Refer to the exhibit, which contains the output of diagnose vpn tunnel list.
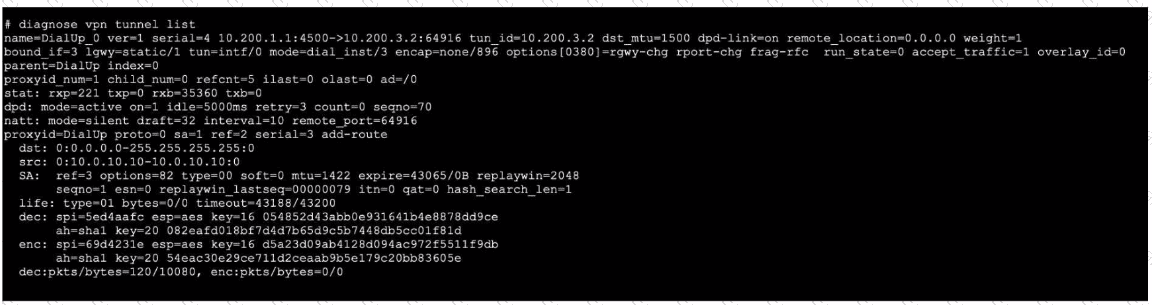
Which command will capture ESP traffic for the VPN named DialUp_0?
What are two reasons you might see iprope_in_check() check failed, drop when using the debug flow? (Choose two.)
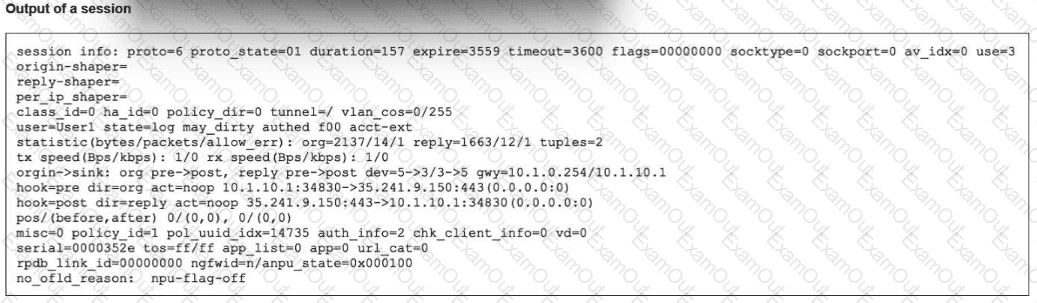
Refer to the exhibit, which shows the omitted output of a session table entry.
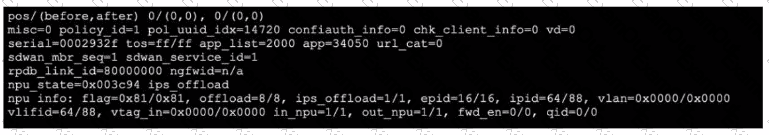
Which two statements are true? (Choose two.)
Exhibit.
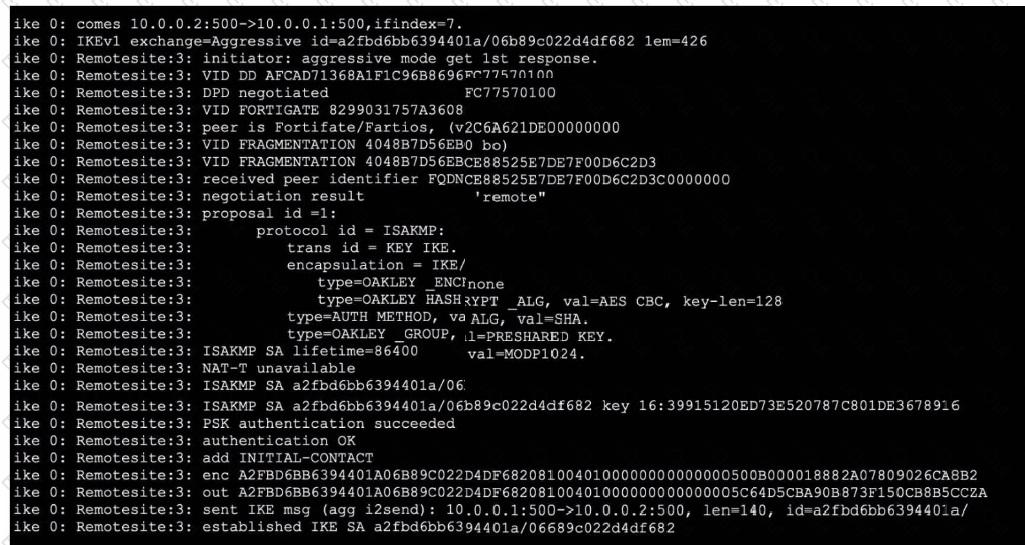
Refer to the exhibit, which contains partial output from an IKE real-time debug.
Which two statements about this debug output are correct? (Choose two.)
Exhibit.

Refer to the exhibit, which shows a partial web fillet profile configuration.
Which action does FortiGate lake if a user attempts to access www. dropbox. com, which is categorized as File Sharing and Storage?
Consider the scenario where the server name indication (SNI) does not match either the common name (CN) or any of the subject alternative names (SAN) in the server certificate.
Which action will FortiGate take when using the default settings for SSL certificate inspection?
Refer to the exhibit.
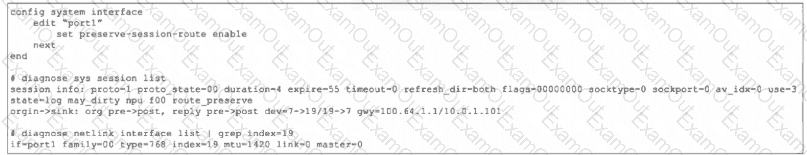
The port1 interface configuration on FortiGate and partial session information for ICMP traffic are shown.
Which two things happen to the session information if a routing change occurs that affects this session? (Choose two answers)
A FortiGate administrator is troubleshooting a VPN that is failing to establish.
As a first step, the administrator is attempting to sniff the traffic using the command:
# diagnose sniffer packet any ‘’udp port 500 or udp port 4500 or esp’’ 4
After several minutes there is still no output. What is the most Likely reason for this?
Refer to the exhibit.
The exhibit shows the output of a session. Which two statements are correct? (Choose two.)
Refer to the exhibit.
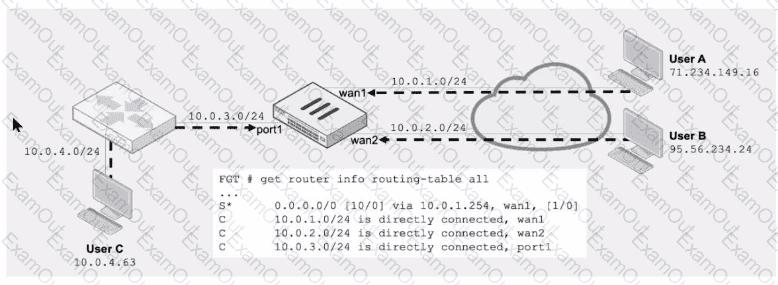
Assuming a default configuration, which three statements are true? (Choose three.)

