Refer to the exhibit, and then answer the question below.
Which host is rogue?
When FortiNAC is managing FortiGate VPN users, why is an endpoint compliance policy necessary?
Refer to the exhibit.
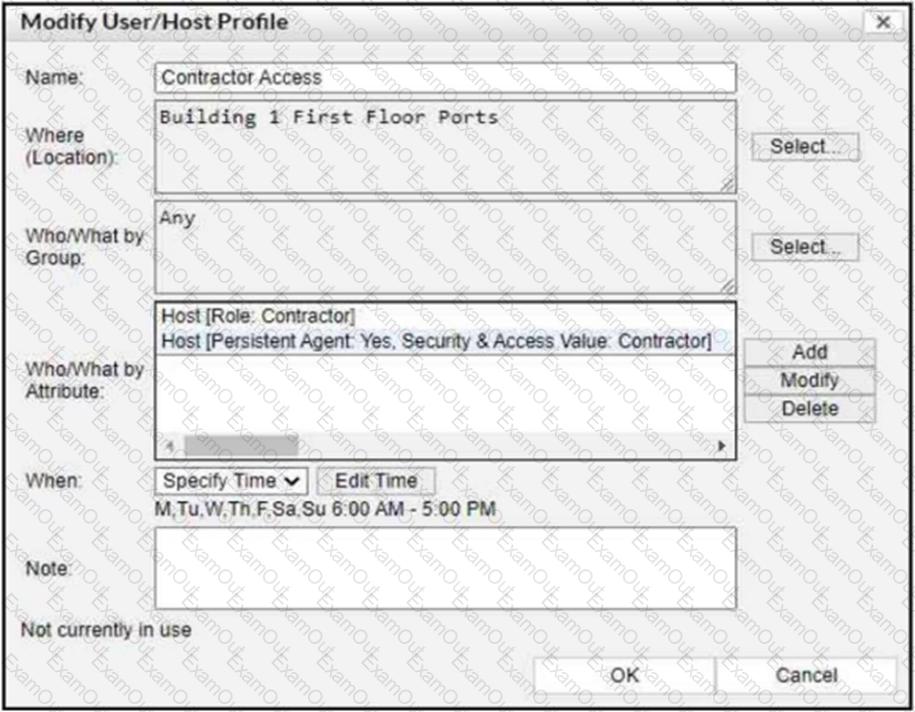
If a host is connected to a port in the Building 1 First Floor Ports group, what must also be true to match this user/host profile?
What capability do logical networks provide?

