Refer to the exhibit.
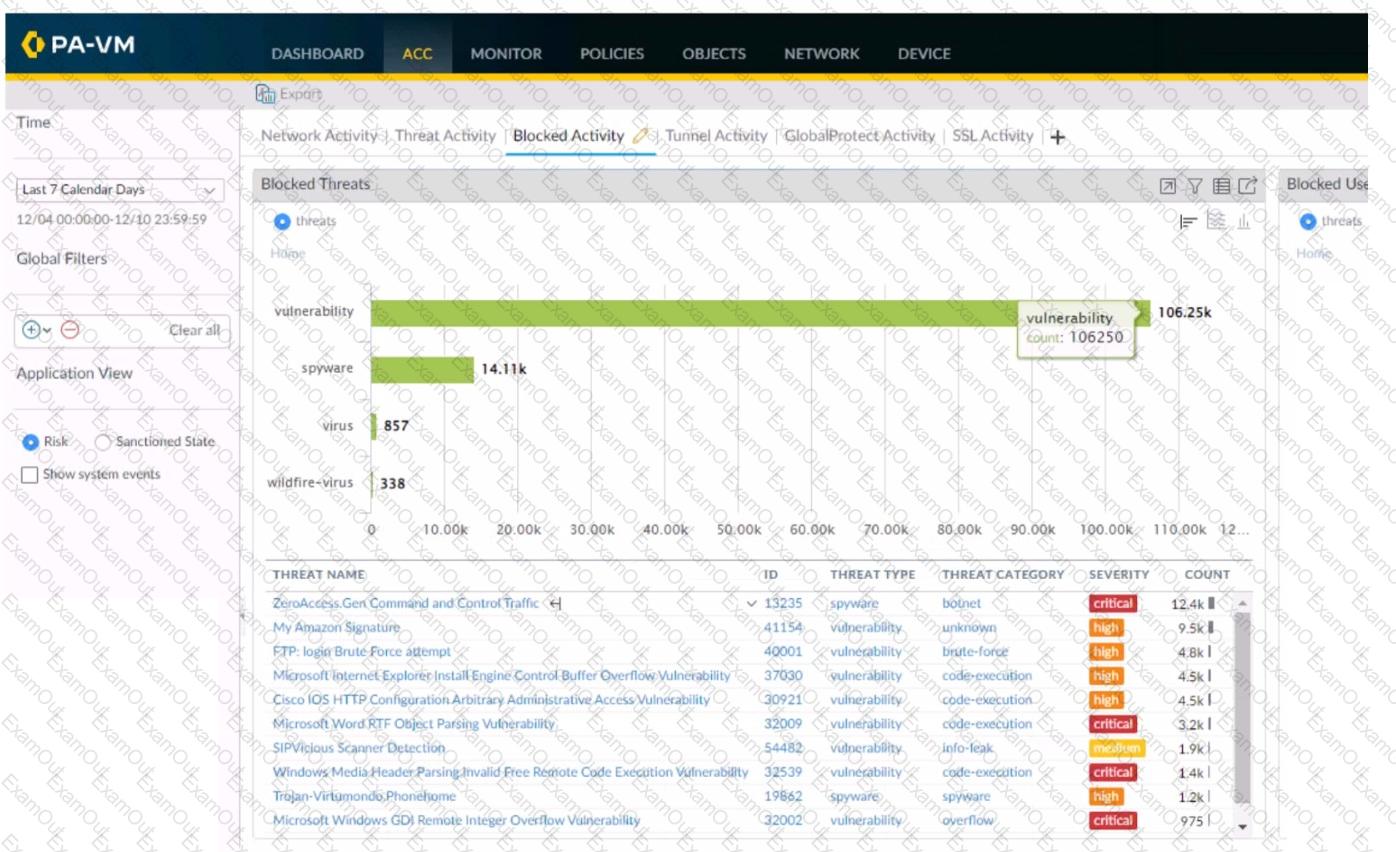
Using the above screenshot of the ACC, what is the best method to set a global filter, narrow down Blocked User Activity, and locate the user(s) that could be compromised by a botnet?
Which new PAN-OS 11.0 feature supports IPv6 traffic?
A firewall administrator has been tasked with ensuring that all firewalls forward System logs to Panorama. In which section is this configured?
Based on the images below, what is the correct order in which the various rules are deployed to firewalls inside the DATACENTER_DG device group?
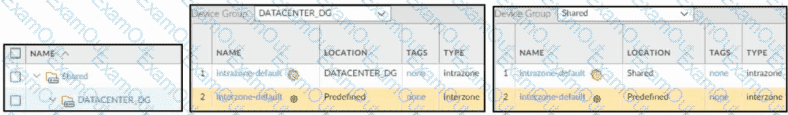
Based on the images below, what is the correct order in which the various rules are deployed to firewalls inside the DATACENTER_DG device group?
Information Security is enforcing group-based policies by using security-event monitoring on Windows User-ID agents for IP-to-User mapping in the network. During the rollout, Information Security identified a gap for users authenticating to their VPN and wireless networks.
Root cause analysis showed that users were authenticating via RADIUS and that authentication events were not captured on the domain controllers that were being monitored Information Security found that authentication events existed on the Identity Management solution (IDM). There did not appear to be direct integration between PAN-OS and the IDM solution
How can Information Security extract and learn iP-to-user mapping information from authentication events for VPN and wireless users?
A company is deploying User-ID in their network. The firewall team needs to have the ability to see and choose from a list of usernames and user groups directly inside the Panorama policies when creating new security rules.
How can this be achieved?
Which three methods are supported for split tunneling in the GlobalProtect Gateway? (Choose three.)
A firewall engineer is tasked with defining signatures for a custom application. Which two sources can the engineer use to gather information about the application patterns'? (Choose two.)
A firewall engineer is migrating port-based rules to application-based rules by using the Policy Optimizer. The engineer needs to ensure that the new application-based rules are future-proofed, and that they will continue to match if the existing signatures for a specific application are expanded with new child applications. Which action will meet the requirement while ensuring that traffic unrelated to the specific application is not matched?
An administrator is configuring a Panorama device group. Which two objects are configurable? (Choose two.)

