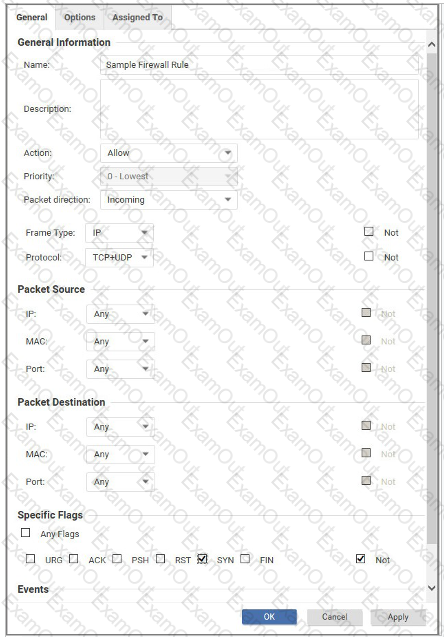
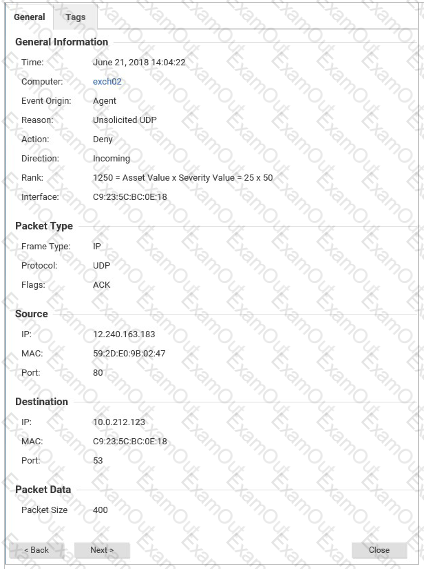
What is the effect of the Firewall rule displayed in the following exhibit?
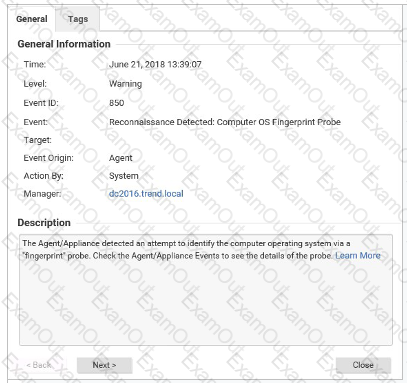
Based on the details of event displayed in the exhibit, which of the following statements is false?
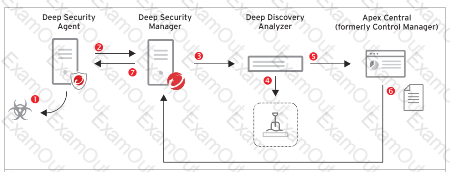
What is the role of Apex Central in the Connected Threat Defense infrastructure?
What is the result of performing a Reset operation on a Deep Security Agent?
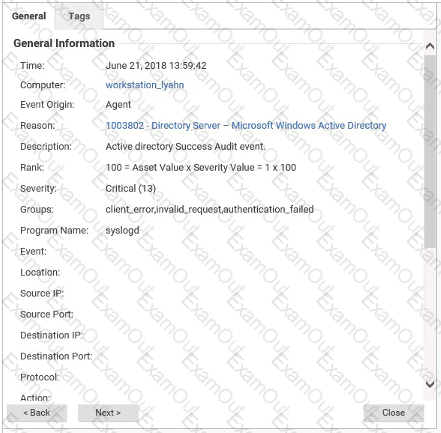
The details for an event are displayed in the exhibit. Based on these details, which Protection Module generated the event?
Policies in Deep Security can include a Context value. Which of the following statements re-garding Context is correct?
What is the purpose of the Deep Security Relay?
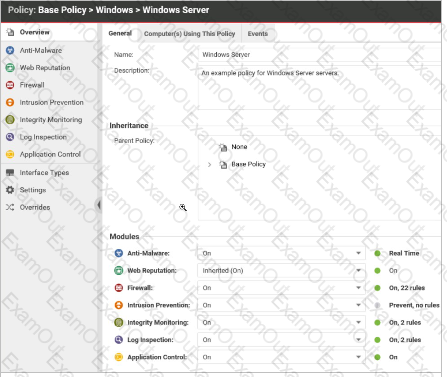
In the policy displayed in the exhibit, the state of the Web Reputation Protection Module is set to "Inherited (On)", while the state for the other Protection Module is set to "On". Why is the Web Reputation Protection Module displayed differently than the other Protection Modules.
The details for an event are displayed in the exhibit. Based on these details, which Protection Module generated the event?
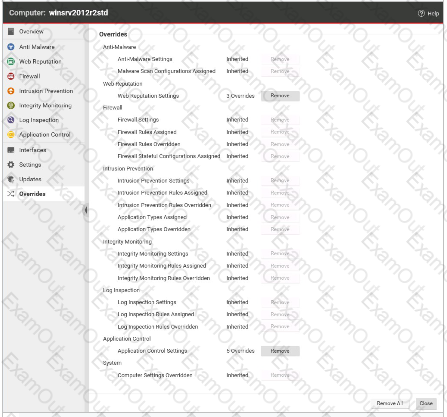
The Overrides settings for a computer are displayed in the exhibit. Which of the following statements is true regarding the displayed configuration?