Refer to the exhibit. An administrator connects a Cisco Nexus Series to the Cisco ACI fabric. The connectivity must allow Cisco Discovery Protocol LLDP, and LACP. Which action enables the protocols between Switch-1 and the ACI leaf switches?
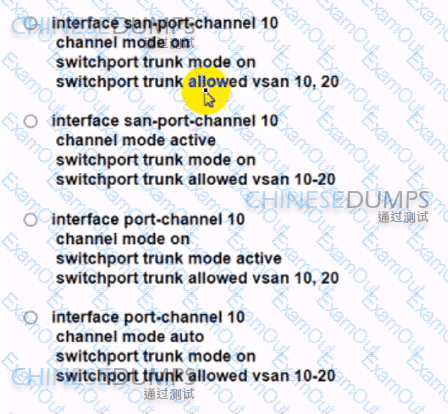
An engineer must configure a Fibre Channel port channel on a Cisco Nexus 9000 Series Switch. The configuration must meet these requirements:
A port-channel protocol negotiation is performed with the peer ports.
The trunk mode must be explicitly configured for the interfaces.
VSANs from 10 to 20 must be allowed.
Which command set configures the devices to meet the requirements?
An engineer is implementing a Cisco ACI fabric and must use static VLAN range as part of a VMM deployment. The static VLAN must be incorporated into the dynamic VLAN pool. The existing VLAN pool is set for dynamic allocation. Which action accomplishes this goal?
A Cisco UCS user called " Employee1 " accidentally changed the boot policy of the Cisco UCS server at the Cisco UCS Manager root level. This change impacted all service profiles and their storage connectivity was lost. The system administrator wants to prevent this issue from recurring in the future. The new security policy mandates that access must be restricted up to the organization level and prevent other users from modifying root policies. Which action must be taken to meet these requirements?
An engineer must back up the Cisco UCS configuration. The backup job must meet these requirements:
• It must use the TCP protocol.
• Client identification must be verified before data is transmitted.
• The backup must contain all the system and logical configuration settings.
• The operations team requires that the backup file is in a human-readable format.
Which set of configurations must the engineer use?
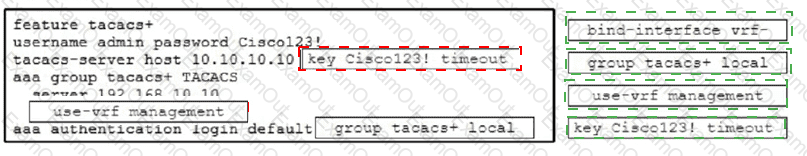
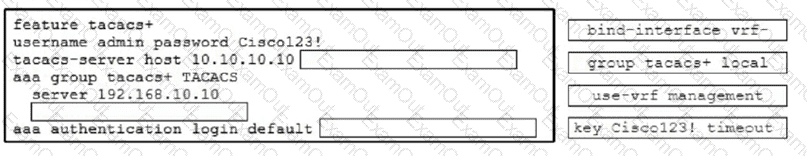
All logins to a Cisco Nexus 9000 Series Switch must pass through the TACACS+ server at IP address 192.168.10.10. The configuration must meet these requirements:
• The TACACS+ server must be used for SSH and Telnet.
• The TACACS+ server key must be Cisco123!.
• Management VRF must be used for connectivity.
• The deployment must fail back to local credentials if the TACACS+ server fails to respond within 30 seconds.
Drag and drop the code snippets from the right onto the blanks in the code on the left to complete the configuration. Not all code snippets are used.
What occurs when running the command install deactivate
< filename > while a software maintenance upgrade is performed on a Cisco Nexus 9000 Series switch?
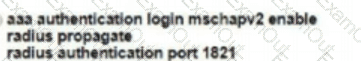
An engineer must apply AAA configuration on a Cisco MDS 9000 Series Switch The solution must meet these conditions :
It must use a challenge-response authenticator protocol that uses MD5 hashing with an incrementally changing identifier
The RADIUS configuration must be automatically shared with other MDS switches in the environment
The RADIUS server is already defined. Which command set completes the configuration?
A)user naed
B)
C)
D)
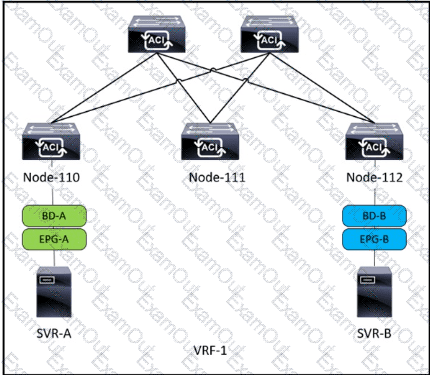
Refer to the exhibit. SVR-A in EPG-A/BD-A fails to reach SVR-B in EPG-B/BD-B. Which two conditions should be verified to analyze the traffic between the two EPGs? (Choose two.)
Which storage technology provides a simple, high-capacity solution and offers a direct file-access level to the shared storage?