While assisting a customer with an issue, a support representative realizes the appointment is taking longer than expected and will cause the next customer meeting to be delayed by five minutes. Which of the following should the support representative do NEXT?
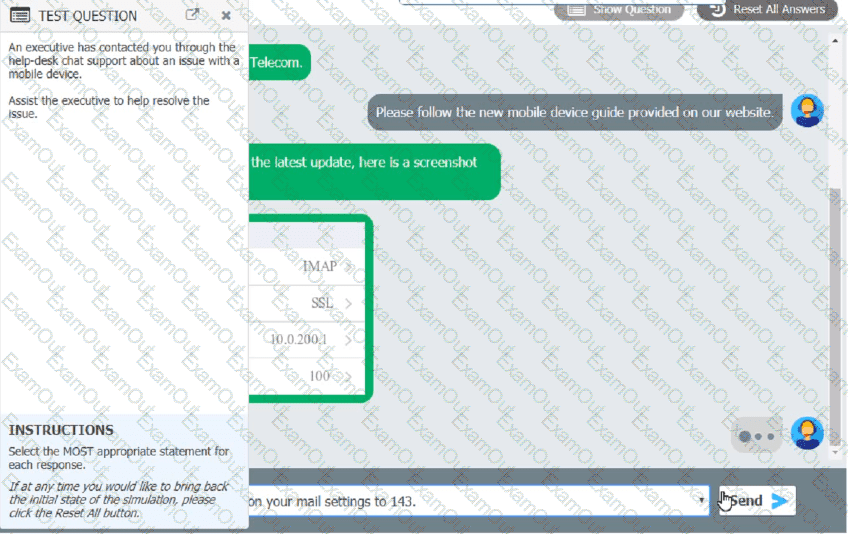
An executive has contacted you through the help-desk chat support about an issue with a mobile device.
Assist the executive to help resolve the issue.

Which of the following should be done NEXT?
A technician needs to transfer a large number of files over an unreliable connection. The technician should be able to resume the process if the connection is interrupted. Which of the following tools can be used?
Someone who is fraudulently claiming to be from a reputable bank calls a company employee. Which of the following describes this incident?
A technician needs to join a Windows client to a domain. Which of the following is required?
A user sent a large amount of money to a supplier's bank account and claims that the Chief Executive Officer instructed the user to do so. A technician informs the user that the request was fraudulent and contacts the authorities. Which of the following types of attack took place?
A customer reports high data usage on a smartphone that reaches its monthly data limit within the first week of each billing cycle. The customer uses the phone primarily for calls and SMS messages with minimal content streaming. A technician troubleshoots the phone and notices that both developer mode and installs from unknown sources are enabled. Which of the following should the technician check next?
Which of the following is the MOST cost-effective version of Windows 10 that allows remote access through Remote Desktop?
A company is opening several remote offices and would like to have the capability for its systems administrator to automate patch management and software deployment. Which of the following would meet this requirement?
A technician thinks that a computer on the network has been infected with malware. The technician attempts several times to use a malware removal tool, but the issue persists. Which of the following should the technician do next?
Employees want their Windows 10 laptops to wirelessly connect when they take them home. Which of the following should the employees configure so the laptops can automatically connect wirelessly?
A technician is setting up backup and recovery solutions that must restore quickly. Storage space is not a factor. Which of the following backup methods should the technician implement?
A technician installs a Bluetooth headset for a user. During testing, the sound is still coming from the speaker on the computer. The technician verifies the headset shows up in Device Manager. Which of the following would the technician most likely do to fix this issue?
A network technician, who is managing mobile devices with MDM, notices an Android phone is using an OS that differs from the factory version. The technician also sees that the device has the ability to perform administrative functions. Which of the following is the next step the technician should take?
A company is transitioning to a new firewall and discovers that one of the servers is still sending traffic to the old firewall. Which of the following IP address settings should a technician change to resolve this issue?
A security administrator teaches all of an organization's staff members to use BitLocker To Go. Which of the following best describes the reason for this training?
A company needs to securely and remotely access network devices. Which of the following will allow the company to access these devices?
A technician is helping a customer connect to a shared drive. The technician notices some unused drives that have already been mapped and wants to disconnect those drives first. Which of the following commands should the technician use?
A user identified that a program installed in a workstation does not have optional features enabled. Which of the following must the technician do to install the optional features?
A client recently upgraded their Windows 10 machine to Windows 11. The client reports the following message displays when turning the computer on: "Error loading operating system." Which of the following should a technician do first to troubleshoot this issue?

