A secretary receives an email from the CEO requesting immediate vendor payment. Later, the CEO says they never sent it. Which social engineering tactic is this?
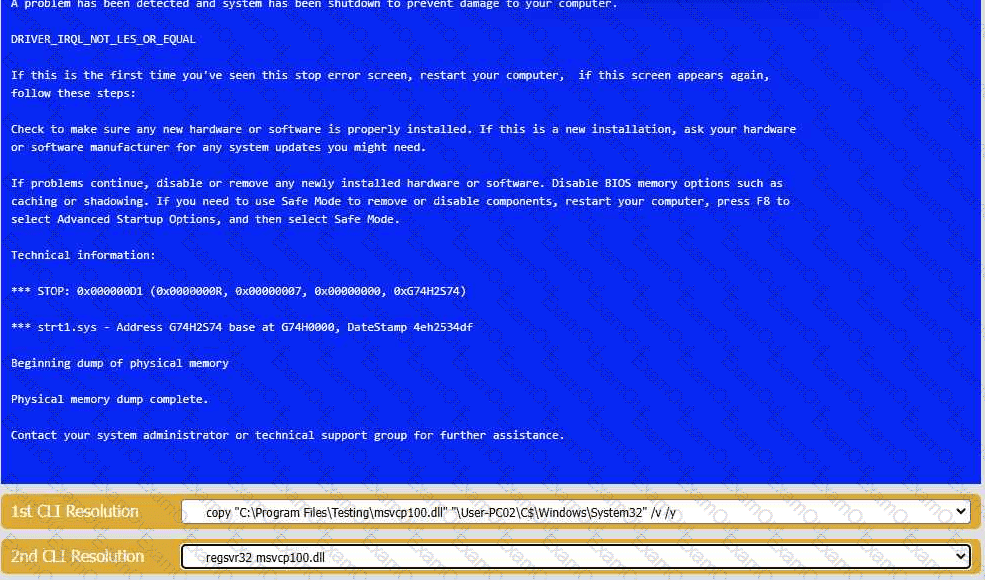
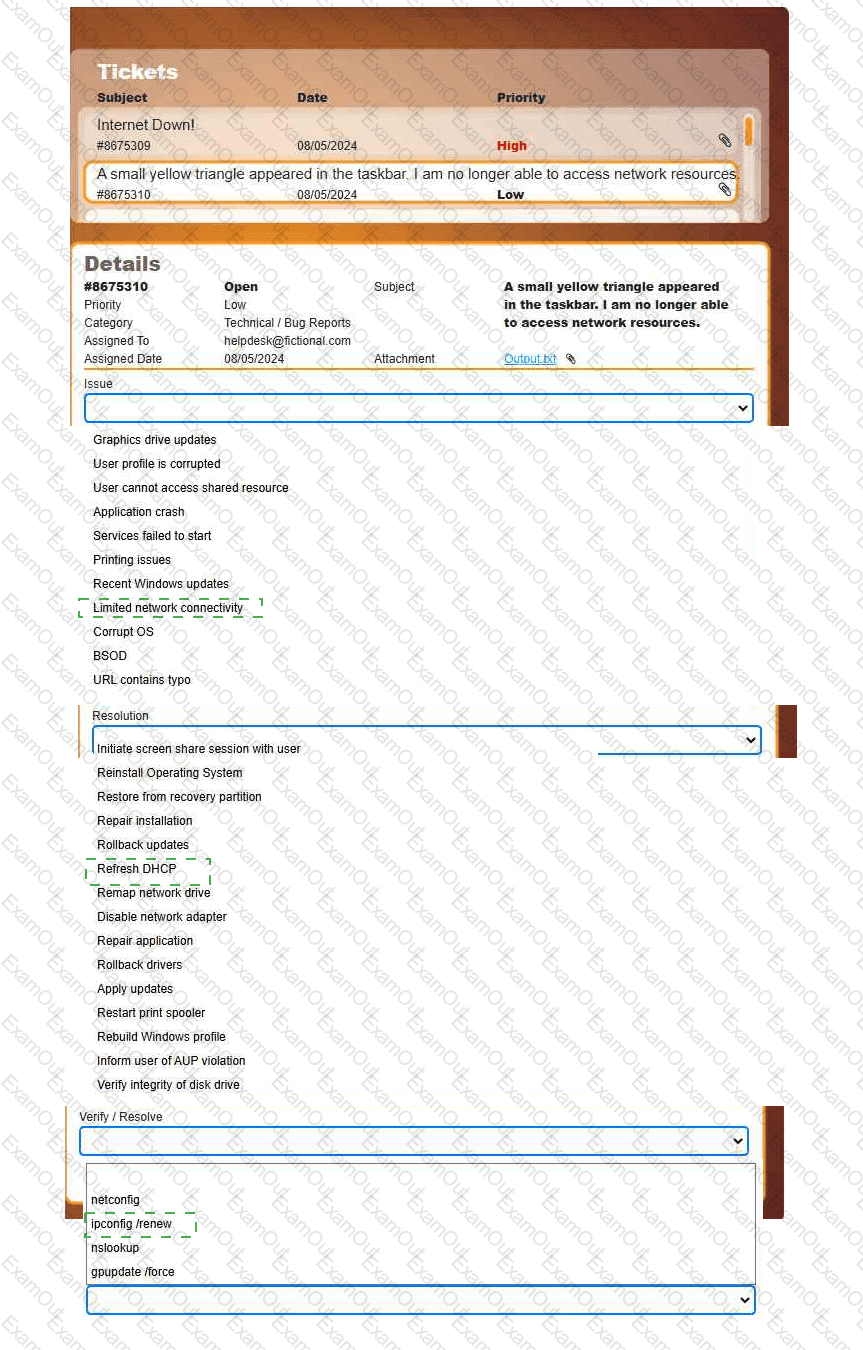
