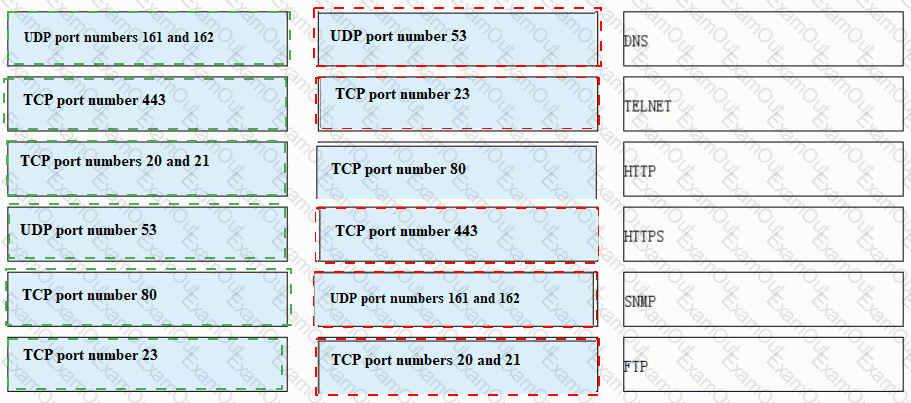
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
Which of the following statements are correct about SYN flood attack defense technologies on Huawei firewalls?
Which of the following descriptions about the heartbeat interface is wrong ( )?
Digital envelope technology means that the sender uses the receiver's public key to encrypt the data, and then sends the ciphertext to the receiver
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
The initial priority of the USG9500VGMP group is related to which of the following factors ( )? *
According to the level protection requirements, which of the following behaviors belong to the scope of information security operation and maintenance management? ( )*
Which of the following types of packets cannot be filtered by a packet filtering firewall?
Devices that need to provide network services externally, such as WWW servers and FTP servers, can be placed in the DMZ.