An externalA .R.T.I.E.user requires access to sensitive resources and data.
Which authentication technique should be best recommended to provide access to this business user?
A .R.T.I.E.is planning to deploy some of their applications in a public cloud. A major concern is how to share and protect data off premises. Also, how data can be used in decision making without exposing it to anyone who should not have access. Dell Services briefed them about various control mechanisms to secure data in the public cloud.
Which control mechanism should be selected in this scenario?
To minimize the cost and damage of ransomware attacks the cybersecurity team provided static analysis of files in an environment and compare a ransomware sample hash to known data.
Which detection mechanism is used to detect data theft techniques to access valuable information and hold ransom?
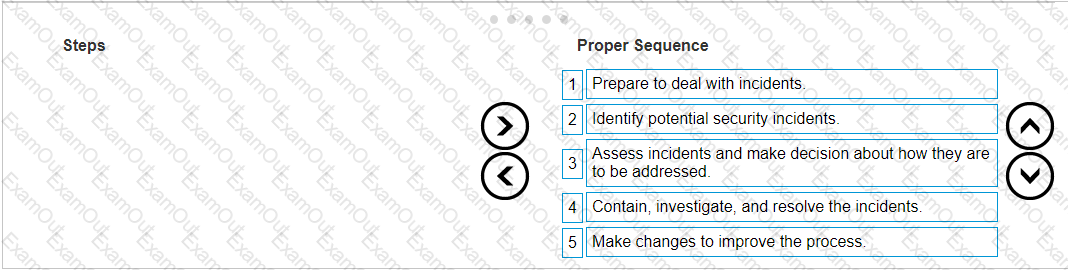
A .R.T.I.E.has an evolving need, which was amplified during the incidents. Their complex and dispersed IT environments have thousands of users, applications, and resources to manage. Dell found that the existing Identity and Access Management was limited in its ability to apply expanding IAM protection to applications beyond the core financial and human resource management application.A .R.T.I.E.also did not have many options for protecting their access especially in the cloud.A .R.T.I.E.were also not comfortable exposing their applications for remote access.
Dell recommended adopting robust IAM techniques like mapping out connections between privileged users and admin accounts, and the use multifactor authentication.
The Dell Services team suggest implementing a system that requires individuals to provide a PIN and biometric information to access their device.
Which type of multifactor authentication should be suggested?
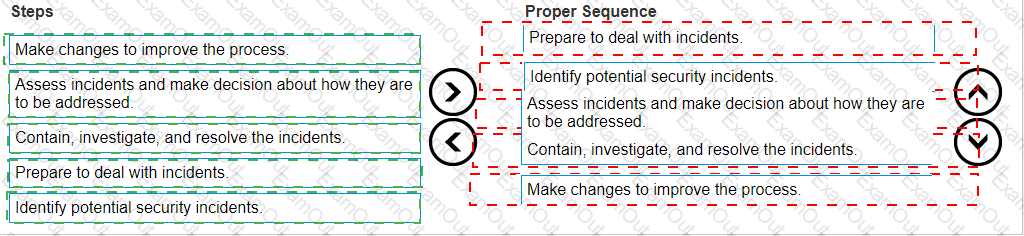
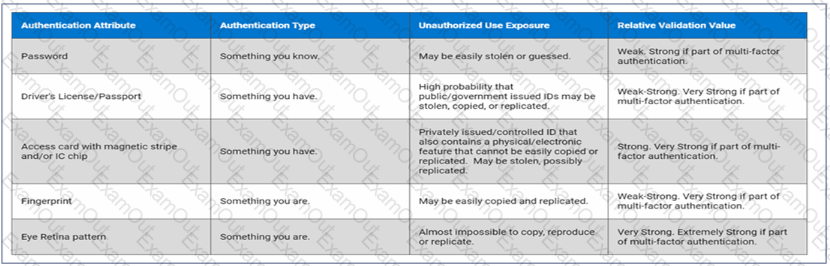
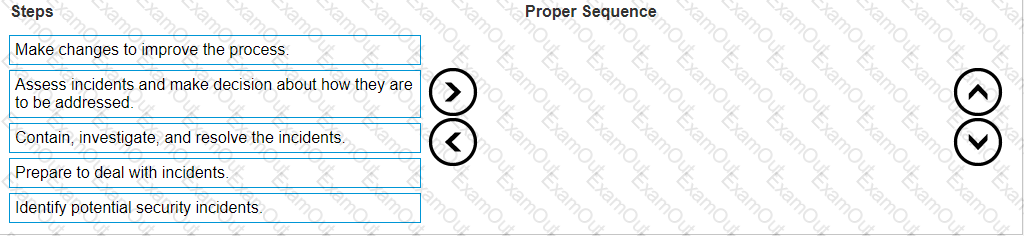
The cybersecurity team created a detailed security incident management procedures training program to manage any probable incidents atA .R.T.I.E.
Arrange the steps in the proper sequence to best manage cybersecurity incidents.
During the analysis, the threat intelligence team disclosed that attackers not only encrypted files, but also attempted to encrypt backups and shared, networked, and cloud drives.
Which type of ransomware is used for this attack?