You have a Microsoft 365 £5 subscription.
You plan to implement Microsoft Priva Subject Rights Requests for Microsoft 365 data.
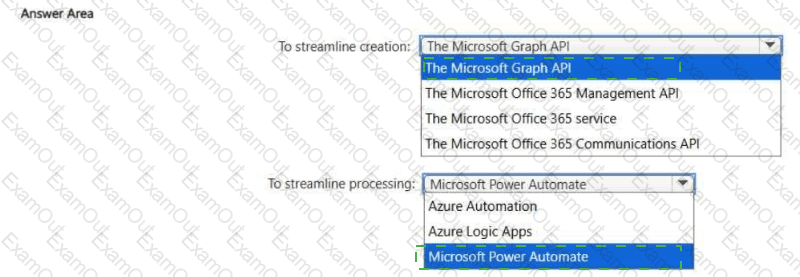
You need to streamline the creation and processing of subject rights requests. The solution must minimize development effort.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
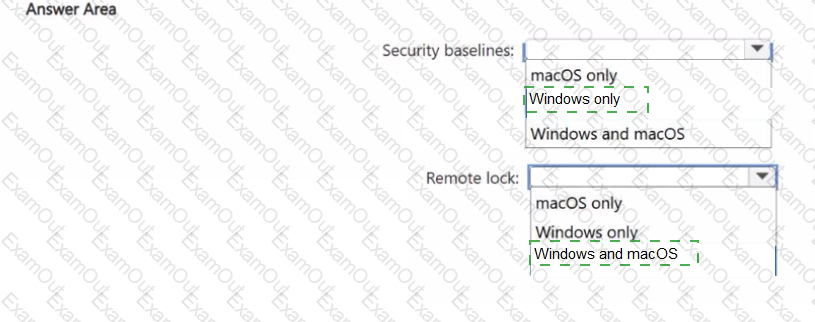
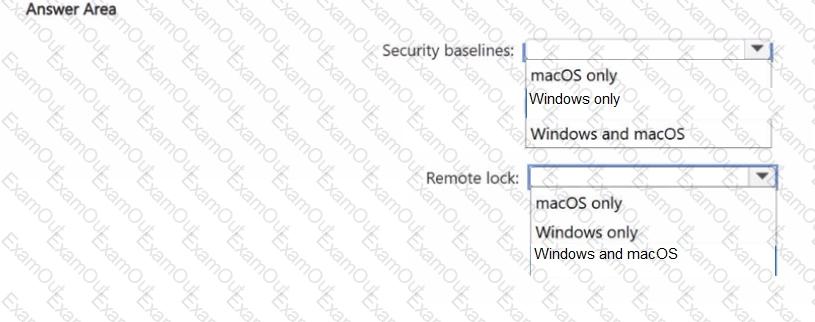
You have 500 Windows 11 devices and 200 macOS devices. The devices are managed by using Microsoft Intune and are subject to compliance policies.
You plan to deploy the following Intune features:
• Security baselines
• Remote lock of noncompliant devices
Which feature will be supported by each platform? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
A customer has a hybrid cloud infrastructure that contains a Microsoft 365 E5 subscription and an Azure subscription.
All the on-premises servers in the perimeter network are prevented from connecting directly to the internet.
The customer recently recovered from a ransomware attack.
The customer plans to deploy Microsoft Sentinel.
You need to recommend configurations to meet the following requirements:
• Ensure that the security operations team can access the security logs and the operation logs.
• Ensure that the IT operations team can access only the operations logs, including the event logs of the servers in the perimeter network.
Which two configurations can you include in the recommendation? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that contains 1,000 users. Each user is assigned a Microsoft 365 E5 license.
The subscription uses sensitivity labels to classify corporate documents. All the users have Windows 11 devices that are onboarded to Microsoft Defender for Endpoint and are configured to sync files to Microsoft OneDrive.
You need to prevent the users from uploading the documents from OneDrive to external websites.
What should you include in the solution?
