Which of the following technologies is used by Open vSwitch (OVS) for remote access and traffic control?
In Huawei FusionCompute, which of the following resources cannot be reduced?
To enhance the security of user desktops, FusionAccess supports diverse access management policies. Which of the following statements about access management policies are true?
Virtualization is the fundamental technology powering cloud computing. It is the act of creating a virtual version of something and a logical representation of physical resources. It allows resource simulation, isolation, and sharing.
In Huawei FusionCompute, which of the following functions enables virtual machines (VMs) to be migrated between CNA hosts with different CPU models?
Which of the following statements is false about CPU virtualization?
Which of the following statements arefalseabout VLAN technology?
Which of the following statements is false about the graphical user interface (GUI) and the command-line interface (CLI) of Linux?
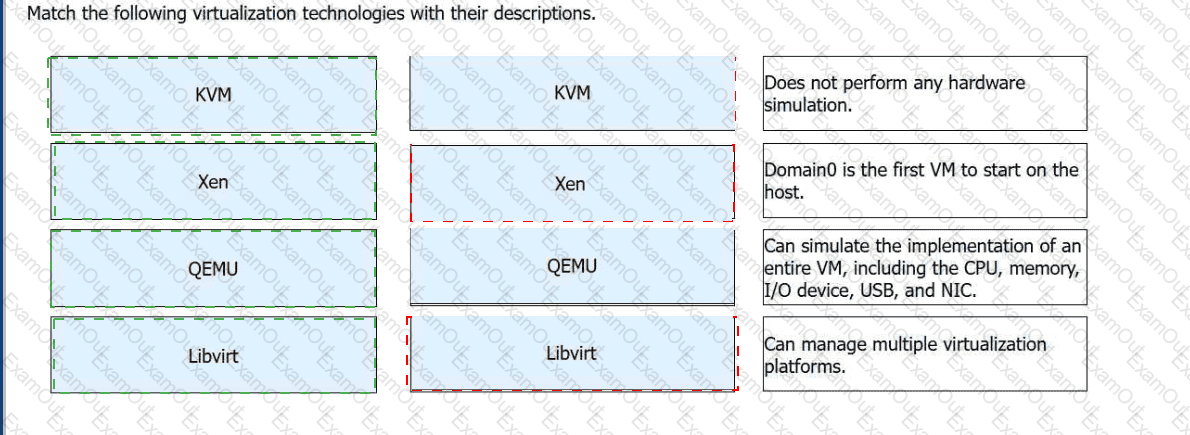
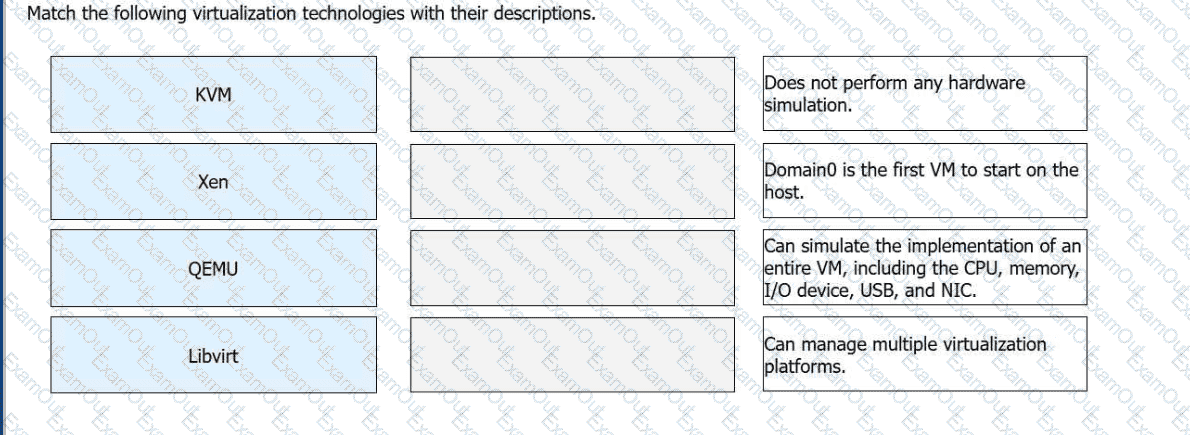
Match the following virtualization technologies with their descriptions.
Which of the following statements about FusionAccess for office automation (OA) isfalse?