What is the purpose of a subnet mask?
Which two actions are typically performed in ROMMON mode during the password recoveryprocess? (Choose two.)
Which two actions ensure a smooth transition to the new hardware when replacing a Cisco UCS C-Series Rack-Mount Server? (Choose two.)
Which two features are managed by the hardware and software of the collaboration infrastructure? (Choose two.)
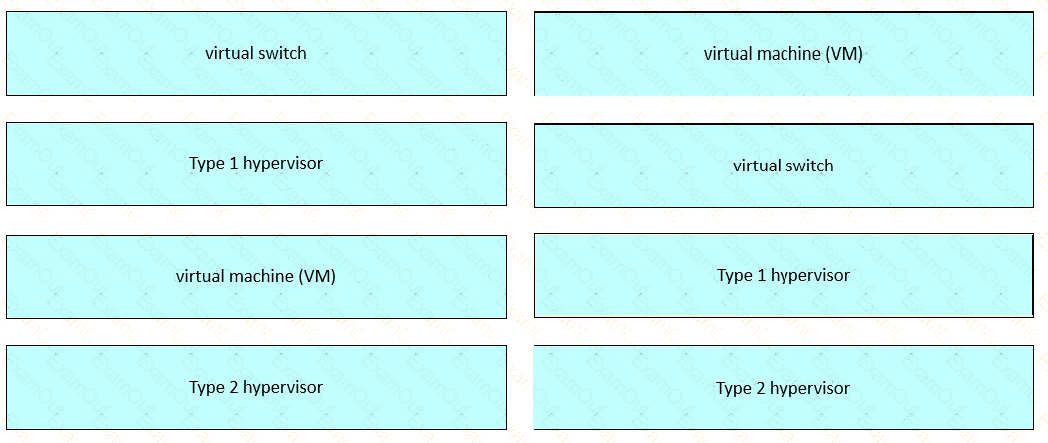
Drag and drop the virtualized data center components from the left onto the corresponding descriptions on the right.
Which layer of the OSI model provides error detection and defines how access to the media is controlled?