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
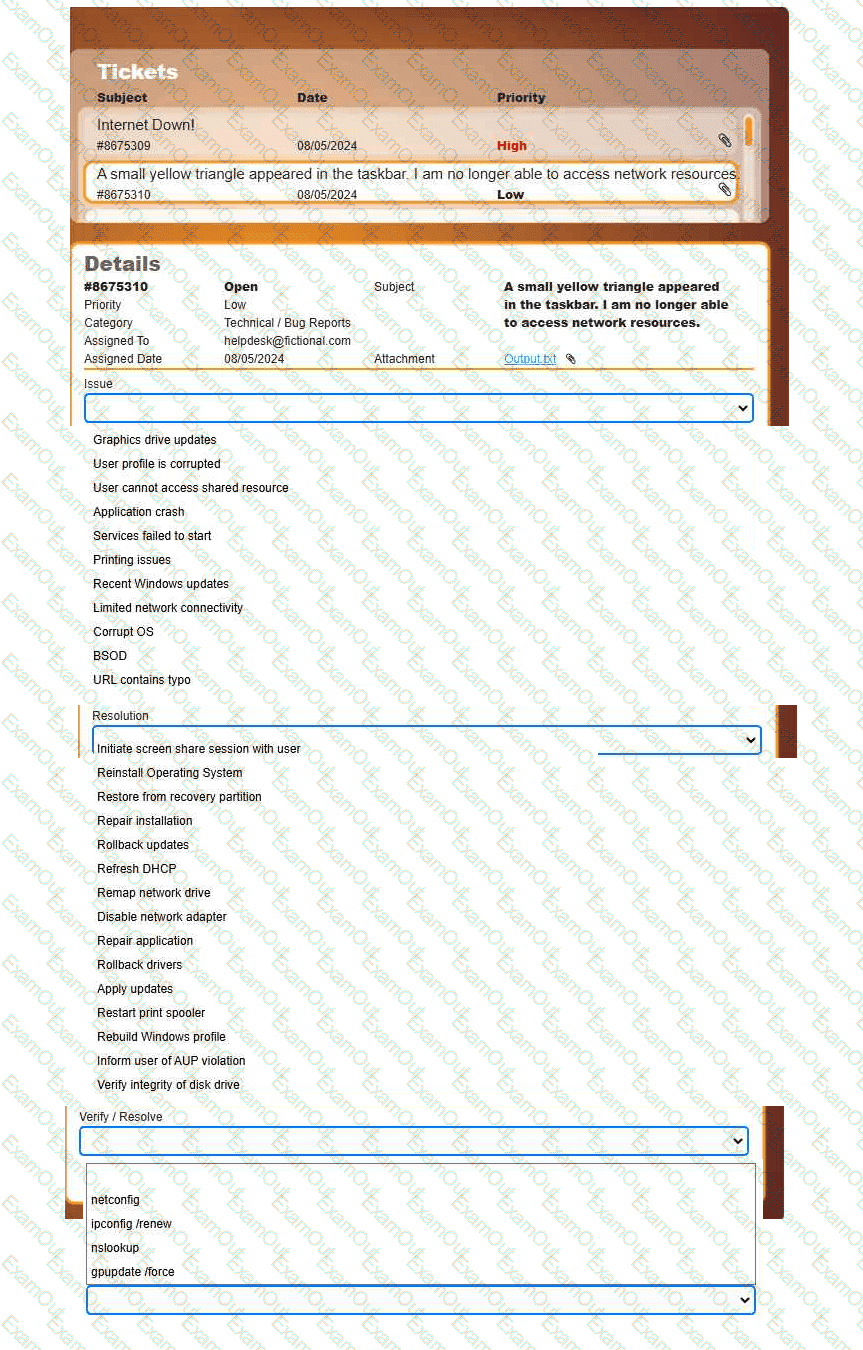
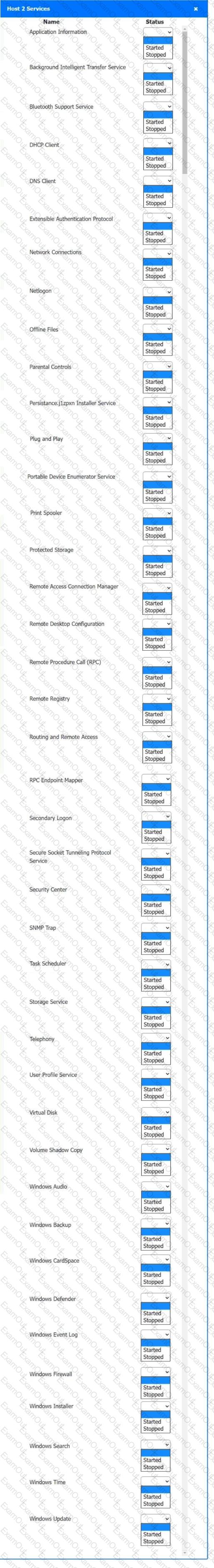
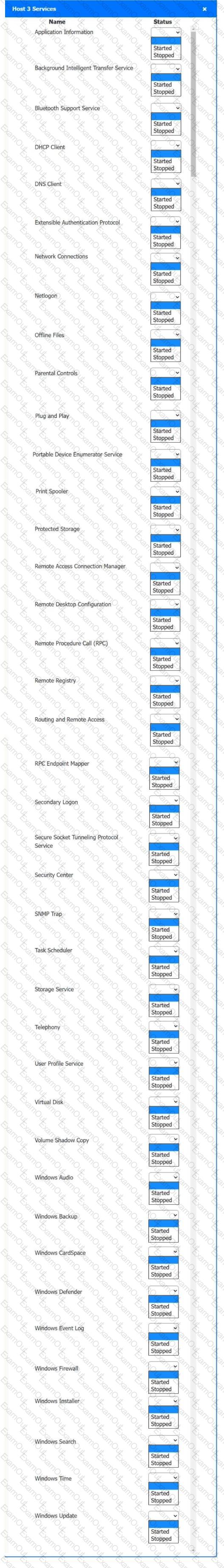
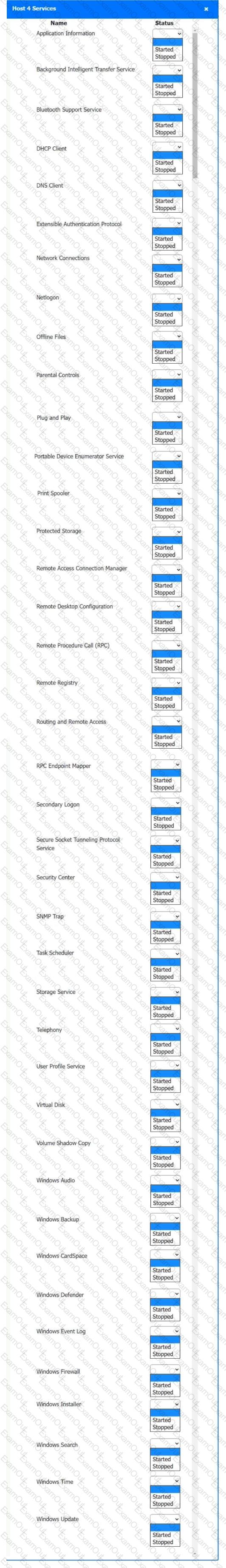
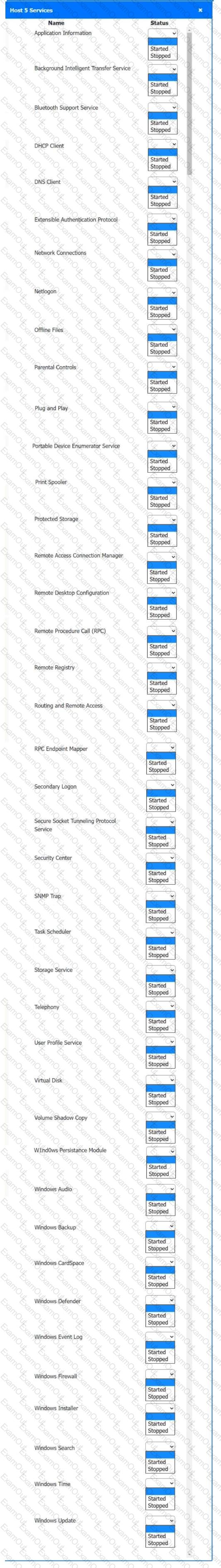
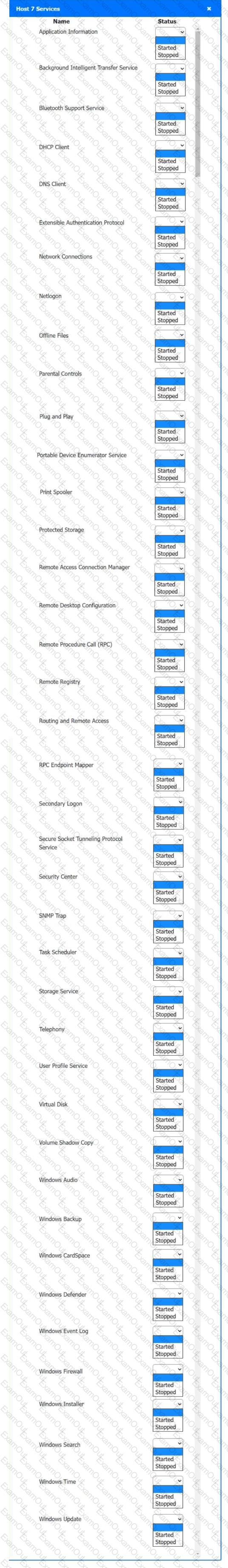
