You have a Microsoft 365 subscription that contains a user named User1 and 500 Windows devices enrolled in Microsoft Intune.
You configure an attack surface reduction {ASR) rule and enable the rule in Warn mode.
User1 downloads a file named file1.exe. When User1 attempts to run file1.exe he receives a prompt that the content has been blocked. The user unblocks the content.
How much time will pass until the user is prompted next to unblock the content?
You have a Microsoft 365 subscription that contains a user named User1. User! is assigned a Windows 10/11 Enterprise E3 license. You use Microsoft Intune Suite to manage devices. User1 activates the following devices:
• Device1: Windows 11 Enterprise
• Device2: Windows 10 Enterprise
• Device3: Windows 11 Enterprise
How many more devices can User1 activate?
You have a Microsoft 365 tenant.
You have devices enrolled in Microsoft Intune.
You assign a conditional access policy named Policy1 to a group named Group1. Policy! restricts devices marked as noncompliant from accessing Microsoft OneDrive for Business.
You need to identify which noncompliant devices attempt to access OneDrive for Business. What should you do?
You have computer that run Windows 10 and connect to an Azure Log Analytics workspace. The workspace is configured to collect all available events from Windows event logs.
The computers have the logged events shown in the following table.
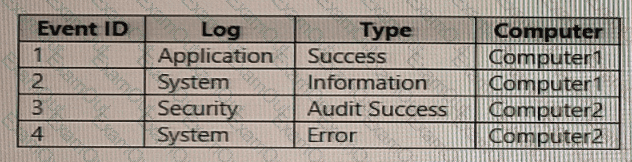
Which events are collected in the Log Analytics workspace?
You have computers that run Windows 10 and are managed by using Microsoft Intune.
Users store their files in a folder named D:\Folder1.
You need to ensure that only a trusted list of applications is granted write access to D:\Folder1.
What should you configure in the device configuration profile?
You have a Microsoft Intune subscription.
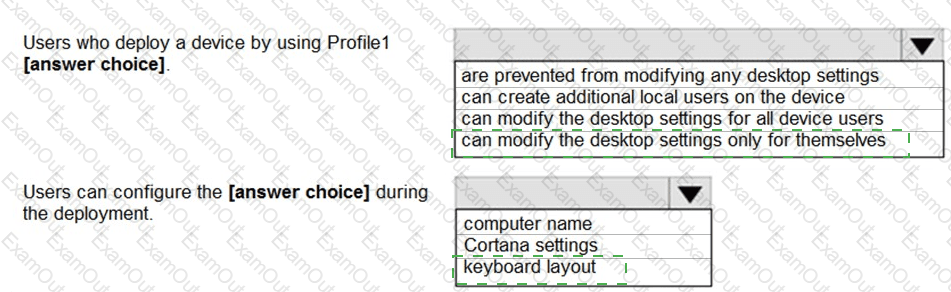
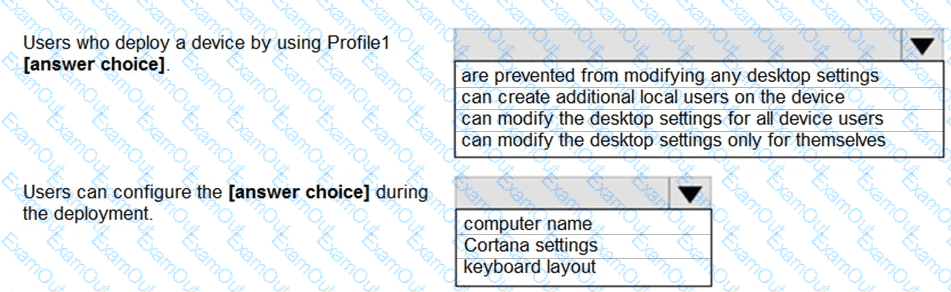
You are creating a Windows Autopilot deployment profile named Profile1 as shown in the following exhibit.
