Which of the following facilitates the continuous deployment of cloud applications without performing a clean install on each iteration?
A cloud administrator needs to distribute workloads across remote data centers for redundancy reasons. Which of the following deployment strategies would eliminate downtime, accelerate deployment, and remain cost efficient?
A company’s cybersecurity team receives the following alert that a production VM was deleted from the virtual network:
21 September 09:19:08 (GMT-5)
Resource with ID: PROD-WEB001 was deleted by User: Logging Service
The console to manage virtual network resources uses directory authentication. Only users in a particular directory group can interactively access the virtual network management console. The logging service account is not part of this group and requires some local administration privileges to aggregate logs from various resources. The cybersecurity team discovers the logging service account was previously given full directory administrator privileges and sees the following entry:
21 September 09:10:55 (GMT-5)
User with ID: Logging Service was added to the Group: VNet Console Administrators by actor: Logging Service.
The cybersecurity team removes the compromised service account from the directory group. Which of the following should the cybersecurity team do next to prevent repeat instances of this issue?
Five thousand employees always access the company's public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application Which of the following is the best configuration approach to resolve this issue?
Users have been reporting that a remotely hosted application is not accessible following a recent migration. However, the cloud administrator is able to access the application from
the same site as the users. Which of the following should the administrator update?
A cloud developer resigned from an organization and gave a two-week notice. Within the first week since the developer resigned, a security analyst identifies large volumes of file downloads to the developer’s laptop from the source code repository. Which of the following security controls is the best way to mitigate the organization’s risk of data loss?
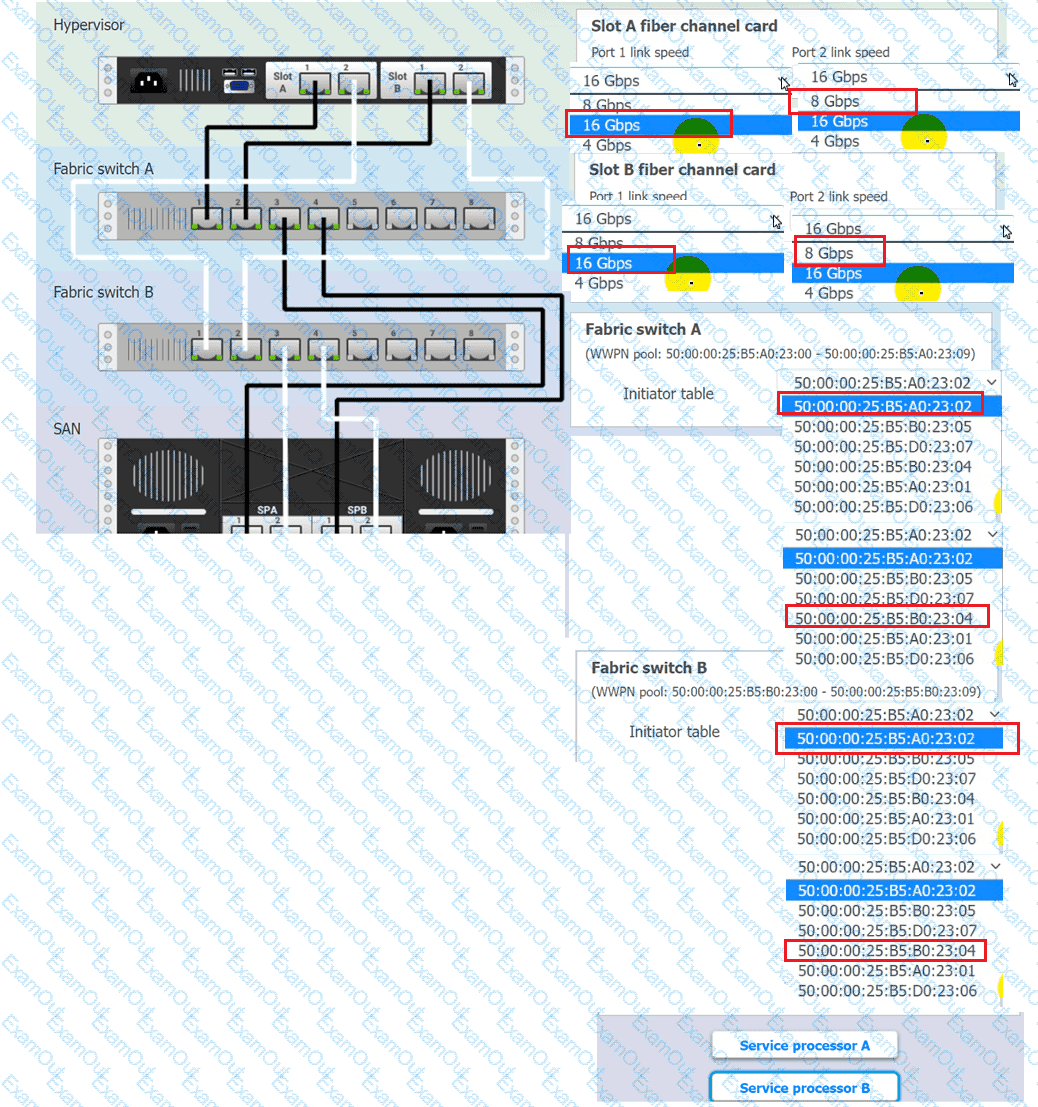
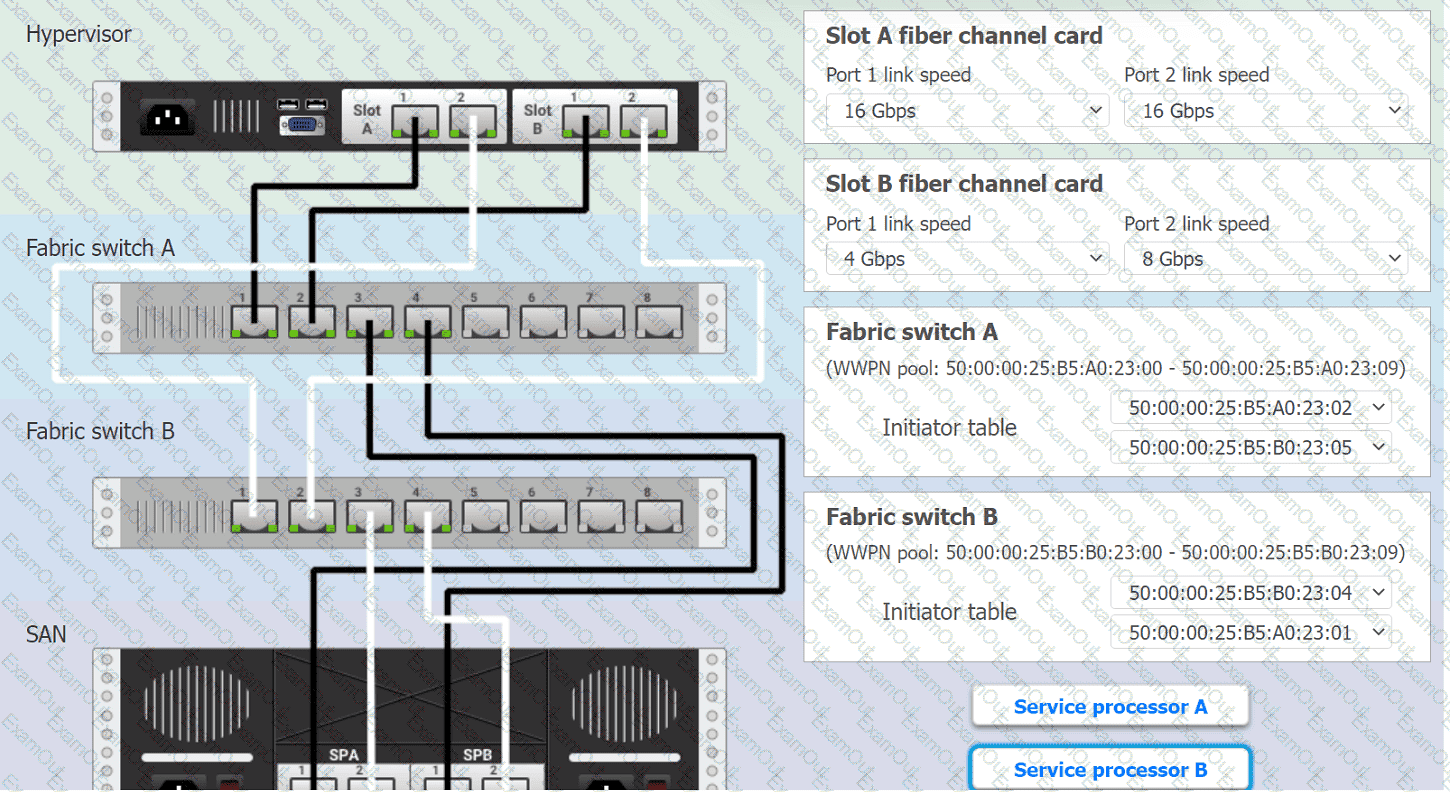
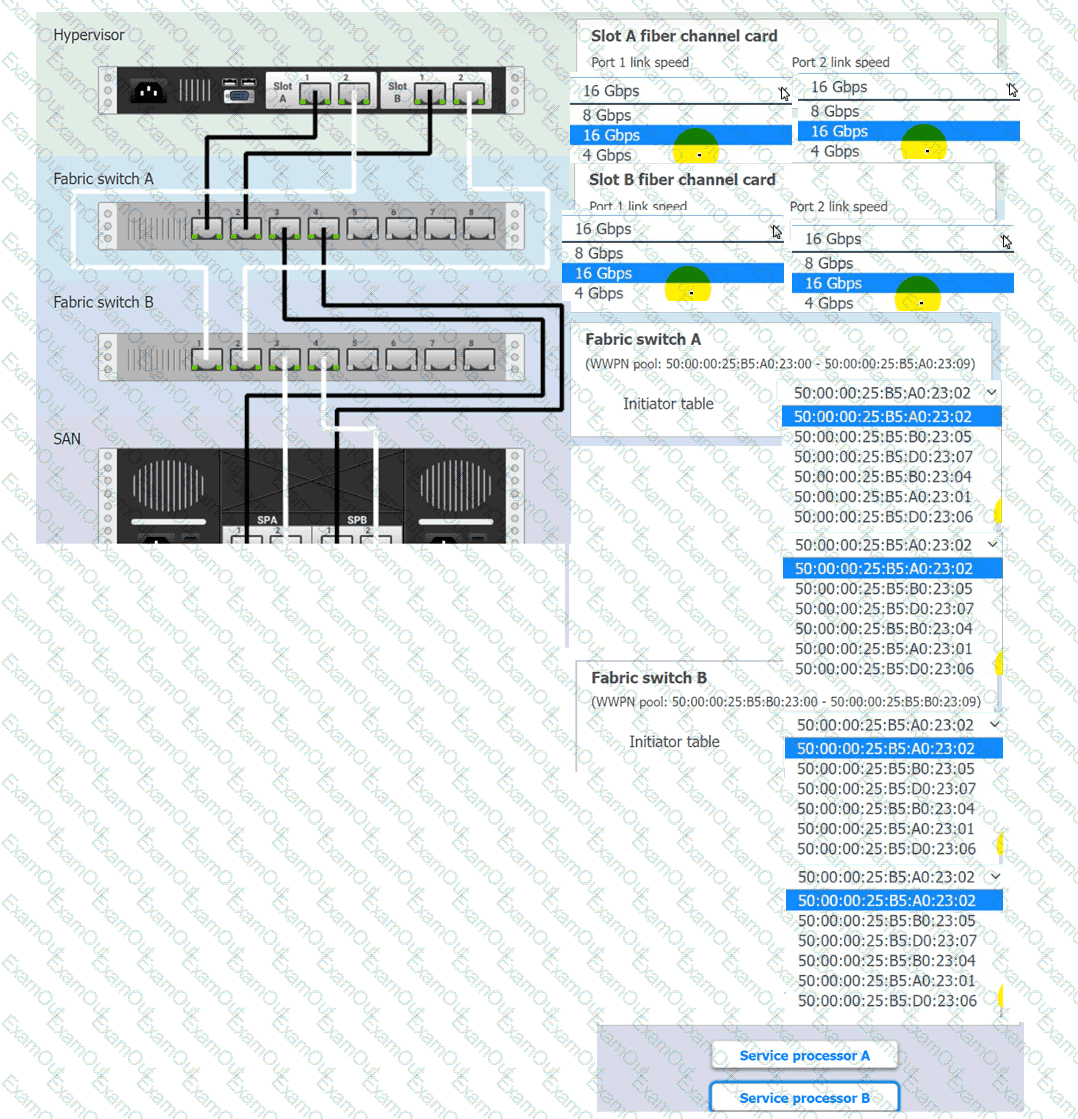
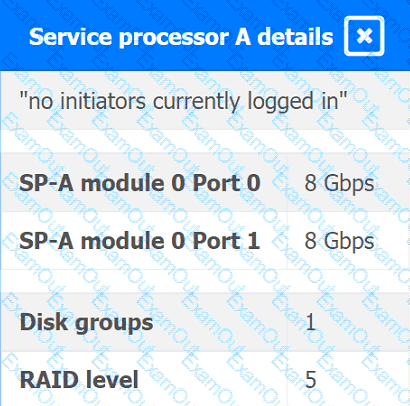
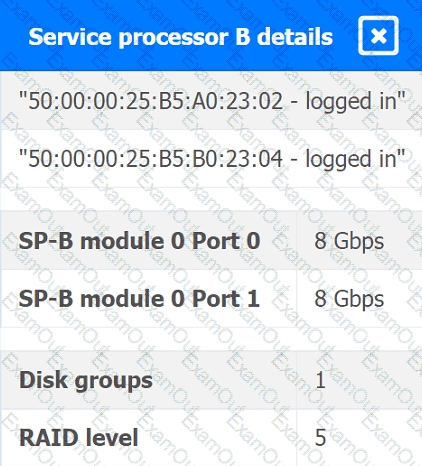
You are a cloud engineer working for a cloud service provider that is responsible for an
IaaS offering.
Your customer, who creates VMs and manages virtual storage, has noticed I/O bandwidth issues and low IOPS (under 9000).
Your manager wants you to verify the proper storage configuration as dictated by your service level agreement (SLA).
The SLA specifies:
. Each SFP on the hypervisor host must be set to the maximum link speed
allowed by the SAN array. . All SAN array disk groups must be configured in a RAID 5.
. The SAN array must be fully configured for redundant fabric paths. . IOPS should not fall below 14000
INSTRUCTIONS
Click on each service processor to review the displayed information. Then click on the drop-down menus to change the settings of each device as necessary to conform to the SLA requirements.
A cloud engineer needs to migrate an application from on premises to a public cloud. Due to timing constraints, the application cannot be changed prior to migration. Which of the
following migration strategies is best approach for this use case?
A company's man web application is no longer accessible via the internet. The cloud administrator investigates and discovers the application is accessible locally and only via an IP access. Which of the following was misconfigured?
A cloud developer is creating a static website that customers will be accessing globally. Which of the following services will help reduce latency?