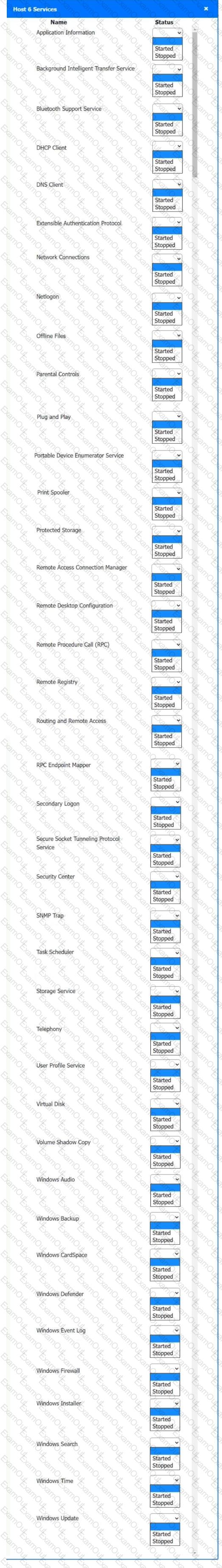
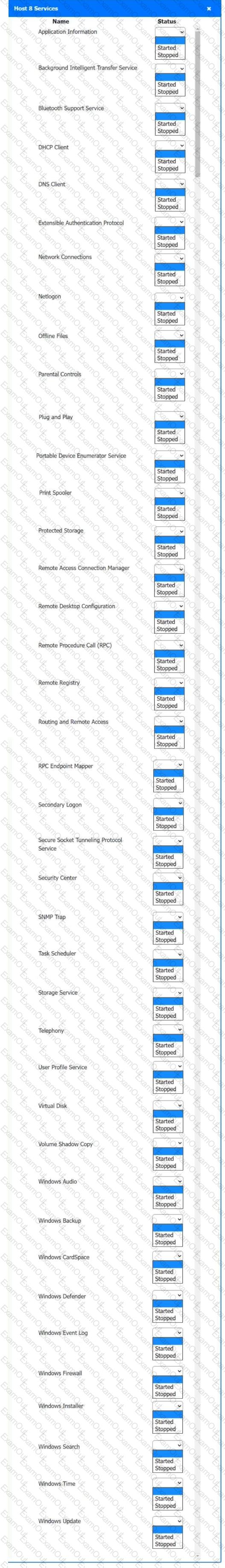
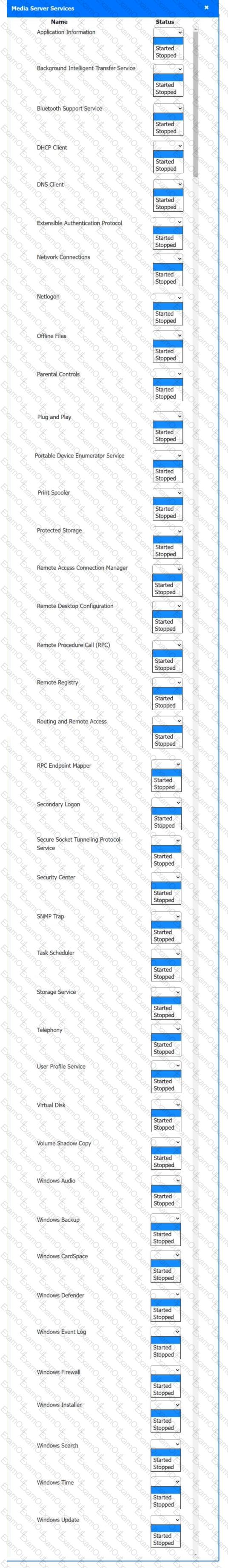
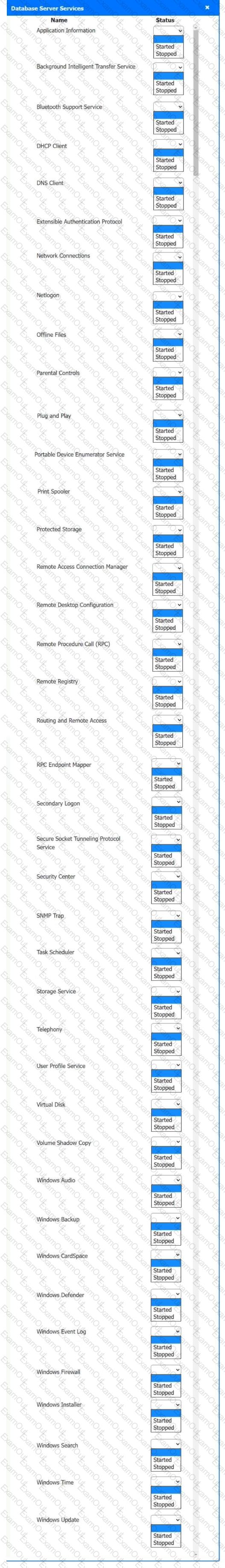
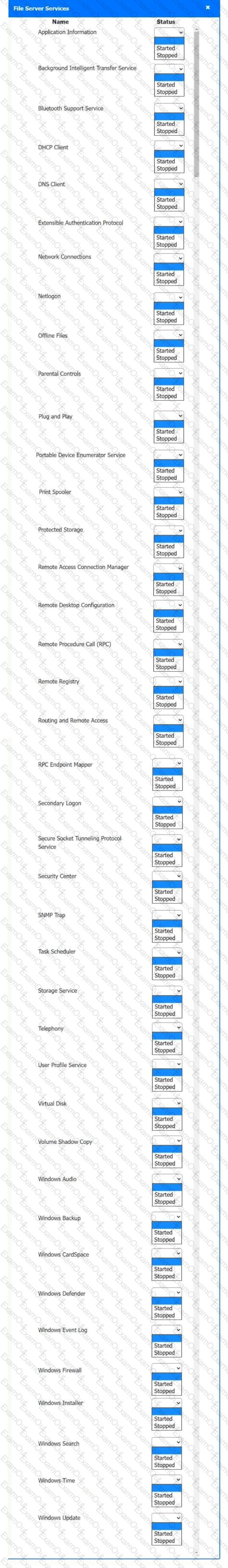
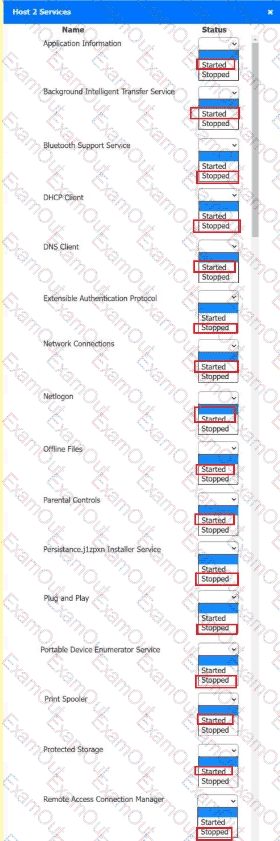
