Ayden works from home on his company's laptop. During working hours, he received an antivirus software update notification on his laptop. Ayden clicked on the update button; however, the system restricted the update and displayed a message stating that the update could only be performed by authorized personnel. Which of the following PCI-DSS requirements is demonstrated In this scenario?
ProNet, a leading technology firm, has been dynamically evolving its internal infrastructure to cater to an expanding workforce and changing business needs. The company's current project involves enhancing the overall security of its internal platforms. The company’s security team is focusing on a robust access control system. To make the system efficient, it needs to implement a model that would define access based on roles within the organization, where specific roles would have predefined access to certain resources, and the roles can be assigned to multiple users. The aim is to decrease the administrative work involved in assigning permissions and ensure that users gain only the necessary permissions in line with their job functions.
Which access control model best suits ProNet's requirement?
A global financial Institution experienced a sophisticated cyber-attack where attackers gained access to the internal network and exfiltrated sensitive data over several months. The attack was complex, involving a mix of phishing, malware, and exploitation of system vulnerabilities. Once discovered, the institution initiated its incident response process. Considering the nature and severity of the incident, what should be the primary focus of the incident response team's initial efforts?
You are the Lead Cybersecurity Specialist at GlobalTech, a multinational tech conglomerate renowned for its avant-garde technological solutions in the aerospace and defense sector. The organization's reputation stands on the innovative technologies it pioneers, many of which are nation’s top secrets.
Late on a Sunday night, you are alerted about suspicious activities on a server holding the schematics and project details for a groundbreaking missile defense system. The indicators suggest a complex, multi-stage cyberattack that managed to bypass traditional security measures. Preliminary investigations reveal that the cybercrlmlnals might have used an Insider's credentials, further complicating the breach. Given the extremely sensitive nature of the data involved, a leak could have severe national security implications and irreparably tarnish the company's reputation. Considering the potential gravity and intricacies of this security incident, what immediate action should you undertake to handle this situation effectively, safeguard crucial data, and minimize potential fallout?
Dany, a member of a forensic team, was actively involved in an online crime investigation process. Dany's main responsibilities included providing legal advice on conducting the investigation and addressing legal issues involved in the forensic investigation process. Identify the role played by Dany in the above scenario.
A startup firm contains various devices connected to a wireless network across the floor. An AP with Internet connectivity is placed in a corner to allow wireless communication between devices. To support new devices connected to the network beyond the APS range, an administrator used a network device that extended the signals of the wireless AP and transmitted it to uncovered area, identify the network component employed by the administrator to extend signals in this scenario.
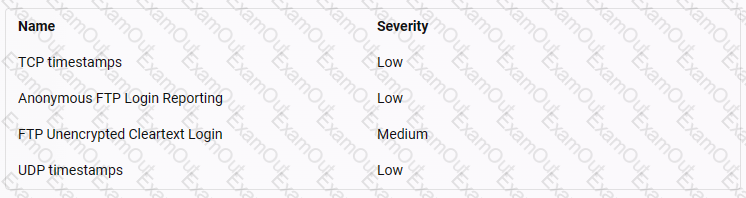
You are Harris working for a web development company. You have been assigned to perform a task for vulnerability assessment on the given IP address 20.20.10.26. Select the vulnerability that may affect the website according to the severity factor.
Hint: Greenbone web credentials: admin/password
Malachi, a security professional, implemented a firewall in his organization to trace incoming and outgoing traffic. He deployed a firewall that works at the session layer of the OSI model and monitors the TCP handshake between hosts to determine whether a requested session is legitimate.
Identify the firewall technology implemented by Malachi in the above scenario.