How does the Falcon sensor for Windows contribute to the enforcement in Falcon Identity Protection?
How does CrowdStrike Falcon Identity Protection help customers identify different types of accounts in their domain?
What is the recommended action for the"Guest Account Enabled"risk?
Which of the following isNOTan available Goal within the Domain Security Overview?
Falcon Identity Protection monitors network traffic to build user behavioral profiles to help identify unusual user behavior. How can this be beneficial to create a Falcon Fusion workflow?
When an endpoint that has not been used in the last90 daysbecomes active, a detection forUse of Stale Endpointis reported.
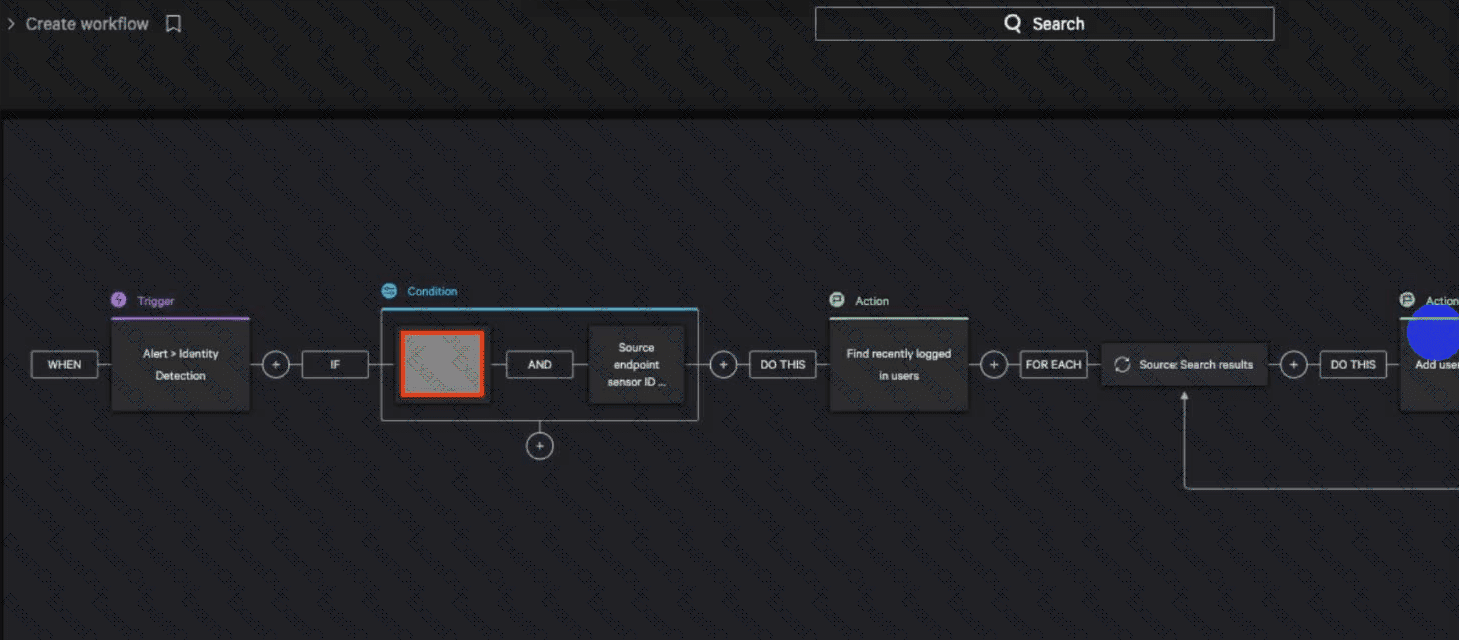
Considering the following example, what MITRE ATT&CK tactic would you use to complete the workflow?
What does a modern Zero Trust security architecture offer compared to a traditional wall-and-moat (perimeter-based firewall) approach?
Under which CrowdStrike documentation category could you find Identity Protection API information?
Where in the Identity Protection module can one view the monitoring status of domain controllers?