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
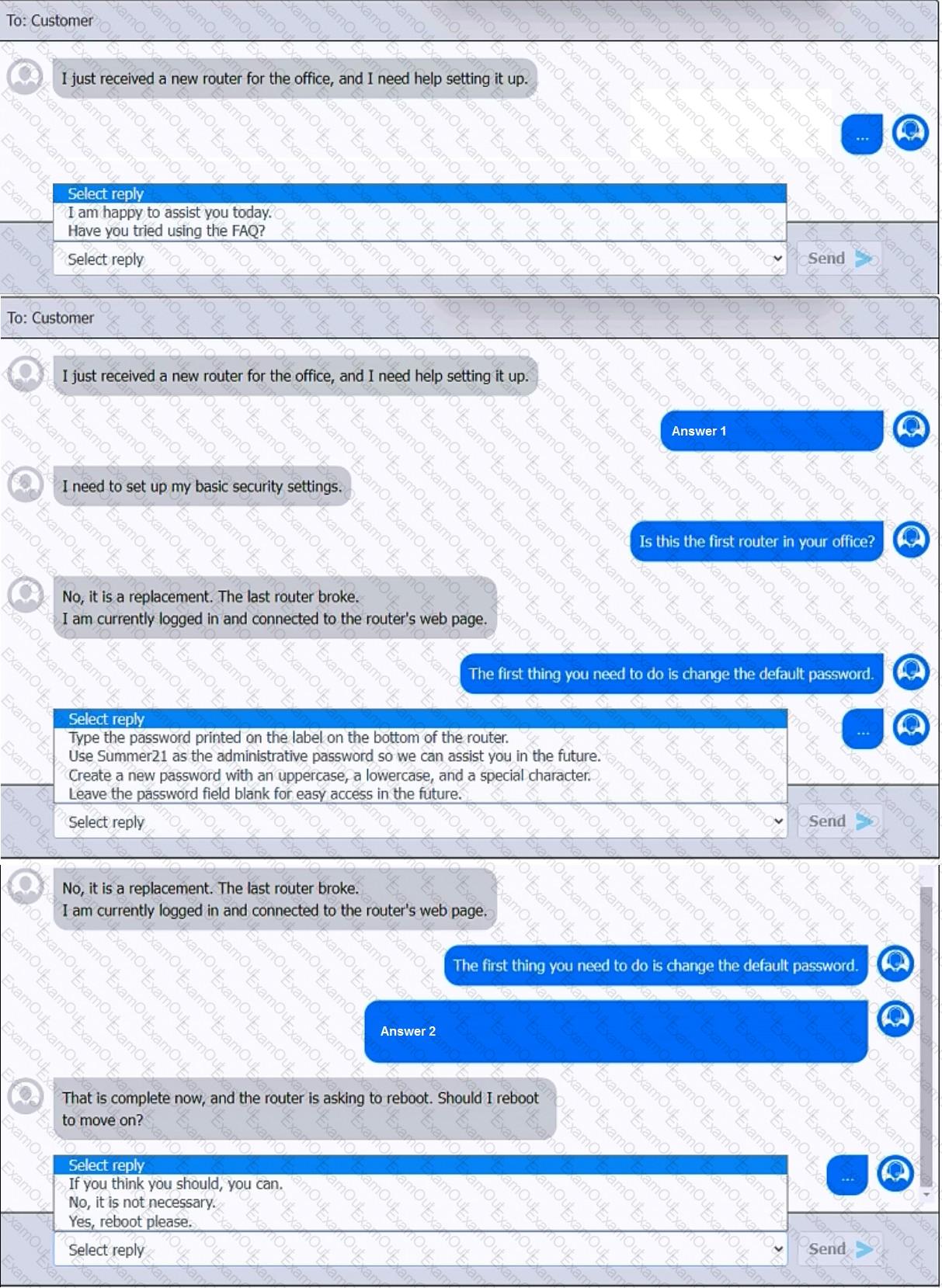
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
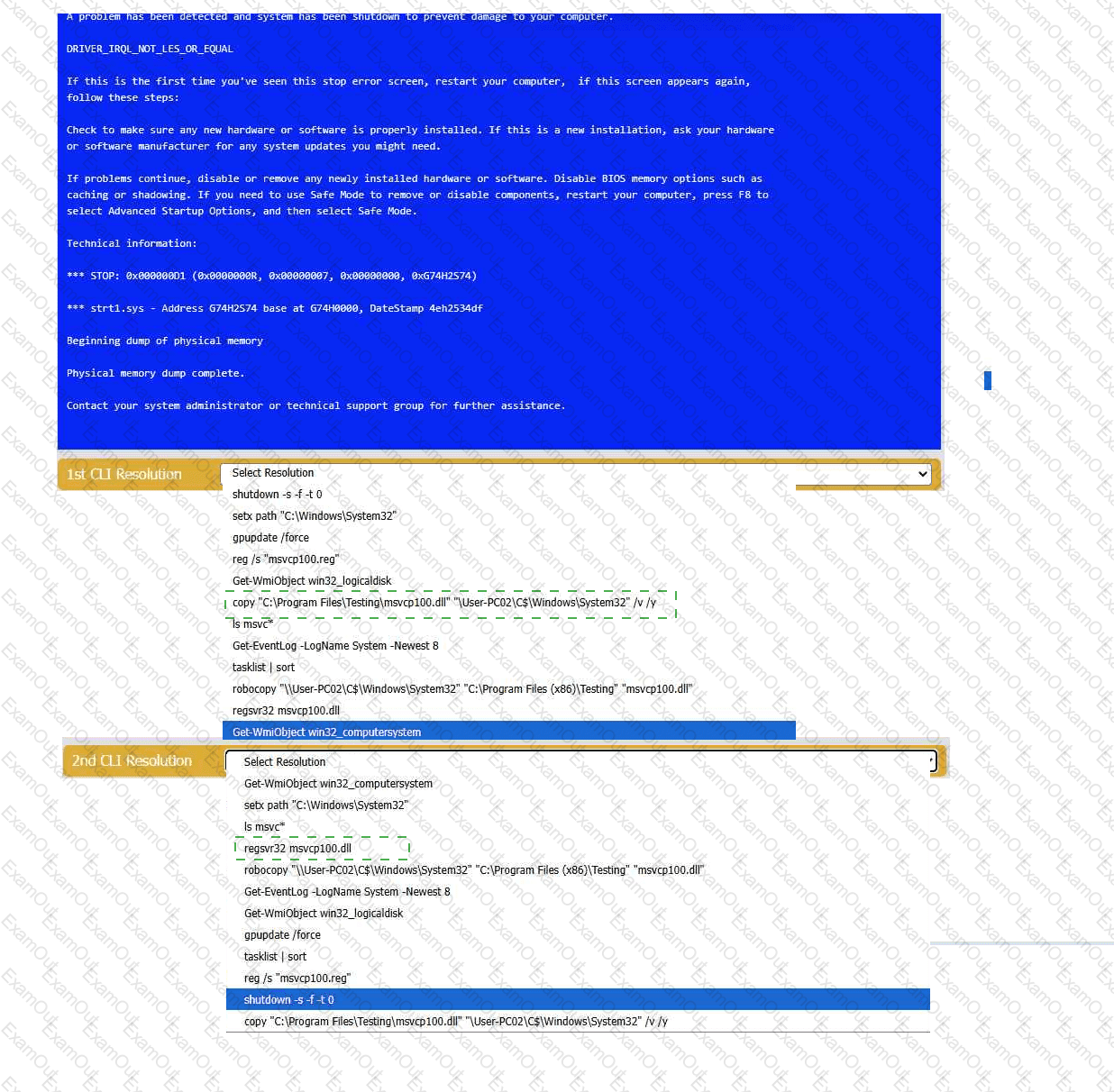
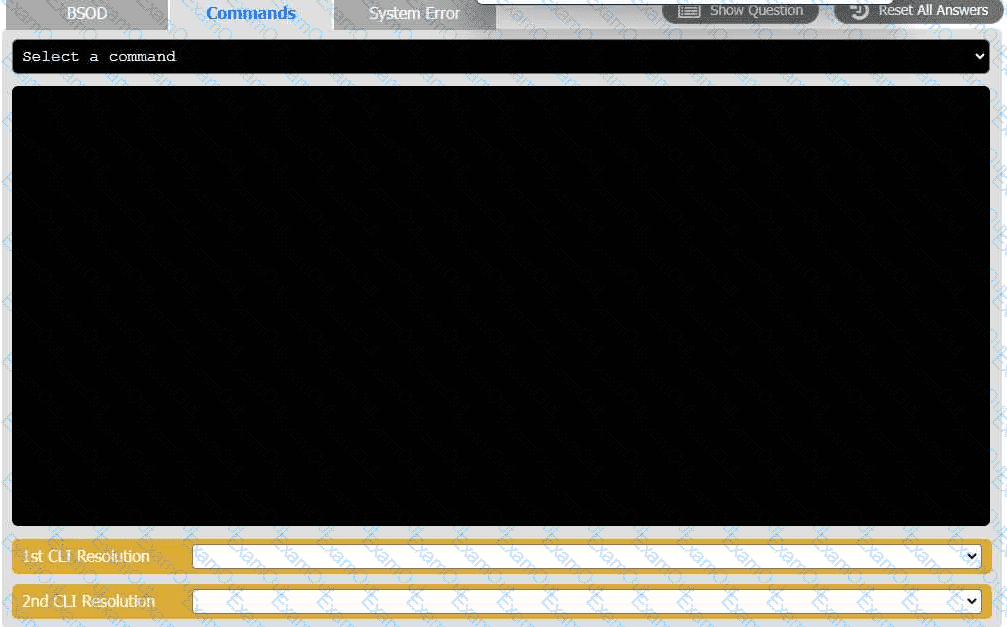
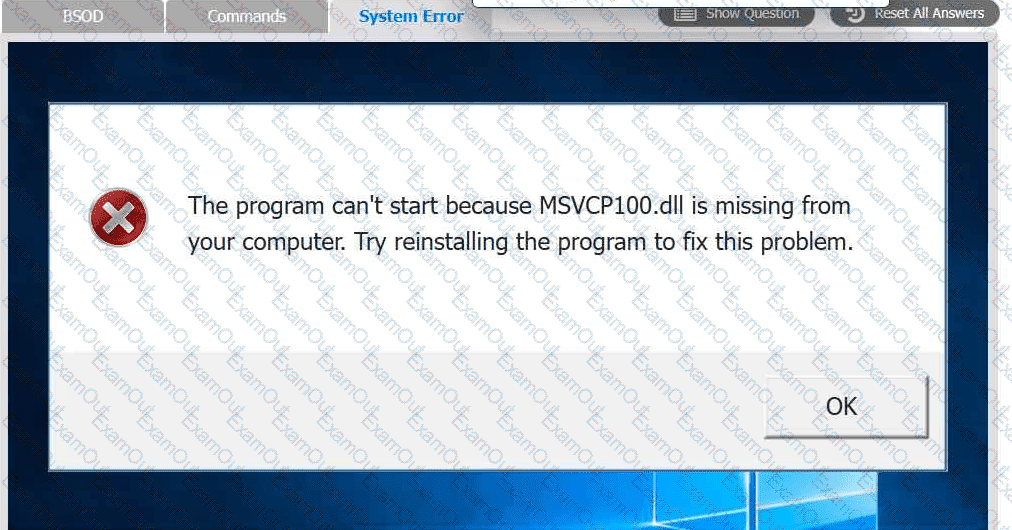
