A marketer is using Adobe Real-Time CDP and wants to exclude potential customers who have already made a purchase in the last 30 days from being targeted in an upcoming holiday discount campaign. What criterion would the marketer use to create the audience segment for the campaign?
A data architect is building an XDM Experience Event Schema for loading event data from the Adobe Experience Platform (AEP) Web SDK. The data is intended to be used in the Real-Time customer profile and requires a primary identity to be present in the schema. The architect wants to be able to store both ambiguous and authenticated web data.
Does the data architect need to select a field as a primary identity?
A data engineer encounters persistent ingestion failures for a batch ingestion in the Adobe Real-Time CDP. To troubleshoot and resolve the issue, what two steps would the data engineer take? (Choose two.)
A financial services customer wishes to suppress people from active credit card campaigns as soon as they submit an application for the associated credit card name. The business's goal is to optimize ad spend by suppressing people quickly who convert and use the savings to help funnel more money back into their acquisition strategies. The current data model that IT has provided from their data warehouse looks like the following:
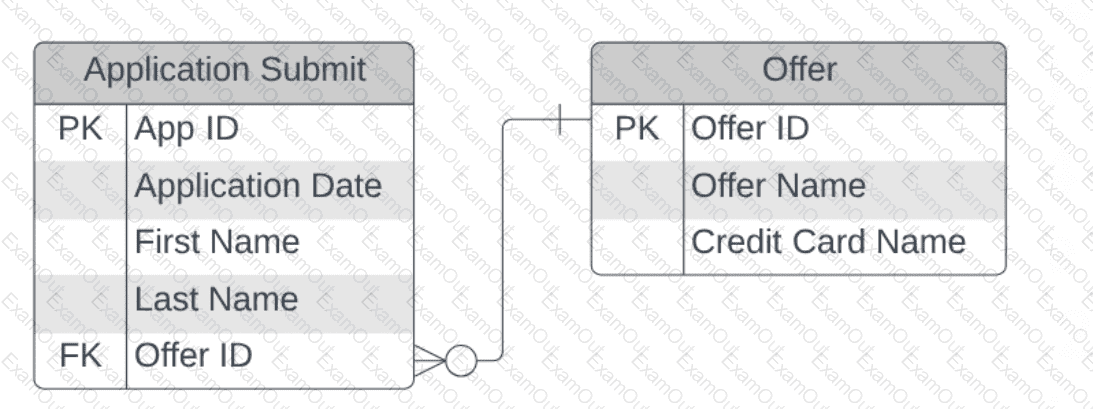
It is assumed that each application submit contains an offer that is always associated to a credit card name. Assuming all applications are streamed into the Real-Time Customer Profile, in which two ways could a developer model the application submit event to ensure the real-time suppression requirement is supported? (Choose two.)
A company has completed their implementation of Adobe Experience Platform (AEP) and is successfully onboarding data and profiles, but they are struggling with managing data across their services. What tool would best aid the company in inspecting, manipulating, and analyzing dataset data in AEP Data Lake?
A data analyst is trying to apply a series of complex conditions to filter audiences in Adobe Real-Time CDP for a client's online sale event. What would be the two recommended courses of action in terms of segment creation in this situation? (Choose two.)
A customer needs to access profile data using /access/entities endpoint. What parameters are required to retrieve profile information?
A data architect is tasked with maintaining synchronization between Edge and Adobe Real-Time CDP profiles in a dynamic data environment. The developer needs to determine the frequency and extent of the synchronization between Edge and Adobe Real-Time CDP profiles. What is the primary factor that should be used to complete this task?
A media company uses Adobe Experience Platform to process large quantities of media consumption data. This data was previously stored in a relational database management system (RDBMS) but has been migrated to the Adobe Real-Time CDP's NoSQL data model for improved scalability and performance. The data set includes information such as user ID, media content ID, play duration, pause durations, and timestamps of each interaction. Which combination of Experience Data Model (XDM) schemas should be used to efficiently capture and retrieve this data with the Adobe Real-Time CDP's NoSQL data model, considering the real-time analytics needs?
A system admin is looking to implement attribute-based access control (ABAC) in their Adobe Real-Time CDP (RTCDP) to support unique data access requirements for various user groups within the organization. Which method represents the most efficient way to set up ABAC in RTCDP?