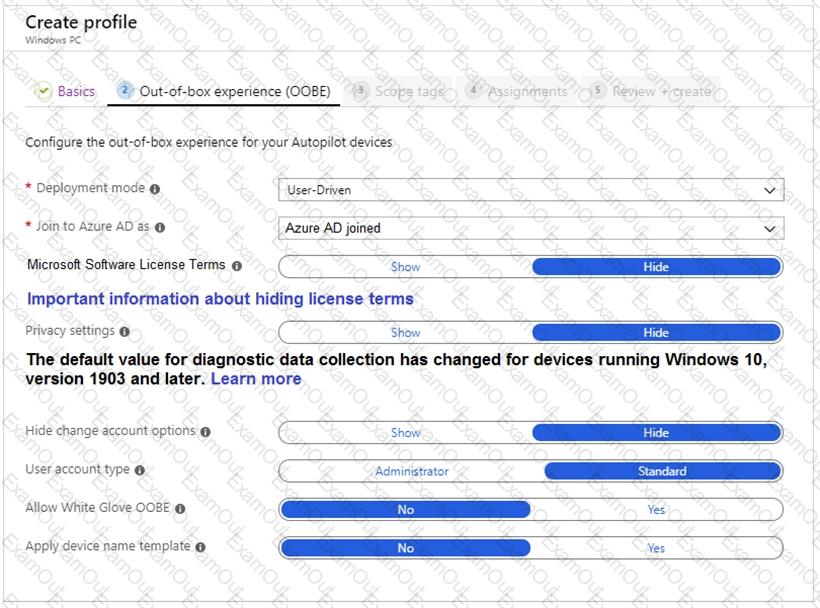
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
Your company has an Azure AD tenant named contoso.com that contains several Windows 10 devices.
When you join new Windows 10 devices to contoso.com, users are prompted to set up a four-digit pin.
You need to ensure that the users are prompted to set up a six-digit pin when they join the Windows 10 devices to contoso.com.
Solution: From the Microsoft Entra admin center, you configure automatic mobile device management (MDM) enrollment. From the Microsoft Intune admin center, you configure the Windows Hello for Business enrollment options.
Does this meet the goal?
You have an Azure AD tenant that contains the devices shown in the following table.
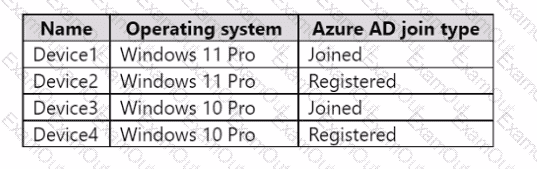
You purchase Windows 11 Enterprise E5 licenses.
Which devices can use Subscription Activation to upgrade to Windows 11 Enterprise?
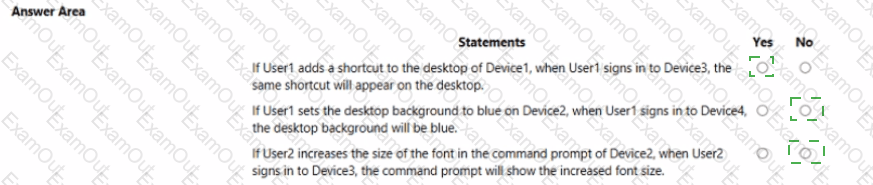
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
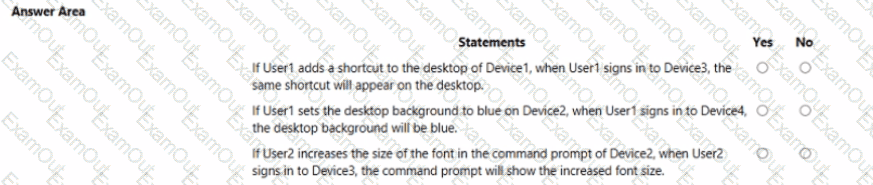
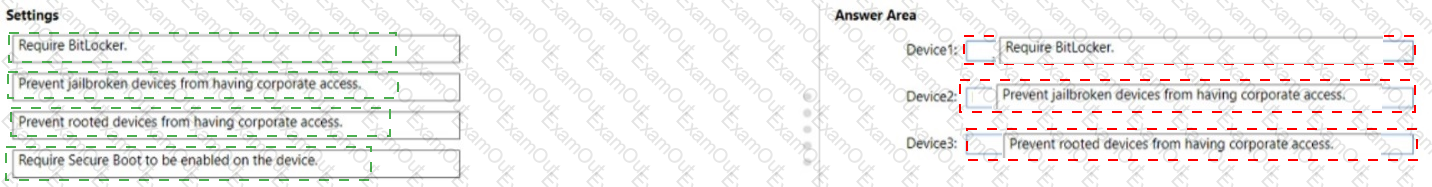
You have a Microsoft 365 subscription that contains the devices shown in the following table.
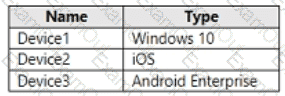
You need to ensure that only devices running trusted firmware or operating system build can access network resources.
Which compliance policy setting should you configure for each device? To answer, drag the appropriate settings to the correct devices. Each setting may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.