Which of the following describes the method of consolidating system events to a single location?
The development team asks a Linux administrator to help diagnose a connectivity issue that is occurring with a newly developed software. The Linux administrator reviews the following output:
$ wget -vvv https://api.newapp.comptia.org/v2/health
Resolving proxy.comptia.org (proxy.comptia.org)... connected.
ERROR: The certificate of ' api.newapp.comptia.org ' is not trusted.
ERROR: The certificate of ' api.newapp.comptia.org ' does not have a known issuer.
Which of the following actions is the best way to resolve the issue?
Which of the following is the best use of AI within a Linux environment?
A Linux administrator needs to add a new HTTP service on the server. Which of the following commands allows other systems to communicate with the service after the system is restarted?
A systems administrator receives reports from users who are having issues while trying to modify newly created files in a shared directory. The administrator sees the following outputs:
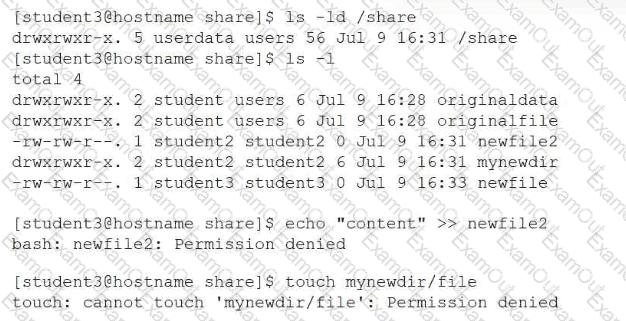
Which of the following provides the best resolution to this issue?
A Linux administrator needs to compare two files and provide the output in the following format:
2,3d1
< Line 2
< Line 3
4a3
Line 5
Which of the following commands should the administrator use to perform the task?
An administrator is trying to terminate a process that is not responding. Which of the following commands should the administrator use in order to force the termination of the process?
A Linux user needs to download the latest Debian image from a Docker repository. Which of the following commands makes this task possible?
Which of the following can be implemented with PAM to detect and block dictionary attacks?
An administrator receives the following output while attempting to unmount a filesystem:
umount /data1: target is busy.
Which of the following commands should the administrator run next to determine why the filesystem is busy?

