When deploying Cisco SD-Access Fabric APs, where does the data plane VXLAN tunnel terminate?
Which two characteristics apply to Type 1 hypervisors? (Choose two.)
What is provided by the Stealthwatch component of the Cisco Cyber Threat Defense solution?
Which two operations are valid for RESTCONF? (Choose two)
Which two namespaces does the LISP network architecture and protocol use? (Choose two.)
Which feature provides data-plane security for Cisco Catalyst SD-WAN networks ' ?
Which solution supports end-to-end line-rate encryption between two sites?
Which LISP device is responsible for publishing EID-to-RLOC mappings for a site?
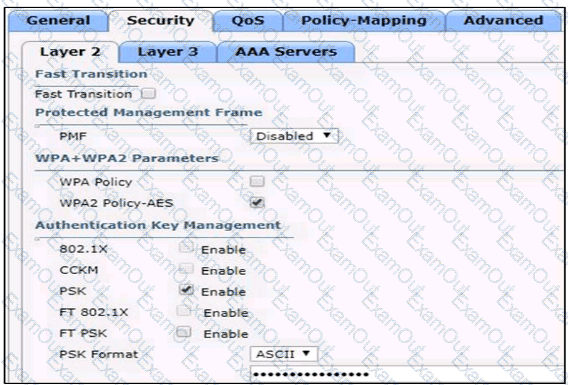
Based on the configuration in this WLAN security setting,Which method can a client use to authenticate to the network?
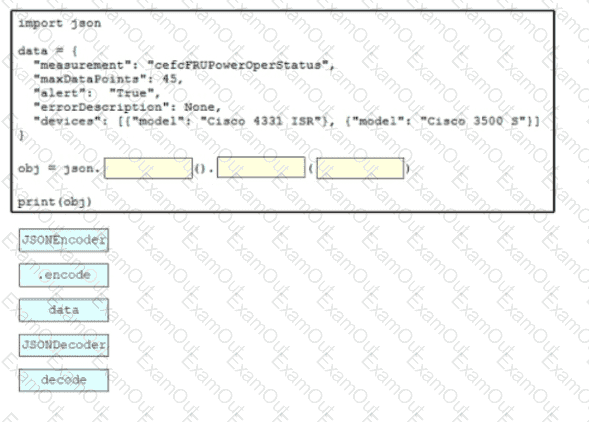
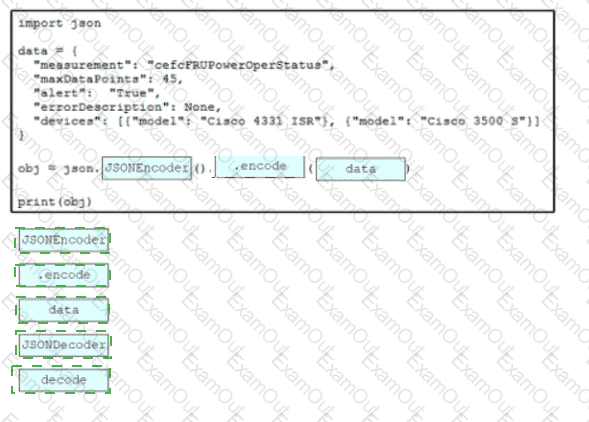
Drag and drop the code snippets from the bottom onto the blanks in the script to convert a Python object into a JSON string. Not all options are used