A collector attempts to access a known malicious website. FortiEDR is configured for eXtended detection with FortiAnalyzer. What two roles does Fortinet Cloud Services (FCS) perform in this process? (Choose two answers)
You added three new applications to FortiEDR using only the Path attribute. What are two expected outcomes of this configuration? (Choose two answers)
You find third-party software on a user’s computer that does not appear in the application list on the communication control console. Which two statements are true about this situation? (Choose two answers)
Refer to the exhibits.
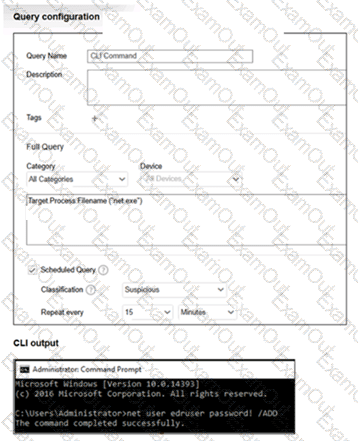
What happens when the net user command runs on an endpoint? (Choose one answer)
Which two statements correctly describe the IoT probing process on FortiEDR? (Choose two answers)
An employee leaves the company and no longer has access to the FortiEDR system. You must ensure GDPR compliance regarding the employee’s personal data stored in FortiEDR. Which two data types must be removed to meet GDPR requirements? (Choose two answers)
Which two Python commands are supported when using FortiEDR Connect to directly access a protected device shell? (Choose two answers)
Refer to the exhibit.
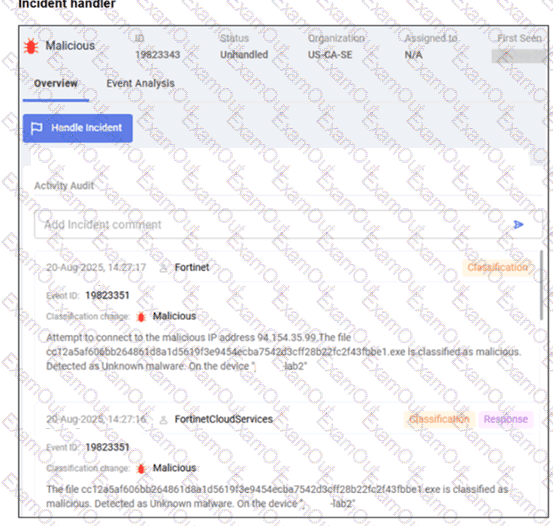
Based on the exhibit, which two observations are true? (Choose two answers)
A company requires a global communication policy for a FortiEDR multi-tenant environment. Which recommendation must you make? (Choose one answer)

