John joined the ISC2 organization. His manager asked him to check the authentication controls in a security module. What would John use to ensure a certain control is working as he expects it to?
Which protocol would be most suitable to fulfill the secure communication requirements between clients and the server for a company deploying a new application?
What is meant by non-repudiation?
Which of the following is NOT one of the three main components of an SQL database?
An IP network protocol standardized by the IETF through RFC 792 to determine if a host is available is:
Which is NOT a component of a Business Continuity (BC) plan?
David's team recently implemented a new system that gathers information from a variety of different log sources, analyzes that information, and then triggers automated playbooks in response to security events. What term BEST describes this technology?
Exhibit.
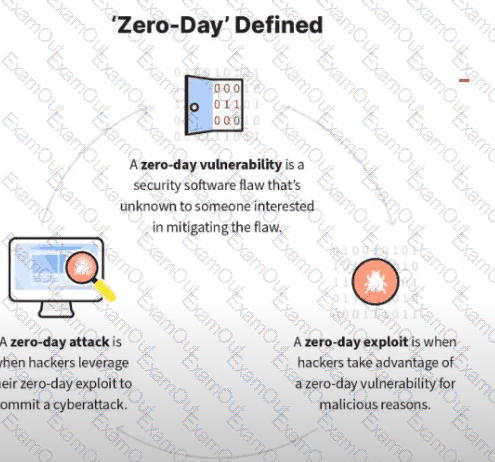
What kind of vulnerability is typically not identifiable through a standard vulnerability assessment?
A DDoS attack affects which OSI layers?
An unusual occurrence in a system or network is best described as:

