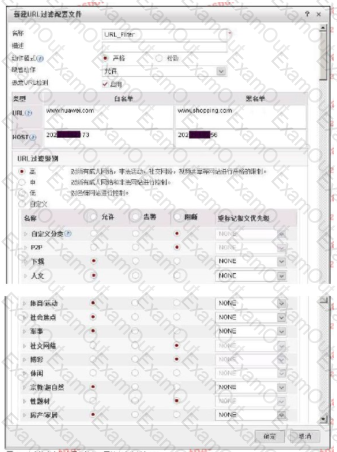
The following figure shows the configuration of the URL filtering configuration file. Regarding the configuration, which of the following statements is correct?
Huawei USG6000 products can scan and process certain file transfer protocols for viruses, but which of the following protocols is not included?
Which of the following options describes the IntelliSense engine IAE incorrectly?
Regarding firewall and IDS, which of the following statements is correct?
Which of the following is the correct configuration idea for the anti-virus strategy?
1. Load the feature library
2. Configure security policy and reference AV Profile
3. Apply and activate the license
4. Configure AV Profile
5. Submit
For the URL is htpt://www.abcd. com:8080/news/education. aspx?name=tom &age=20, which option is path?
Server Fault information collection tool Server Collector, which of the following does collected information items not include?
For the description of the principles of HTTP Flood and HTTPS Flood blow defense, which of the following options are correct? (multiple choice)
Regarding the anti-spam response code, which of the following statements is wrong?
Which way can NAC Agent upgrade package be deployed?

