A firewall receives traffic on port 80 and forwards it to an internal server on port 88. Which of the following technologies is being leveraged?
A company implements a video streaming solution that will play on all computers that have joined a particular group, but router ACLs are blocking the traffic. Which of the following is the most appropriate IP address that will be allowed in the ACL?
A network administrator deploys several new desk phones and workstation cubicles. Each cubicle has one assigned switchport. The administrator runs the following commands:
nginx
CopyEdit
switchport mode access
switchport voice vlan 69
With which of the following VLANs will the workstation traffic be tagged?
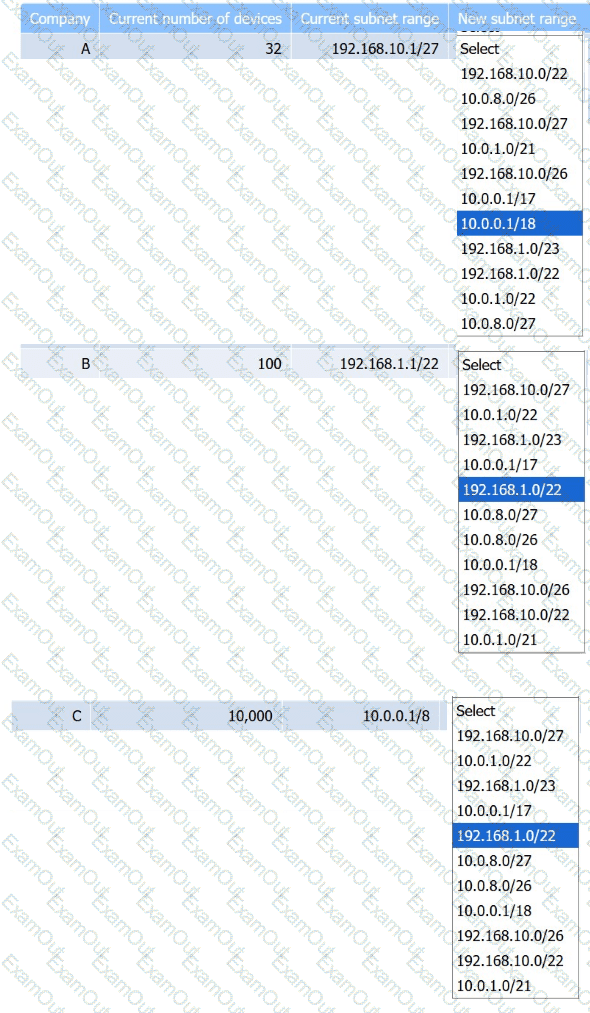
Company C is acquiring Company A and Company B. Company C needs to merge all
three networks into one Class B network. Additionally, the network capacity of each company needs to grow by 20%. Company C also requires segmentation of Company A and Company B to account for unknown security vulnerabilities within each.
Instructions:
Select the correct subnet range to meet Company C ' s requirements.
Which of the following cloud platform technology characteristics would a quantum computing host most likely prioritize?
Before using a guest network, an administrator requires users to accept the terms of use Which of the following is the best way to accomplish this goal?
Which of the following impacts the availability of a web-based customer portal?
A network administrator recently updated configurations on a Layer 3 switch. Following the updates, users report being unable to reach a specific file server. Which of the following is the most likely cause?
Which of the following objectives does an evil twin achieve?
A company has been added to an unapproved list because of spam. The network administrator confirmed that a workstation was infected by malware. Which of the following processes did the administrator use to identify the root cause?
