Which statement about security posture tags in FortiSASE is correct?
Which three reports are valid report types in FortiSASE? (Choose three.)
Which FortiSASE feature monitors SaaS application performance and connectivity to points of presence (POPs)?
Which three authentication sources support secure identity verification and access control for FortiSASE remote users? (Choose three.)
For a small site, an administrator plans to implement SD-WAN and ensure high network availability for business-critical applications while limiting the overall cost and the cost of pay-per-use backup connections.
Which action must the administrator take to accomplish this plan?
What is the purpose of the on/off-net rule setting in FortiSASE?
Refer to the exhibit.
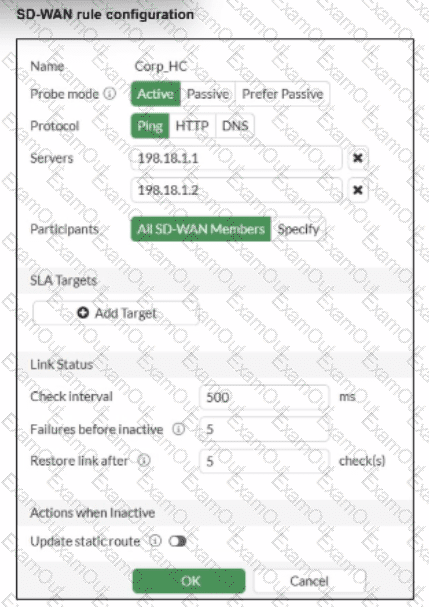
You want the performance service-level agreement (SLA) to measure the jitter of each member. Which configuration change must you make to achieve this result?
Which two delivery methods are used for installing FortiClient on a user's laptop? (Choose two.)
Refer to the exhibits.
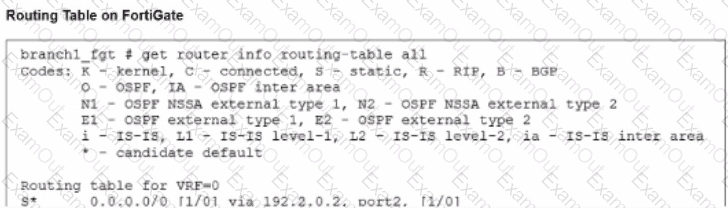
The administrator increases the member priority on port2 to 20. Upon configuration changes and the receipt of new packets, which two actions does FortiGate perform on existing sessions established over port2? (Choose two.)
SD-WAN interacts with many other FortiGate features. Some of them are required to allow SD-WAN to steer the traffic.
Which three configuration elements must you configure before FortiGate can steer traffic according to SD-WAN rules? (Choose three.)

