An organization uses on-premises AHV-based clusters and also has workloads in public cloud environments.
The security team wants a single place to review security posture and compliance across the multi-cloud footprint, and they want the analysis to support security operations workflows rather than only showing cluster-level posture.
The administrator needs to pick the most appropriate Nutanix capability for this requirement.
Which option best aligns to the requirement?
An administrator manages a Nutanix cluster with software data-at-rest encryption enabled using an external KMS. Several VMs are configured with vTPM to support Windows BitLocker encryption.
The administrator needs to perform a disaster recovery operation and restore the VMs on a different cluster. During the recovery, the administrator discovers that the encryption key backup file is unavailable.
What is the expected outcome for the vTPM-enabled VMs?
An administrator manages a shared AHV environment where Dev workloads must not exceed 2,000 IOPS per VM during business hours to prevent noisy-neighbor impact on Prod.
The administrator already uses categories to group VMs (for example, category Env=Dev) and wants a scalable approach that applies consistent throttling to all current and future Dev VMs without configuring each VM individually.
Which approach best meets the requirement?
An administrator needs to protect a volume group using a protection policy that supports an RPO of 1 hour. The environment consists of two clusters in different geographic regions. Which replication type should be used?
What is the default compression setting when a new storage container is created in Prism Central?
An administrator manages a 3-node AHV cluster and needs to optimize overall cluster consumption starting from a recording server workload that stores MP4 videos on dedicated local vDisks. Specifications:
Compression: post process 60 min
Capacity dedupe: disabled
Erasure coding: Disabled
Which configuration would best improve cluster performance?
An administrator has been asked to deploy a single-node Prism Central VM, with the possibility to scale out to increase its capacity. What is the minimum supported Prism Central size?
Refer to the exhibit.
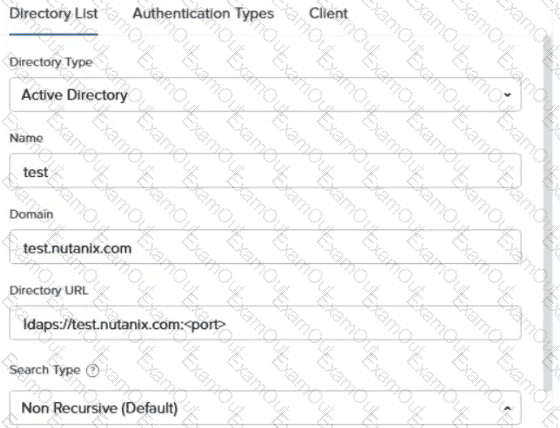
An administrator is configuring Active Directory Authentication in Prism Element and wants to ensure all traffic is encrypted. Which port should the administrator use?
A company has purchased Nutanix hardware for multiple remote branch offices. The IT team at headquarters needs to image and deploy all clusters remotely from a central location.
An administrator deploys Foundation Central from the Prism Central Marketplace.
What capability does Foundation Central provide in this scenario?
An administrator has configured CVM security hardening on a Nutanix cluster with the following settings:
IP Restriction State is set to enabled
Password-based SSH access is disabled via Cluster Lockdown
The administrator attempts to SSH into the CVM from a new jump box and the connection is refused.
What should the administrator do to restore SSH access to the CVM?

