Before creating a new Application Security Policy in Prism Central, what prerequisite must exist?
An administrator needs to use Prism Central to identify a subnet belonging to a VPC. How can the administrator identify networks associated with a VPC within Prism Central?
Which policy mode blocks all traffic that is not explicitly allowed by the policy?
Which step is required to prepare an AHV cluster for Flow Virtual Networking?
An administrator has created a VPC with the following subnets: 10.1.1.0/24 10.1.2.0/24 10.1.3.0/24 What action must be taken for these networks to be externally routable?
When creating a VPC, enabling the Transit VPC toggle changes the role of the VPC. What does the Transit VPC toggle do?
When configuring an Application policy, an administrator defines a VM Category Application:MySQL as a Secured Entity. The administrator wants to ensure that traffic between VMs in the Secured Entity is kept to only required replication traffic on the default mysql service port. How should the administrator best accomplish this?
An administrator receives a ticket reporting unwanted traffic between production and development servers. The administrator reviews the Flow Network Security logs and finds the following:
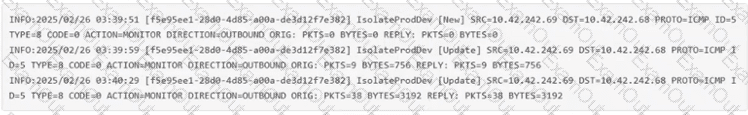
How can the administrator resolve the issue?
An administrator is deploying a multi-tier (web, app, database) application on a Nutanix cluster using AHV. The administrator needs to allow internal communication between tiers and provide external access to the web tier. How should the administrator satisfy this requirement?
Which policy mode records traffic without enforcing rule actions?

