In the deployment of Huawei NIP6000 products, only port mirroring can be used for streaming replication.
The following figure is a schematic diagram of the detection file of the firewall and the sandbox system linkage.
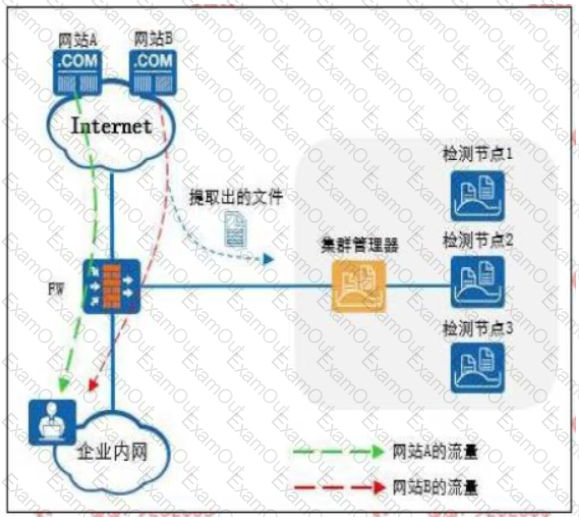
The Web reputation function is enabled on the firewall, and website A is set as a trusted website and website B is set as a suspicious website.
Which of the following statements is correct
In the security protection system of the cloud era, reforms need to be carried out in the three stages before, during and after the event, and a closed-loop continuous improvement should be formed.
And development. Which of the following key points should be done in "things"? (multiple choice)
Tianyu Nei answered the role of safety filtering technology, which of the following is still correct? (multiple choice)
Which of the following options does not belong to the security risk of the application layer of the TCP/IP protocol stack?
Regarding the anti-spam response code, which of the following statements is wrong?
For Huawei USG600 products, which of the following statements about mail filtering configuration is correct?
There are several steps in a stored XSS attack
①The attacker hijacks the user session
②The attacker submits an issue containing known JavaScript
③User login
④The user requests the attacker's question 5
⑤The server responds to the attacker’s JavaScript
⑥ The user's browser sends a session token to the attacker
⑦The attacker's JavaScript is executed in the user's browser
For the ordering of these steps, which of the following options is correct?
In the Huawei USG6000 product, after creating or modifying the security configuration file, the configuration content will not take effect immediately: you need to click the "Prompt" in the upper right corner of the interface.
"Hand in" to activate.
Threats detected by the big data intelligent security analysis platform will be synchronized to each network device at the same time C and then collected from the network device
Collect it in the log for continuous learning and optimization.

