Which source is the most reliable for collecting User-ID user mapping?
A network engineer has discovered that asymmetric routing is causing a Palo Alto Networks firewall to drop traffic. The network architecture cannot be changed to correct this.
Which two actions can be taken on the firewall to allow the dropped traffic permanently? (Choose two.)
An engineer is pushing configuration from Panorama to a managed firewall What happens when the pushed Panorama configuration has Address Object names that duplicate the Address Objects already configured on the firewall?
An engineer is reviewing the following high availability (HA) settings to understand a recent HAfailover event.
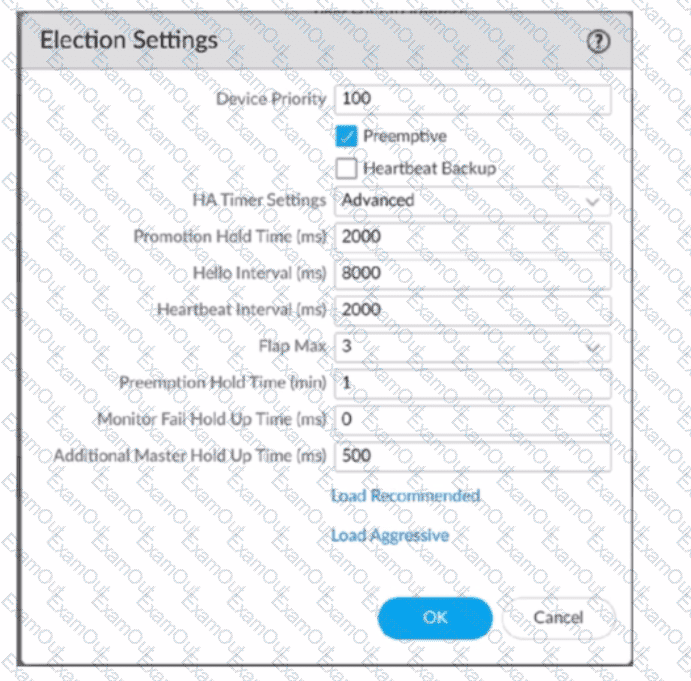
Which timer determines the frequency between packets sent to verify that the HA functionality on the other HA firewall is operational?
An organization conducts research on the benefits of leveraging the Web Proxy feature of PAN-OS 11.0.
What are two benefits of using an explicit proxy method versus a transparent proxy method? (Choose two.)
Which Panorama mode should be used so that all logs are sent to. and only stored in. Cortex Data Lake?
When you import the configuration of an HA pair into Panorama, how do you prevent the import from affecting ongoing traffic?
Which three options does Panorama offer for deploying dynamic updates to its managed devices? (Choose three.)
An enterprise network security team is deploying VM-Series firewalls in a multi-cloud environment. Some firewalls are deployed in VMware NSX-V, while others are in AWS, and all are centrally managed using Panorama with the appropriate plugins installed. The team wants to streamline policy management by organizing the firewalls into device groups in which the AWS-based firewalls act as a parent device group, while the NSX-V firewalls are configured as a child device group to inherit Security policies. However, after configuring the device group hierarchy and attempting to push configurations, the team receives errors, and policy inheritance is not functioning as expected. What is the most likely cause of this issue?
An administrator wants to configure the Palo Alto Networks Windows User-D agent to map IP addresses to u: ‘The company uses four Microsoft Active ‘servers and two Microsoft Exchange servers, which can provide logs for login events. All six servers have IP addresses assigned from the following subnet: 192.168.28.32/27. The Microsoft Active Directory in 192.168.28.22/128, and the Microsoft Exchange reside in 192,168.28 48/28. What the 0 the User

