An internal auditor is assessing the organization's risk management framework. Which of the following formulas should he use to calculate the residual risk?
A) 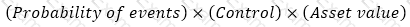
B)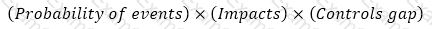
C)
D)
Which of the following should management action plans include at a minimum?
An internal auditor is assessing whether a vendor onboarding procedure is being followed in all business units. The procedure has been centrally designed and depicts activities and validations that must be performed at every step. Which of the following is the most suitable way to compile an internal control questionnaire?
Which of the following is the best option for the chief audit executive to consider for effective coordination of assurance coverage?
The internal audit activity of an insurance company is reviewing six of the company’s 11 branches. During the review of the fourth branch that was selected, the internal audit team discovered control breaches that could result in regulatory sanctions if not addressed. How should the internal audit team proceed?
Which type of assurance engagement is conducted to determine whether a process or area is performing as intended, accomplishing its objectives, and doing so in an efficient and economical way?
A bakery chain has a statistical model that can be used to predict daily sales at individual stores based on a direct relationship to the cost of ingredients used and an inverse relationship to rainy days. What conditions would an auditor look for as an indicator of employee theft of food from a specific store?
In a small internal audit function, a single auditor is responsible for conducting the entire audit engagement. In this situation, what is the benefit of using a checklist as part of an engagement work program?
If observed during fieldwork by an internal auditor, which of the following activities is least important to communicate formally to the chief audit executive?
Which of the following situations best applies to an organization that uses a project, rather than a process, to accomplish its business activities?
In an organization with a large internal audit activity that has several audit teams performing engagements simultaneously which of the following tasks is an engagement supervisor most likely to perform during the planning phase of a new engagement?
Which of the following would best prevent phishing attacks on an organization?
An engagement supervisor reviewed a staff internal auditor's documentation and noted that several edits should be made. The internal audit activity uses an electronic workpaper database and does not maintain paper files for its system of record. A system error prevents the engagement supervisor from adding her electronic signature to any workpaper in the database Given this situation which is the most appropriate response to provide evidence of supervisory review?
Which of the following analytical procedures should an internal auditor use to determine whether monthly expenses for the accounting department are reasonable?