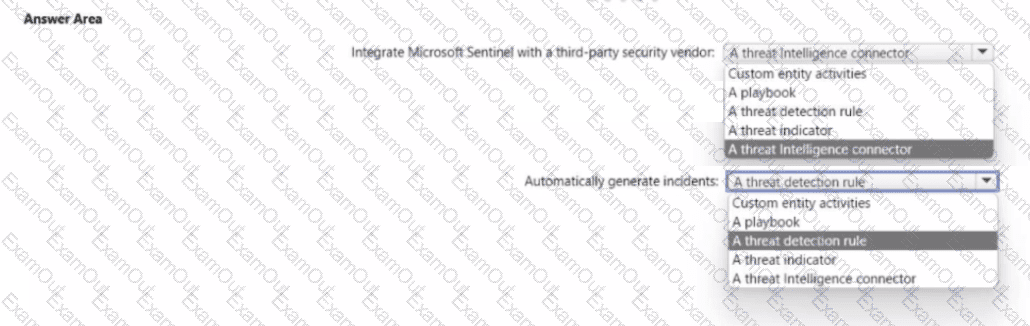
You have a Microsoft 365 subscription that is protected by using Microsoft 365 Defender
You are designing a security operations strategy that will use Microsoft Sentinel to monitor events from Microsoft 365 and Microsoft 365 Defender
You need to recommend a solution to meet the following requirements:
• Integrate Microsoft Sentinel with a third-party security vendor to access information about known malware
• Automatically generate incidents when the IP address of a command-and control server is detected in the events
What should you configure in Microsoft Sentinel to meet each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
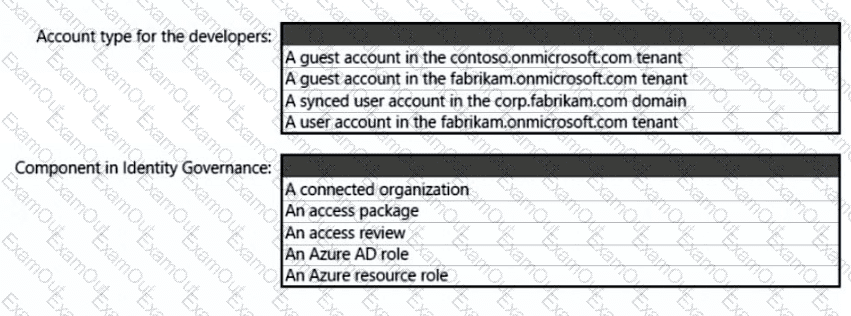
What should you create in Azure AD to meet the Contoso developer requirements?
You need to recommend a solution to secure the MedicalHistory data in the ClaimsDetail table. The solution must meet the Contoso developer requirements.
What should you include in the recommendation?
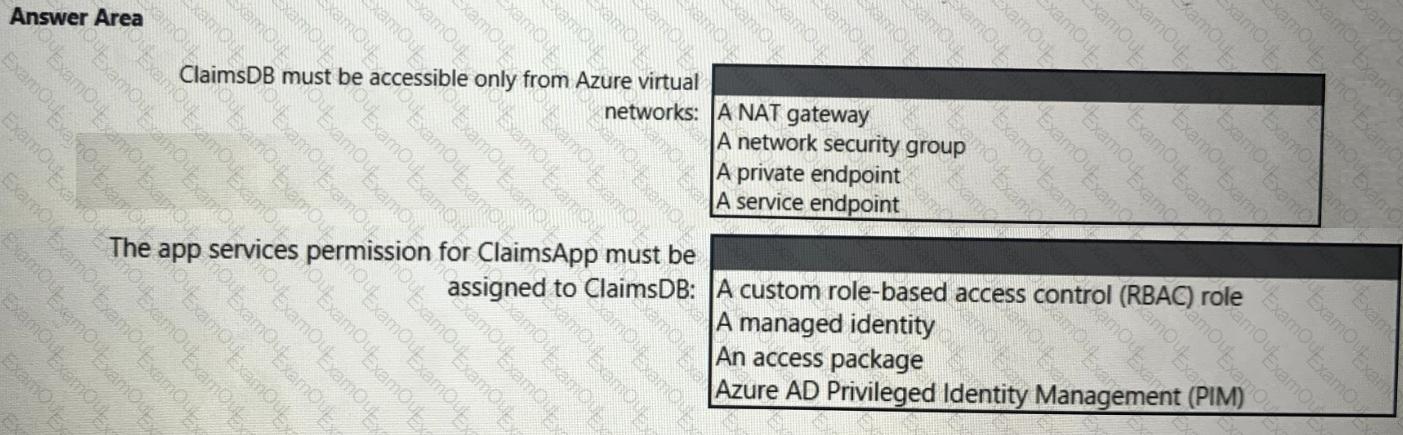
You need to recommend a solution to meet the requirements for connections to ClaimsDB.
What should you recommend using for each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to recommend a solution to scan the application code. The solution must meet the application development requirements. What should you include in the recommendation?
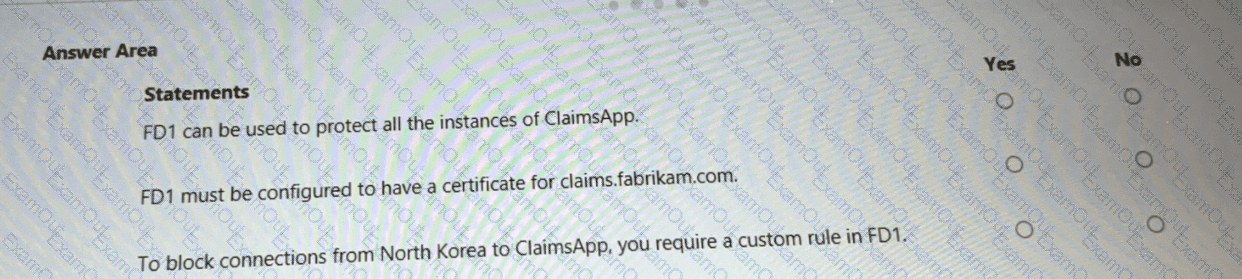
You are evaluating the security of ClaimsApp.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE; Each correct selection is worth one point.