Which command is used to determine if there is sufficient space in the memory of a device before installing a new Cisco IOS image?
Which Layer 2 technology extends to access layer devices, allowing individual switch ports to be assigned for network and traffic management in an enterprise network?
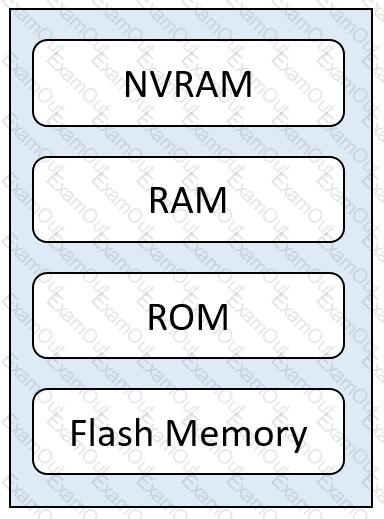
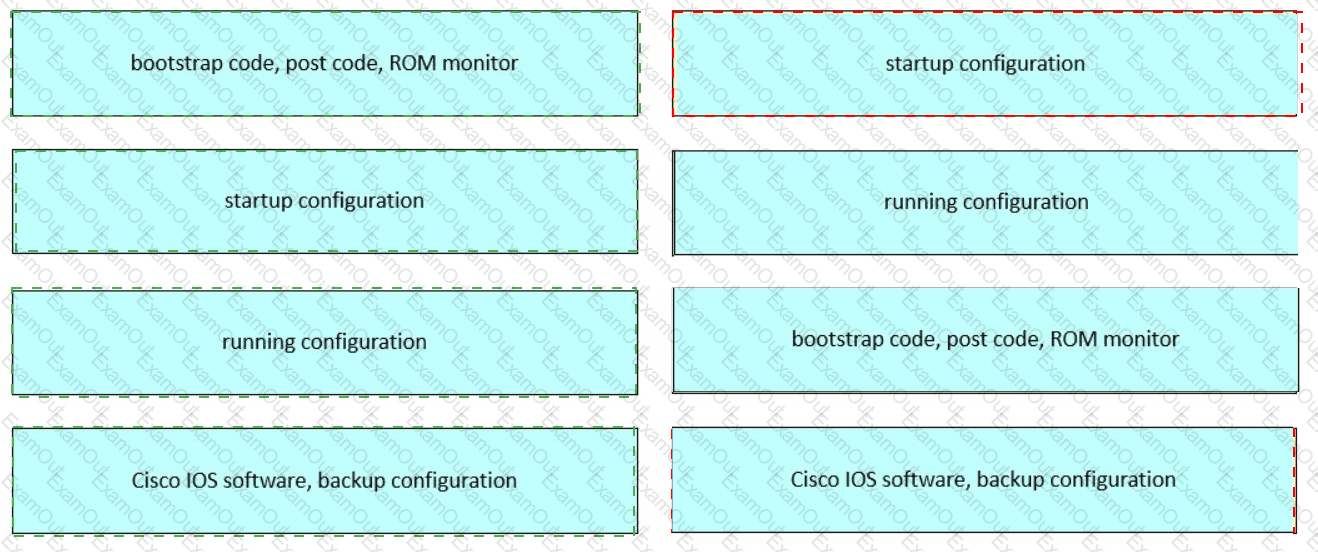
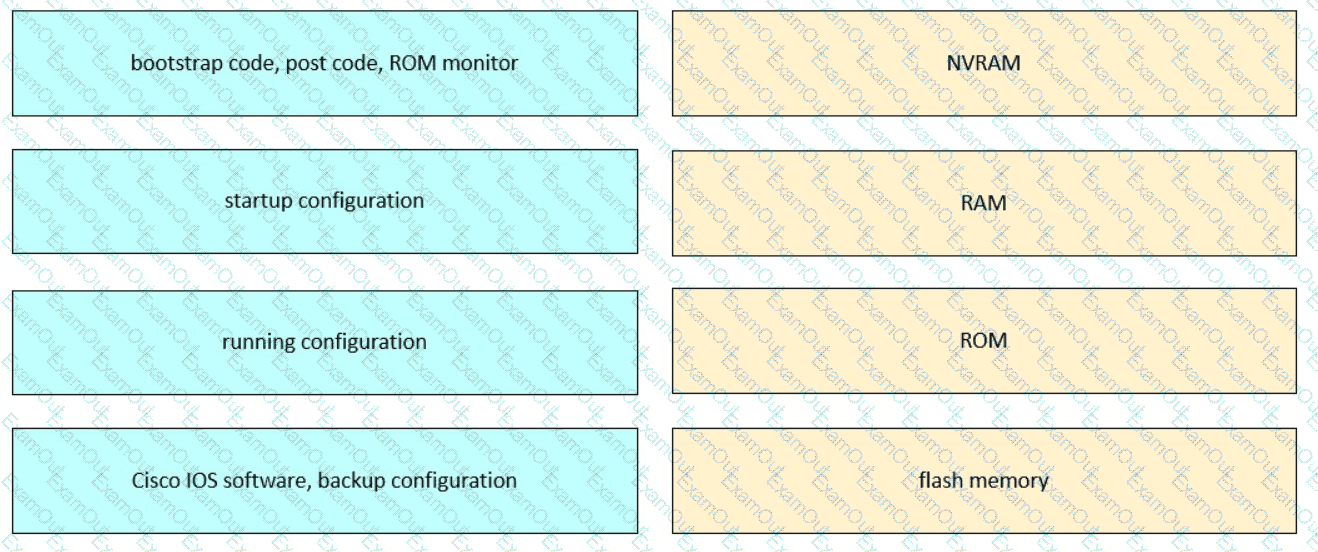
Refer to the exhibit. Drag and drop the functions from the left onto the corresponding internal memory components on the right.
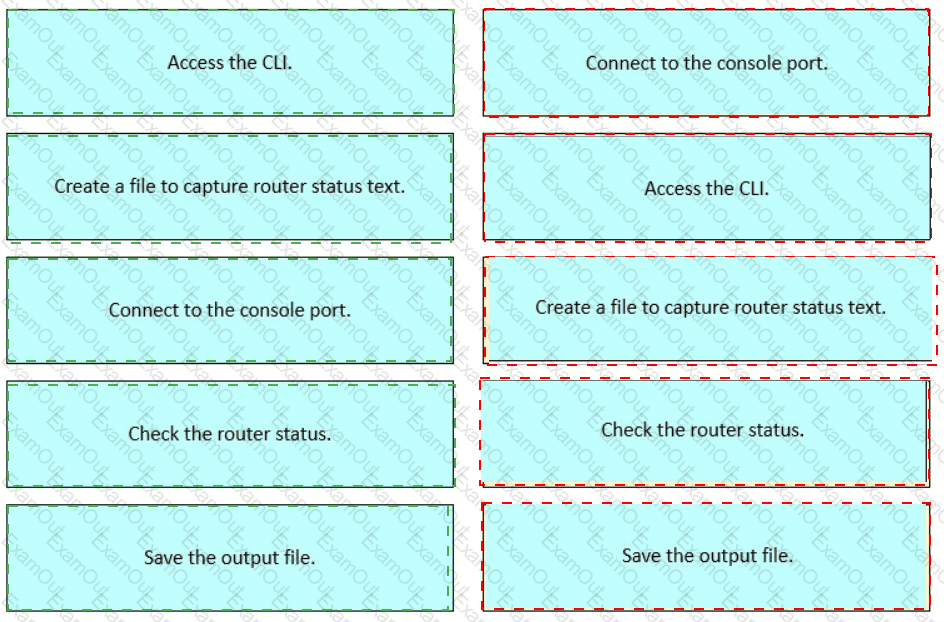
Which action must be taken before powering down the endpoint during thereplacement process of a Cisco collaboration device?