In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
Which of the following statements is correct about characteristics of a firewall?
What are the correct entries in the following description of firewall security zones?
The following description of digital certificates, which one is wrong
The following description of asymmetric encryption algorithms, which item is wrong?
An enterprise wants to build a server system and requires the following functions: 1. The enterprise needs to have its own dedicated mailbox, and the sending and receiving of emails needs to go through the enterprise's server; 2. The server must provide file transfer and access services. Users in different departments of the enterprise provide accounts with different permissions: 3. When the enterprise accesses the internal webpage of the enterprise, the enterprise can directly enter the domain name in the browser to access. To meet the above requirements, which of the following servers do enterprises need to deploy? ( )*
What is correct in the following description of Security Alliance in IPSec?
There are two ways to set up an IPSec SA
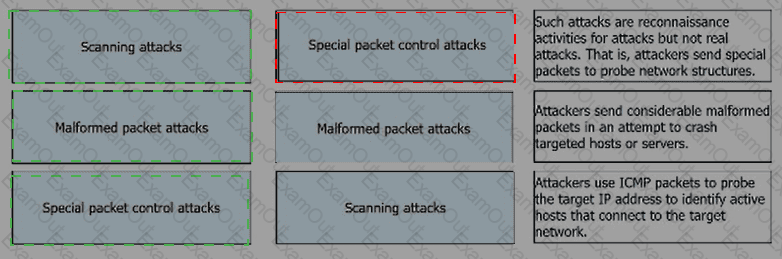
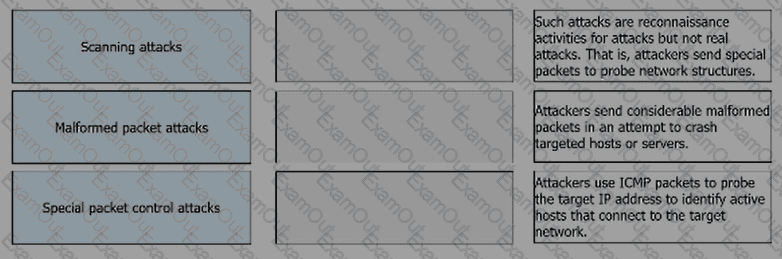
Match the following single-packet attack types with their corresponding descriptions.
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?