Which type of policy in Palo Alto Networks firewalls can use Device-ID as a match condition?
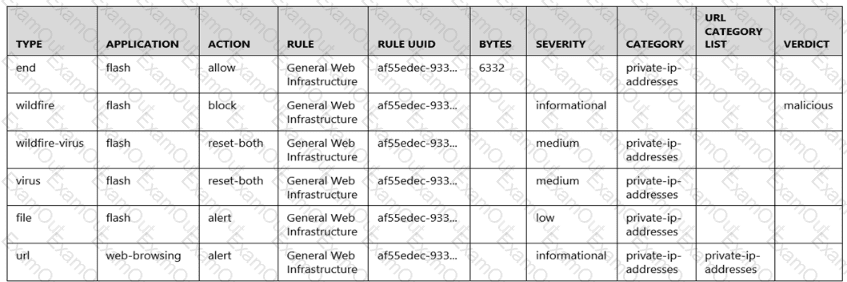
Given the following snippet of a WildFire submission log, did the end user successfully download a file?
An administrator has been asked to configure a Palo Alto Networks NGFW to provide protection against worms and trojans. Which Security Profile type will protect against worms and trojans?
Which action can be taken to immediately remediate the issue of application traffic with a valid use case triggering the decryption log message, "Received fatal alert UnknownCA from client"?
Which two key exchange algorithms consume the most resources when decrypting SSL traffic? (Choose two.)
When backing up and saving configuration files, what is achieved using only the firewall and is not available in Panorama?
Which statement regarding HA timer settings is true?
An engineer is configuring Packet Buffer Protection on ingress zones to protect from single-session DoS attacks.
Which sessions does Packet Buffer Protection apply to?
Review the screenshot of the Certificates page.
An administrator for a small LLC has created a series of certificates as shown, to use for a planned Decryption roll out. The administrator has also installed the self-signed root certificate in all client systems.
When testing, they noticed that every time a user visited an SSL site, they received unsecured website warnings.
What is the cause of the unsecured website warnings?
What is the benefit of the Artificial Intelligence Operations (AIOps) Plugin for Panorama?

