Which consideration must be made when using BFD in a network design?
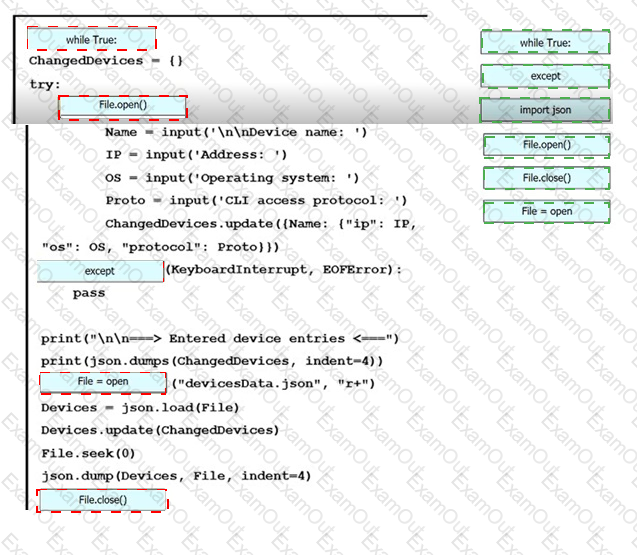
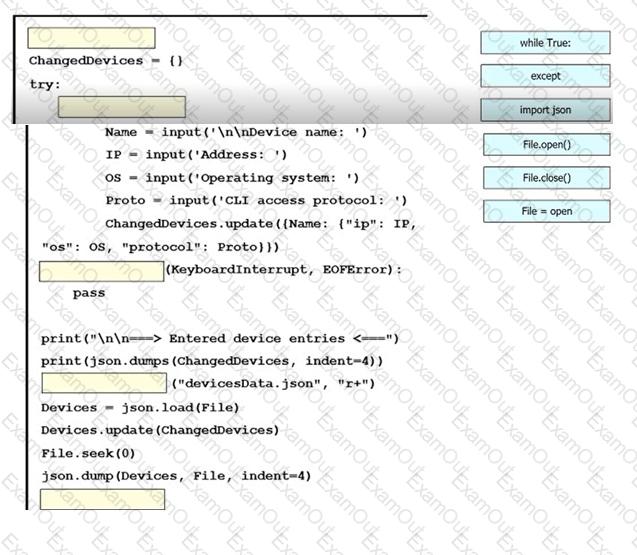
An engineer must create a script to append and modify device entries in a JSON-formatted file. The script must work as follows:
Until interrupted from the keyboard, the script reads in the hostname of a device, its management IP address, operating system type, and CLI remote access protocol.
After being interrupted, the script displays the entered entries and adds them to the JSON-formatted file, replacing existing entries whose hostname matches.
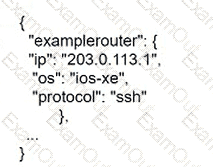
The contents of the JSON-formatted file are as follows
Drag and drop the statements onto the blanks within the code to complete the script. Not all options are used.
Which IEEE standard provides the capability to permit or deny network connectivity based on the user or device identity?
What is the primary responsibility of the vBond orchestrator?
Which characteristics applies to Cisco SD-Access?
What is a benefit of MACsec in a multilayered LAN network design?
Which characteristic applies to Cisco SD-Access?
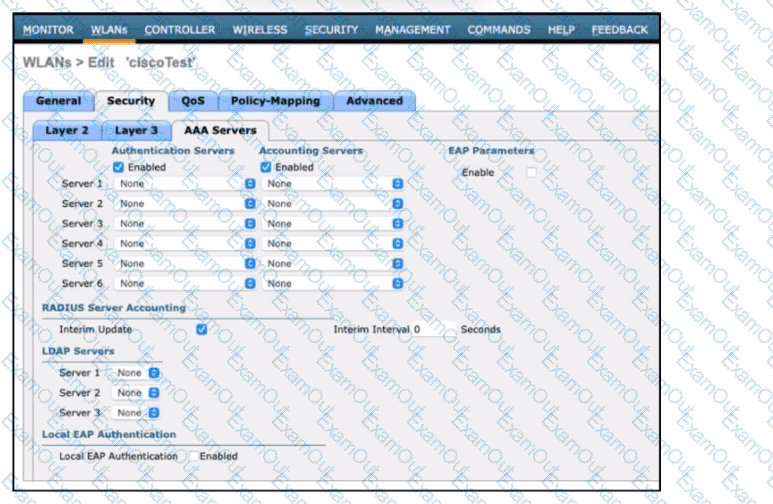
Refer to the exhibit. An engineer must configure a Cisco WLC with WPA2 Enterprise mode and avoid global server lists. Which action is required?
Which protocol is implemented to establish secure control plane adjacencies between Cisco Catalyst SD-WAN nodes?
Which architectural component enables a zero-trust security model?