Which of the following is a difference between EOL and EOS?
A security administrator is creating a new firewall object for a device with IP address 192.168.100.1/25. However, the firewall software only uses dotted decimal notation in configuration fields. Which of the following is the correct subnet mask to use?
A company security policy requires all network traffic from remote employees ' corporate laptops to use the company’s VPN. Which of the following network access methods best describes this scenario?
Which of the following VPN configurations forces a remote user to access internet resources through the corporate network?
A network administrator is managing network traffic so that classified services and applications are prioritized. Which of the following technologies should the network administrator use?
A network engineer is designing an internal network that needs to support both IPv4 and IPv6 routing. Which of the following routing protocols is capable of supporting both IPv4 and IPv6?
An administrator wants to find the top destination for traffic across the infrastructure on a specific day. Which of the following should the administrator use?
Which of the following does a hash provide?
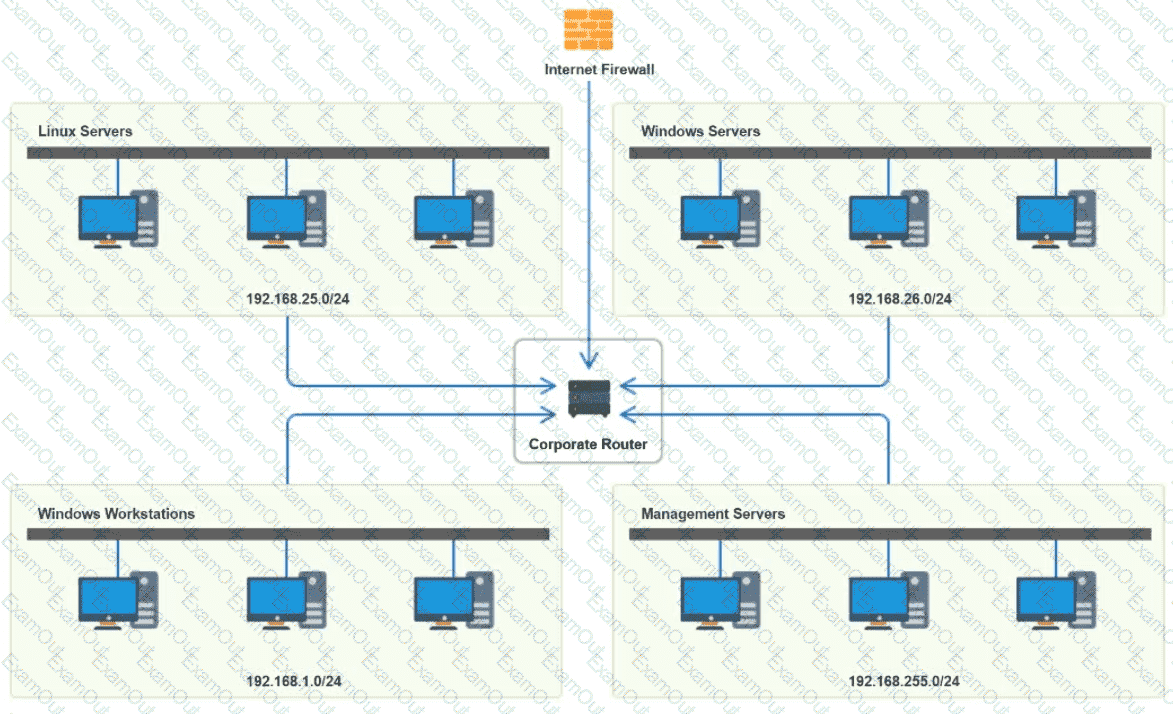
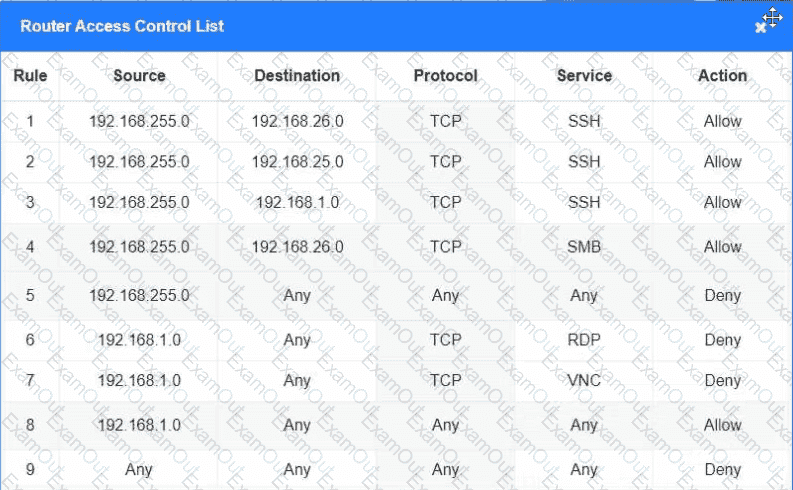
You have been tasked with implementing an ACL on the router that will:
1. Permit the most commonly used secure remote access technologies from the management network to all other local network segments
2. Ensure the user subnet cannot use the most commonly used remote access technologies in the Linux and Windows Server segments.
3. Prohibit any traffic that has not been specifically allowed.
INSTRUCTIONS
Use the drop-downs to complete the ACL
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A secure communication link needs to be configured between data centers via the internet. The data centers are located in different regions. Which of the following is the best protocol for the network administrator to use?
An organizatin is struggling to get effective coverage using the wireless network. The organization wants to implement a solution that will allow for continous connectivity anywhere in the facility. Which of the following should the network administ rator suggest to ensure the best coverage?
Which of the following ports is used for secure email?
Newly crimped 26ft (8m) STP Cat 6 patch cables were recently installed in one room to replace cables that were damaged by a vacuum cleaner. Now, users in that room are unable to connect to the network. A network technician tests the existing cables first. The 177ft (54m) cable that runs from the core switch to the access switch on the floor is working, as is the 115ft (35m) cable run from the access switch to the wall jack in the office. Which of the following is the most likely reason the users cannot connect to the network?
While troubleshooting a VoIP handset connection, a technician ' s laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch. Which of the following should the technician use to determine the switch and port?
A firewall administrator is mapping a server ' s internal IP address to an external IP address for public use. Which of the following is the name of this function?

 A screenshot of a computer screen AI-generated content may be incorrect.
A screenshot of a computer screen AI-generated content may be incorrect.