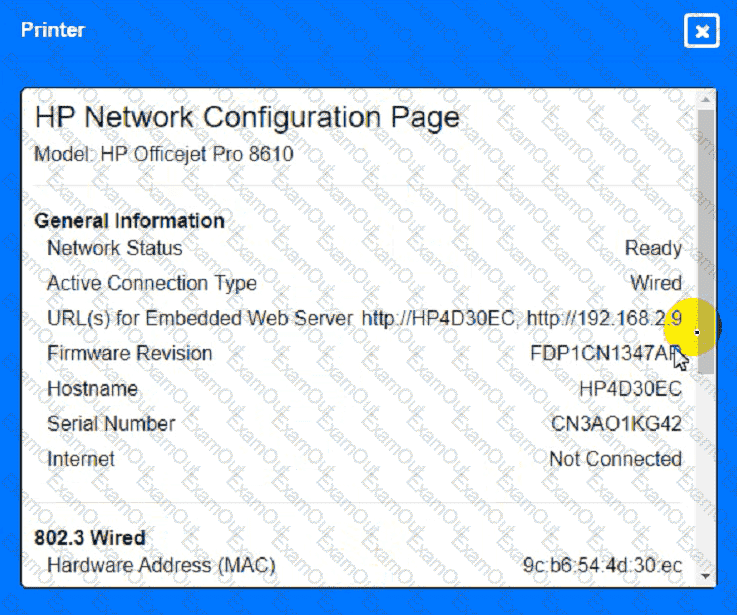
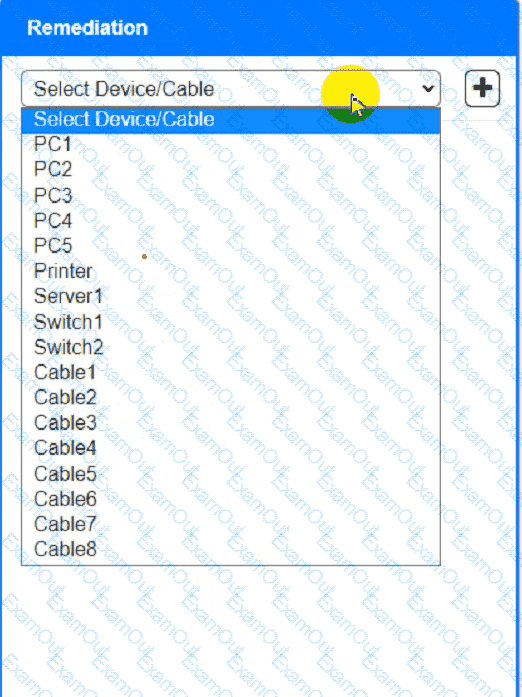
A network technician needs to resolve some issues with a customer ' s SOHO network.
The customer reports that some of the devices are not connecting to the network, while others appear to work as intended.
INSTRUCTIONS
Troubleshoot all the network components and review the cable test results by Clicking on each device and cable.
Diagnose the appropriate component(s) by identifying any components with a problem and recommend a solution to correct each problem.
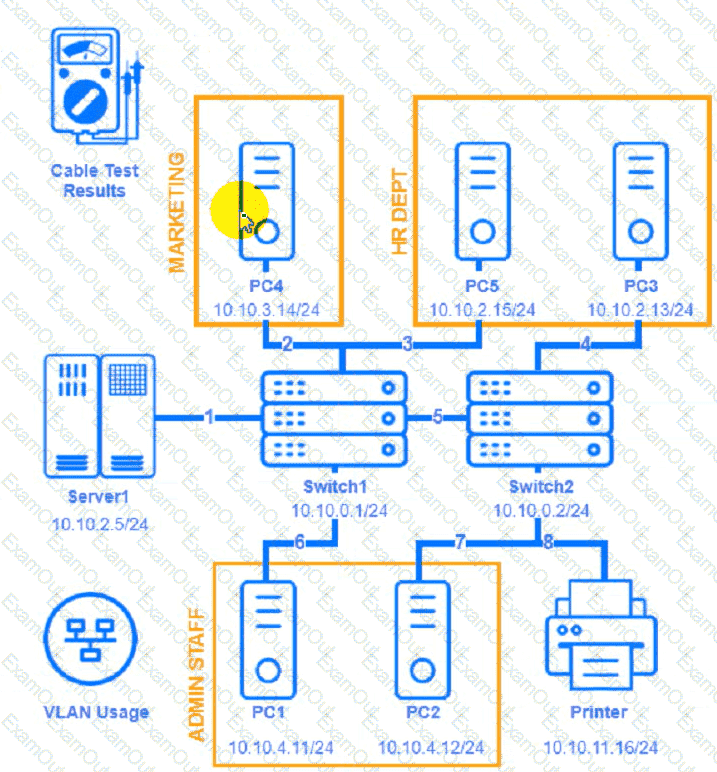

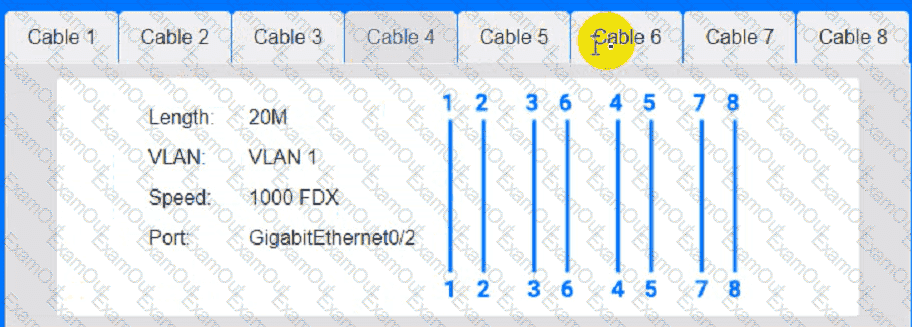
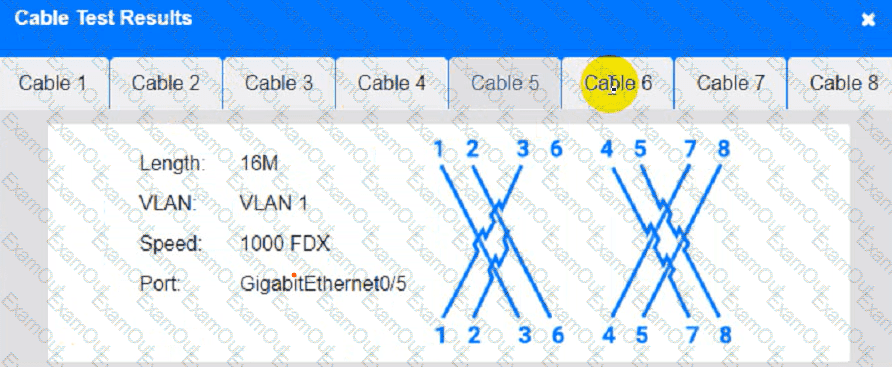
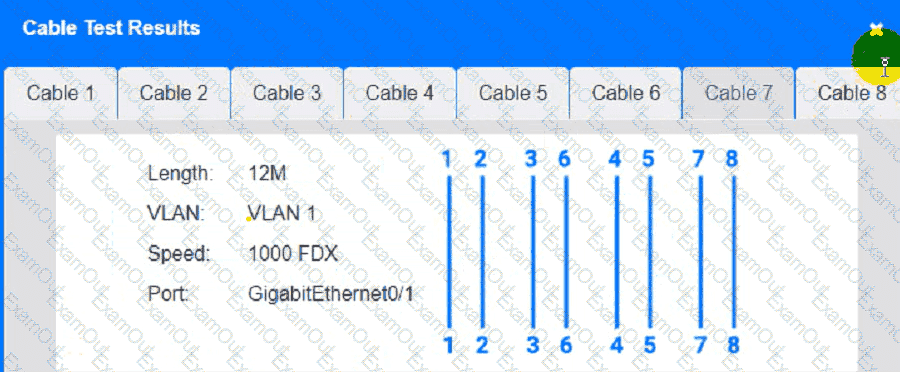
Cable Test Results:
Cable 1:
