Which of the following zones is not the firewall default security zone?
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
The network environment is becoming more and more complex, and network security incidents occur frequently. While accelerating the construction of informatization, enterprises must not only resist external attacks, but also prevent internal management personnel from being involved in data leakage and operation and maintenance accidents due to operational errors and other issues. Which of the following options might reduce operational risk?
Which of the following protocols is a multichannel protocol?
Please match the following information security risks to information security incidents one by one.[fill in the blank]*
physical security risk Enterprise server permissions are loosely set
Information Security Management Risk Infected Panda Burning Incense
Information Access Risk Fire destroyed equipment in computer room
application risk Talk to people about leaking company secrets
Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
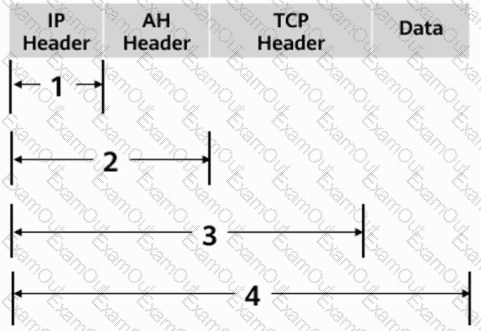
As shown in the figure, what is the range of the AH protocol authentication range in transmission mode?
ARP man-in-the-middle attacks are a type of spoofing attack technique.
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.

