Which field in a DNS Request event points to the responsible process?
Refer to the image. Which query will show file execution from a suspicious directory across all hosts?
You suspect one of your endpoint host systems may have a vulnerable BIOS version. Which Investigate Dashboard will confirm vulnerability information such as the type and timeline?
Which hunting query's results could indicate that an adversary is performing reconnaissance from a specific host?
Refer to the exhibit.
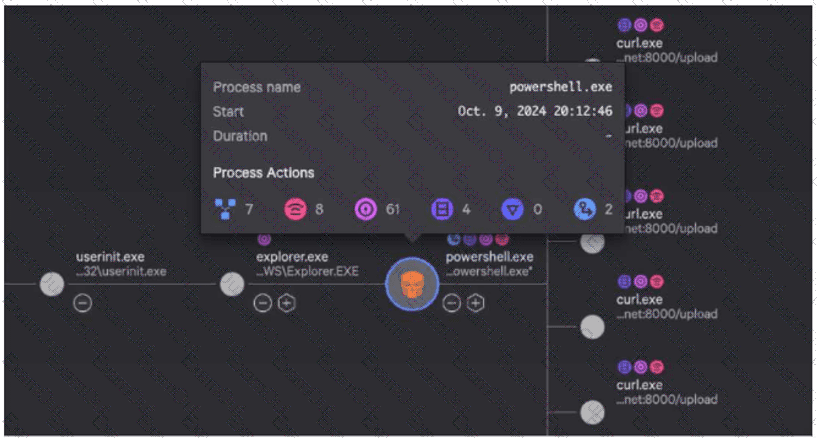
While investigating a process tree, you hover over a malicious powershell.exe process. What is the correct sequence of Process Actions?
While performing triage on a detection, you notice an event with the name SyntheticProcessRollup2. What conclusion can be made about this event?
During an investigation, you discover a Falcon host connecting from a country outside of those you normally do business with. Which built-in report would display Falcon hosts connecting from that country?
While performing a threat hunt in your environment, you decide to identify rare occurrences of user agent strings over the past 30 days. Which query will highlight those results using CQL?
Refer to the image.
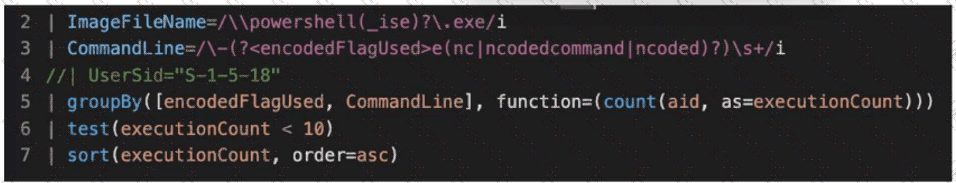
What line item of the query is used to perform outlier analysis?
You've written a complex query within Advanced Event Search that is returning millions of events, making it difficult to threat hunt for particular file metadata. Which option would decrease query time and remove values that are not of interest?

