Network traffic coining from an organization's CEO must never be denied. Which access control policy configuration option should be used if the deployment engineer is not permitted to create a rule to allow all traffic?
When a Cisco FTD device is configured in transparent firewall mode, on which two interface types can an IP address be configured? (Choose two.)
An administrator is optimizing the Cisco FTD rules to improve network performance, and wants to bypass inspection for certain traffic types to reduce the load on the Cisco FTD. Which policy must be configured to accomplish this goal?
A company wants a solution to aggregate the capacity of two Cisco FTD devices to make the best use of resources such as bandwidth and connections per second. Which order of steps must be taken across the Cisco FTDs with Cisco FMC to meet this requirement?
Which object type supports object overrides?
A Cisco FMC administrator wants to configure fastpathing of trusted network traffic to increase performance. In which type of policy would the administrator configure this feature?
A Cisco FTD has two physical interfaces assigned to a BVI. Each interface is connected to a different VLAN on the same switch. Which firewall mode is the Cisco FTD set up to support?
An engineer must configure an ERSPAN passive interface on a Cisco Secure IPS by using the Cisco Secure Firewall Management Center. These configurations have been performed already:
Configure the passive interface.
Configure the ERSPAN IP address.
Which two additional settings must be configured to complete the configuration? (Choose two.)
A company is deploying Cisco Secure Endpoint private cloud. The Secure Endpoint private cloud instance has already been deployed by the server administrator. The server administrator provided the hostname of the private cloud instance to the network engineer via email. What additional information does the network engineer require from the server administrator to be able to make the connection to Secure Endpoint private cloud in Cisco Secure Firewall Management Centre?
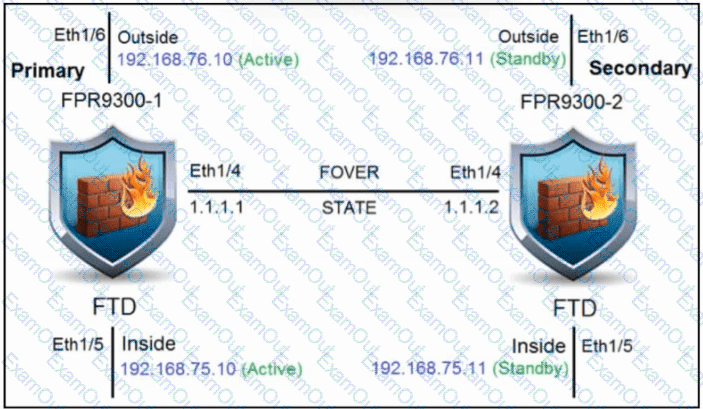
Refer to the exhibit. An engineer is configuring a high-availability solution that has the hardware devices and software versions:
two Cisco Secure Firewall 9300 Security Appliances with FXOS SW 2.0(1.23)
software Cisco Secure Firewall Threat Defense 6.0.1.1 (build 1023) on both appliances
one Cisco Secure Firewall Management Center with SW 6.0.1.1 (build 1023)
Which condition must be met to complete the high-availability configuration?

