An administrator must enable direct communication between multiple spokes in a company ' s network. Each spoke has more than one internet connection.
The requirement is for the spokes to connect directly without passing through the hub, and for the links to automatically switch to the best available connection.
How can this automatic detection and optimal link utilization between spokes be achieved?
Refer to the exhibit, which shows an enterprise network connected to an internet service provider.
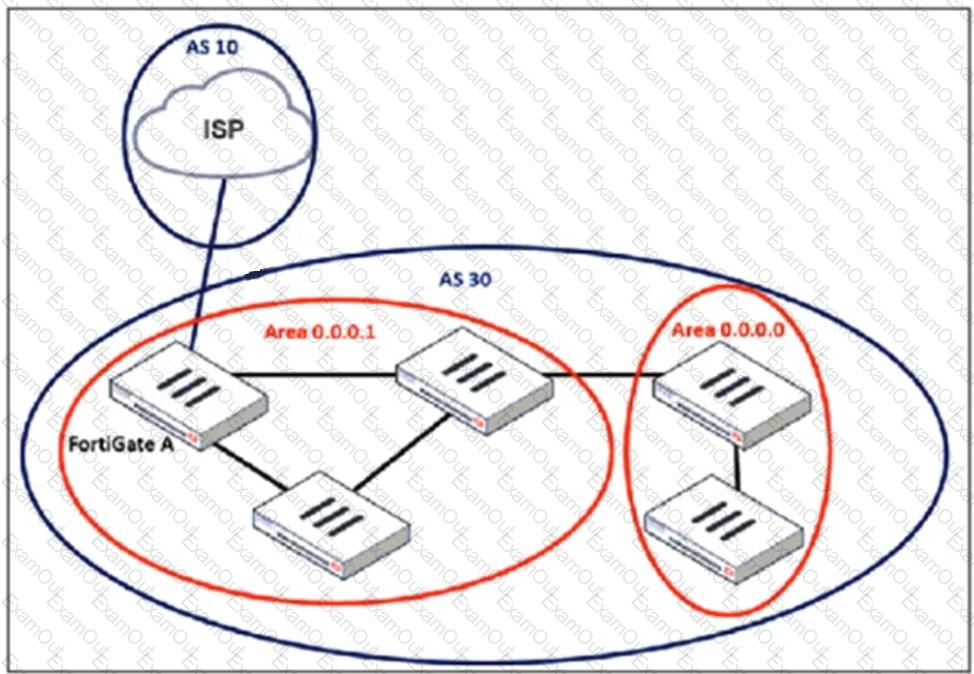
An administrator must configure a loopback as a BGP source to connect to the ISP.
Which two commands are required to establish the connection? (Choose two.)
A FortiGate device using unified threat management (UTM) profiles is reaching resource limits, and you expect traffic in your enterprise network to increase. You received an additional FortiGate of the same model.
Which two options should you consider using to integrate the additional FortiGate into your enterprise network? (Choose two.)
Refer to the exhibit.
An HA configuration of an active-active (A-A) cluster with the same HA uptime is shown. You want HQ-NGFW-2 to handle the Core2 VDOM traffic. Which modification must you make to achieve this outcome? (Choose one answer)
What should be configured to provide hardware-accelerated inter-VDOM traffic?
Refer to the exhibit, which shows the packet capture output of a three-way handshake between FortiGate and FortiManager Cloud.
What two conclusions can you draw from the exhibit? (Choose two.)
Which two statements about the LAN interface connection are correct?
Refer to the exhibit, which shows an enterprise network connected to an internet service provider.
The administrator must configure the BGP section of FortiGate A to give internet access to the enterprise network.
Which command must the administrator use to establish a connection with the internet service provider?
Refer to the exhibit.
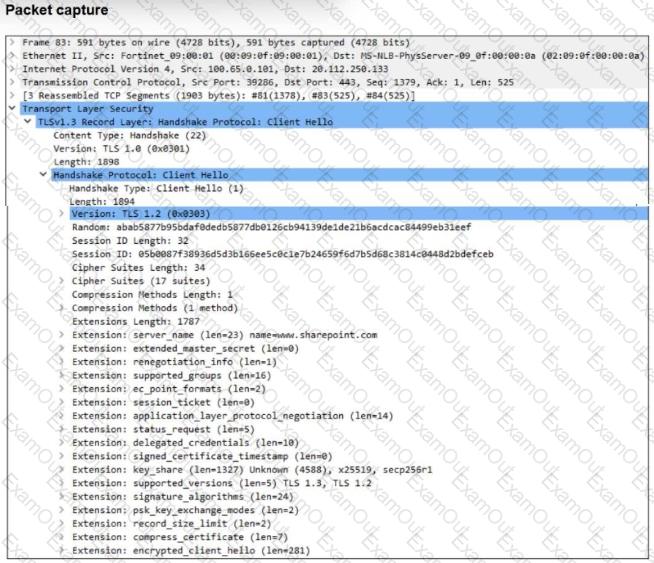
The packet capture output of a client hello message is shown.
You are updating a firewall policy that includes SSL certificate inspection. You are capturing packets from the traffic passing through this firewall policy.
Which two statements about the packet capture are correct? (Choose two.)
Refer to the exhibit.
An administrator is deploying a hub and spokes network and using OSPF as dynamic protocol.
Which configuration is mandatory for neighbor adjacency?

