SIMULATION
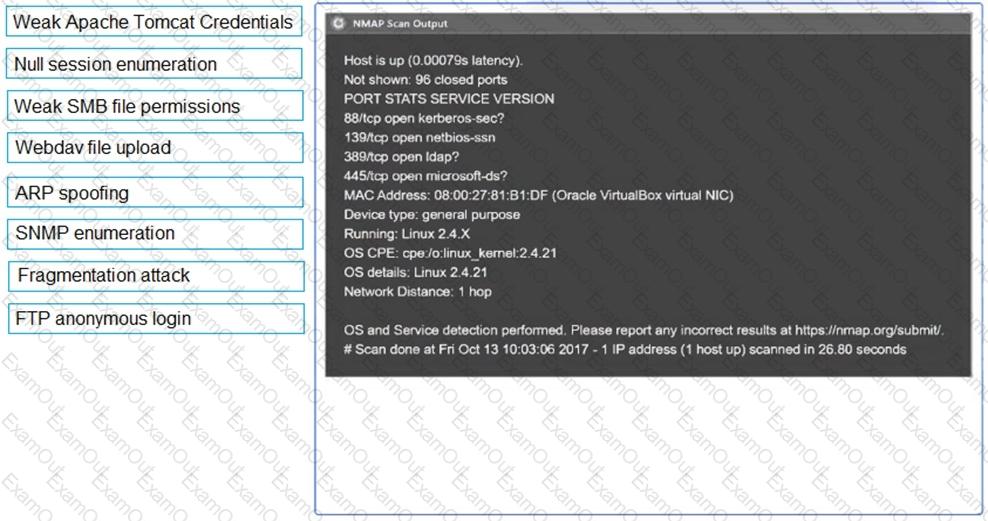
Using the output, identify potential attack vectors that should be further investigated.
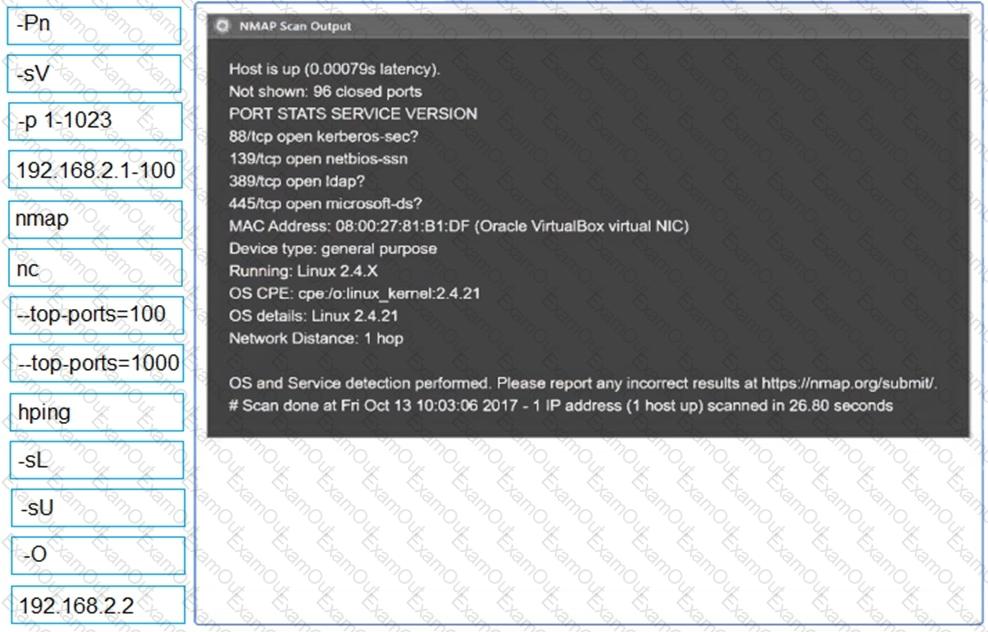
A penetration tester needs to confirm the version number of a client ' s web application server. Which of the following techniques should the penetration tester use?
During a vulnerability assessment, a penetration tester finds the following information:
KRBTGT account with more than 1250 days without password change.
Which of the following tools could an attacker use to exploit this vulnerability?
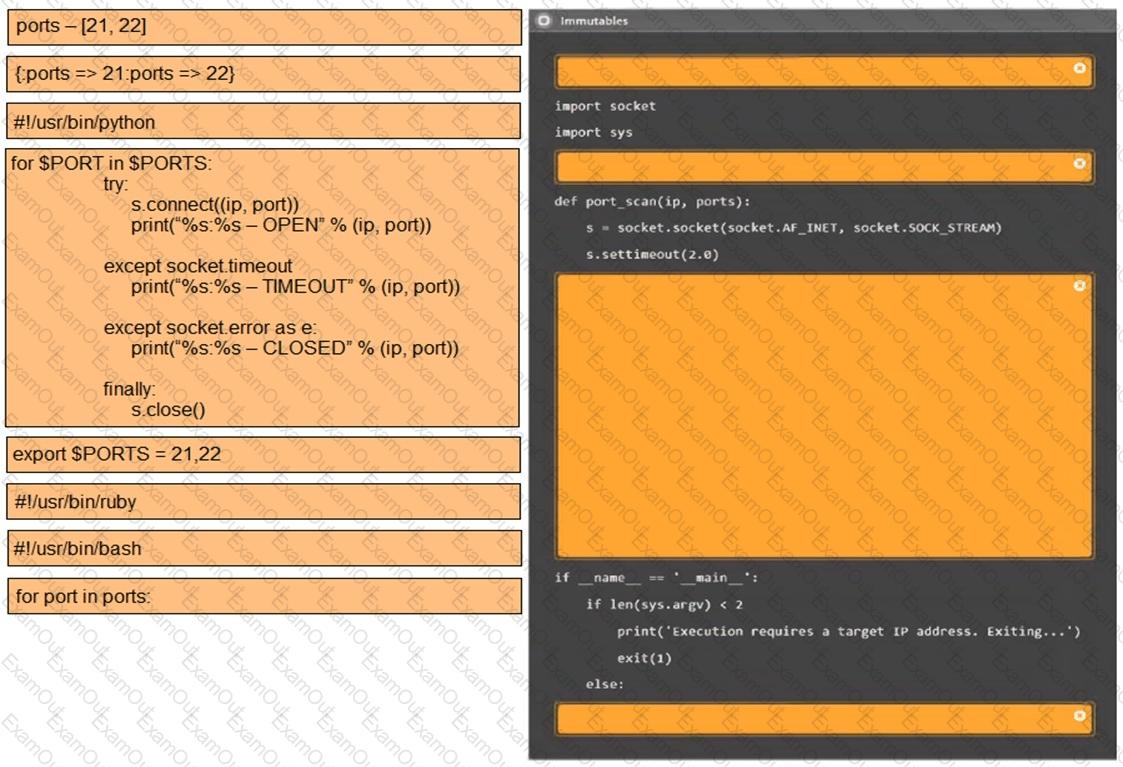
A penetration tester needs to collect information over the network for further steps in an internal assessment. Which of the following would most likely accomplish this goal?