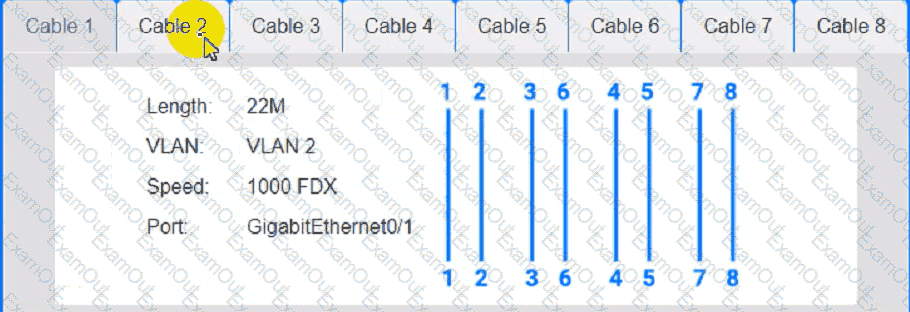
Cable 2:
Cable 3:
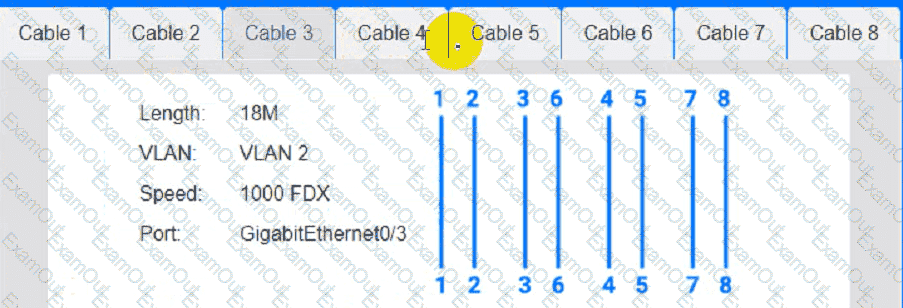
Cable 4:
A junior network administrator gets a text message from a number posing as the domain registrar of the firm. The administrator is tricked into providing global administrator credentials. Which of the following attacks is taking place?
Which of the following standards enables the use of an enterprise authentication for network access control?
Which of the following can be implemented to add an additional layer of security between a corporate network and network management interfaces?
A user tries to visit a website, but instead of the intended site, the page displays vmw.cba.com. Which of the following should be done to reach the correct website?