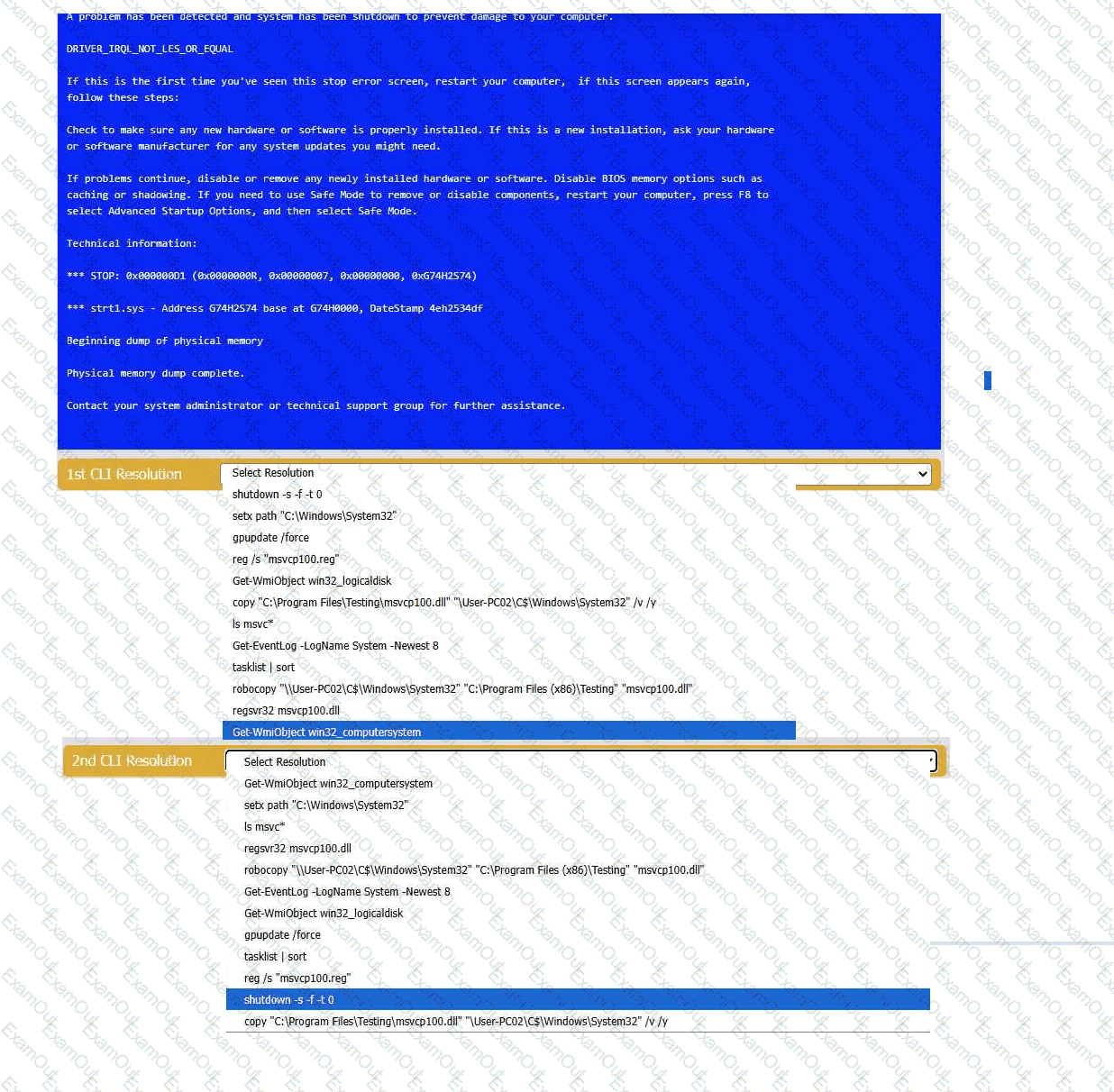
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
A technician is assisting a user who is growing increasingly frustrated because an application continuously crashes. The technician must coordinate with another department