Which of the following vulnerabilities is associated with installing software outside of a manufacturer’s approved software repository?
Which of the following activities are associated with vulnerability management? (Select two).
A security analyst reviews domain activity logs and notices the following:
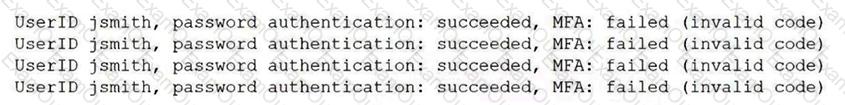
Which of the following is the best explanation for what the security analyst has discovered?
Which of the following would be best suited for constantly changing environments?
The security operations center is researching an event concerning a suspicious IP address A security analyst looks at the following event logs and discovers that a significant portion of the user accounts have experienced faded log-In attempts when authenticating from the same IP address:
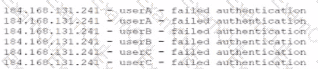
Which of the following most likely describes attack that took place?
A software developer released a new application and is distributing application files via the developer’s website. Which of the following should the developer post on the website to allow users to verify the integrity of the downloaded files?
A systems administrator receives a text message from an unknown number claiming to be the Chief Executive Officer of the company. The message states an emergency situation requires a password reset. Which of the following threat vectors is being used?
A company discovers suspicious transactions that were entered into the company's database and attached to a user account that was created as a trap for malicious activity. Which of the following is the user account an example of?
A network manager wants to protect the company's VPN by implementing multifactor authentication that uses:
. Something you know
. Something you have
. Something you are
Which of the following would accomplish the manager's goal?
Which of the following should be used to ensure that a new software release has not been modified before reaching the user?
A network administrator deploys an FDE solution on all end user workstations. Which of the following data protection strategies does this describe?
A security team receives reports about high latency and complete network unavailability throughout most of the office building. Flow logs from the campus switches show high traffic on TCP 445. Which of the following is most likely the root cause of this incident?
Which of the following is an example of a false negative vulnerability detection in a scan report?
An organization is looking to optimize its environment and reduce the number of patches necessary for operating systems. Which of the following will best help to achieve this objective?
A company plans to secure its systems by:
Preventing users from sending sensitive data over corporate email
Restricting access to potentially harmful websites
Which of the following features should the company set up? (Select two).