Which of the following technologies is most likely used with badge cloning? (Select two).
During a security assessment, a penetration tester needs to exploit a vulnerability in a wireless network ' s authentication mechanism to gain unauthorized access to the network. Which of the following attacks would the tester most likely perform to gain access?
A penetration tester would like to collect permission details for objects within the domain. The tester has a valid AD user and access to an internal PC. Which of the following sets of steps is the best way for the tester to accomplish the desired outcome?
A penetration tester plans to conduct reconnaissance during an engagement using readily available resources. Which of the following resources would most likely identify hardware and software being utilized by the client?
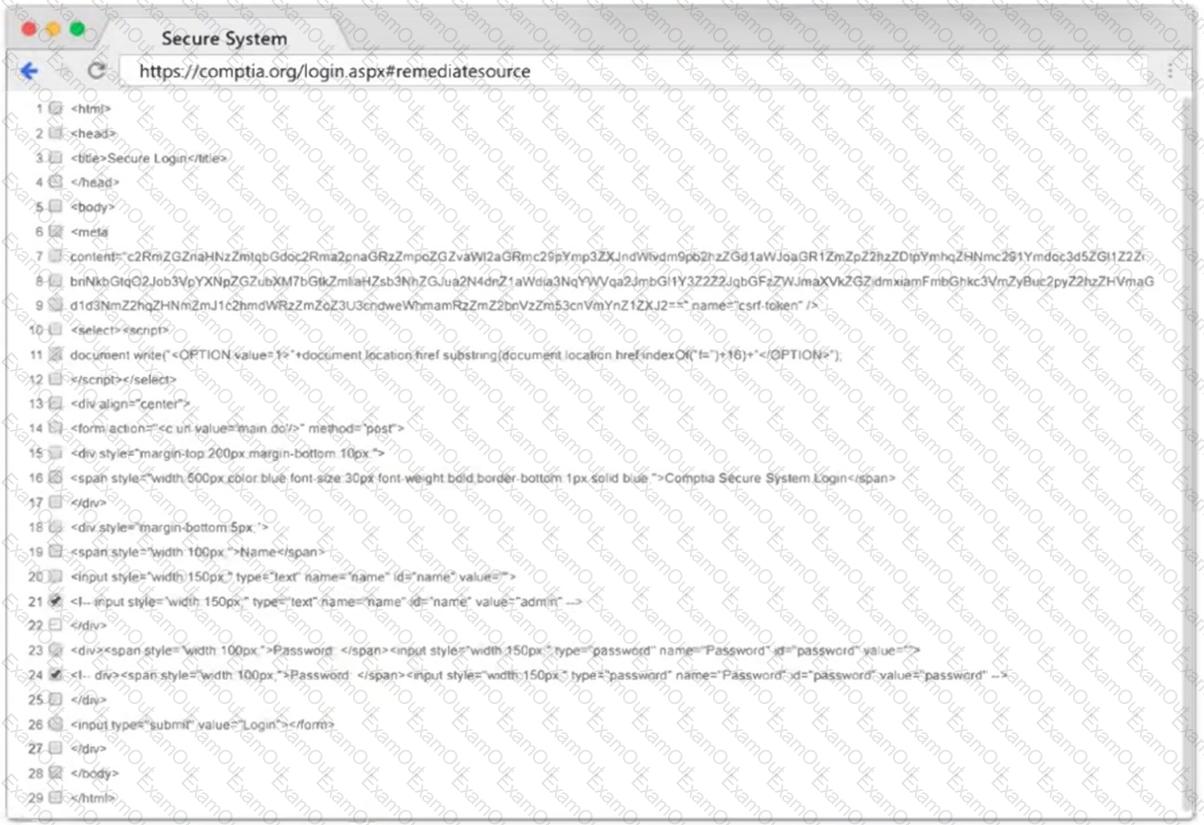
openssl passwd password
$1$OjxLvZ85$Fdr51vn/Z4zXWsQR/Xrj.
The tester then adds the following line to the world-writable script:
echo ' root2:$1$0jxLvZ85$Fdr51vn/Z4zXWsQR/Xrj .: 1001:1001:,,,:/root:/bin/bash " > > /etc/passwd
Which of the following should the penetration tester do to enable this exploit to work correctly?
A penetration tester runs a network scan but has some issues accurately enumerating the vulnerabilities due to the following error:
OS identification failed
Which of the following is most likely causing this error?