to resolve the issue. Which of the following actions should the technician take to effectively and professionally communicate with the user?
Which of the following Linux commands is used to read another command ' s documentation?
After completing malware removal steps, what is the next step the technician should take?
Recently, the number of users sharing smartphone passcodes has increased. The management team wants a technician to deploy a more secure screen lock method. Which of the following technologies should the technician use?
Which of the following should be used to verify the integrity of a downloaded patch?

 A screenshot of a computer AI-
A screenshot of a computer AI-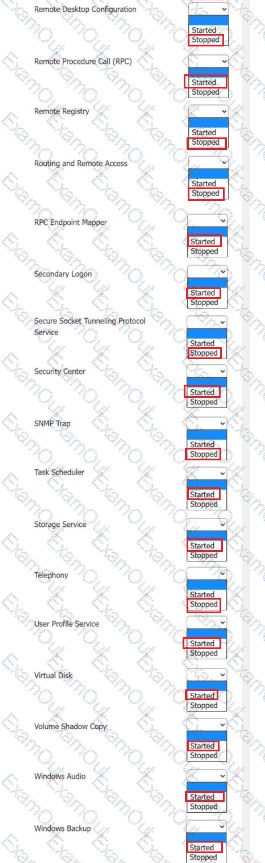 A screenshot of a computer AI-
A screenshot of a computer AI-