On FusionAccess software deployment, if multiple FusionAccess systems share a License, the License component should be deployed independently.
In compute virtualization, which of the following is the operating system running on a virtual machine (VM)?
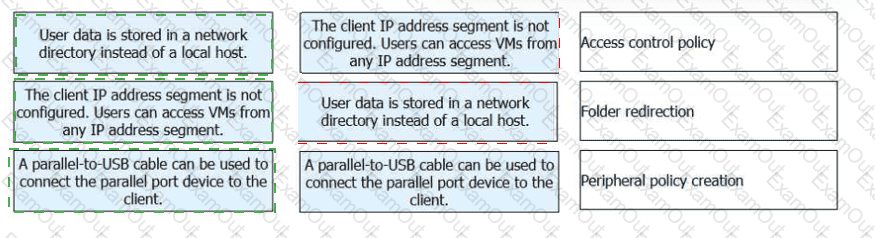
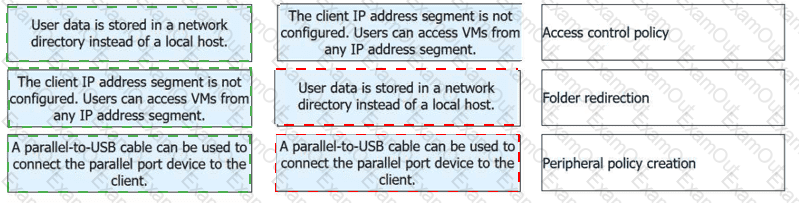
On FusionAccess policy management, match the following scenarios with their operations.

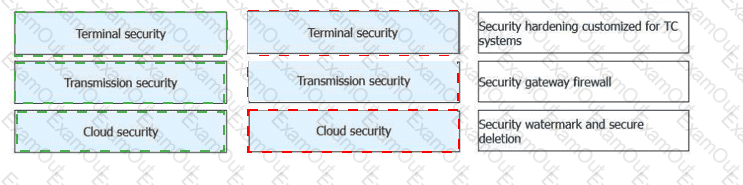
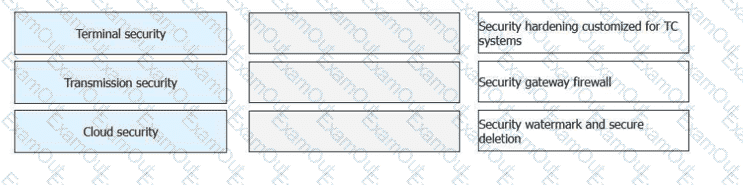
FusionAccess provides three protection mechanisms and 11 key measures to prevent data from being stored locally and make behaviors traceable and processes auditable, enhancing
end-to-end security. Match the key measures with the following protection mechanisms.
At which layer of the TCP/IP reference model does a router work?
Which of the following storage types isrecommendedfor VRM deployment during Huawei FusionCompute installation?
When an administrator uses alinked clone templateto quickly provision virtual machines (VMs) on FusionAccess, which of the following are thesteps of the quick provision process?
In virtualization, KVM and Xen are typical hardware-assisted virtualization technologies. They implement virtualization based on kernel modules in the operating system.
On FusionAccess policy management, match the following scenarios with their operations