A company stores customer credit reports in an Amazon S3 bucket. An analytics service uses standard Amazon S3 GET requests to access the reports.
A developer must implement a solution to redact personally identifiable information (PII) from the reports before the reports reach the analytics service.
Which solution will meet this requirement with the MOST operational efficiency?
A developer is troubleshooting an application mat uses Amazon DynamoDB in the uswest-2 Region. The application is deployed to an Amazon EC2 instance. The application requires read-only permissions to a table that is named Cars The EC2 instance has an attached IAM role that contains the following IAM policy.
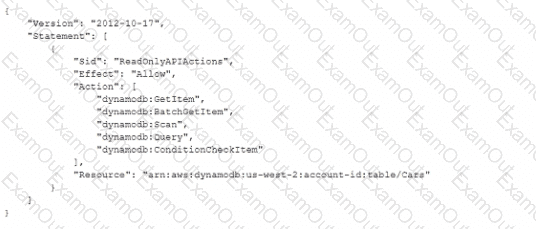
When the application tries to read from the Cars table, an Access Denied error occurs.
How can the developer resolve this error?
A developer has designed an application to store incoming data as JSON files in Amazon S3 objects. Custom business logic in an AWS Lambda function then transforms the objects, and the Lambda function loads the data into an Amazon DynamoDB table. Recently, the workload has experienced sudden and significant changes in traffic. The flow of data to the DynamoDB table is becoming throttled.
The developer needs to implement a solution to eliminate the throttling and load the data into the DynamoDB table more consistently.
Which solution will meet these requirements?
A company has an application that generates large binary data outside of AWS . The company must encrypt the data before uploading the data to an Amazon S3 bucket.
Which solution will meet this requirement?
A developer is writing a web application that must share secure documents with end users. The documents are stored in a private Amazon S3 bucket. The application must allow only authenticated users to download specific documents when requested, and only for a duration of 15 minutes.
How can the developer meet these requirements?
A company has an application that runs as a series of AWS Lambda functions. Each Lambda function receives data from an Amazon Simple Notification Service (Amazon SNS) topic and writes the data to an Amazon Aurora DB instance.
To comply with an information security policy, the company must ensure that the Lambda functions all use a single securely encrypted database connection string to access Aurora.
Which solution will meet these requirements ' ?
A developer is working on an ecommerce website The developer wants to review server logs without logging in to each of the application servers individually. The website runs on multiple Amazon EC2 instances, is written in Python, and needs to be highly available
How can the developer update the application to meet these requirements with MINIMUM changes?
A developer creates an Amazon API Gateway REST API that has a usage plan. The REST API sits in front of an AWS Lambda function. The Lambda function calls a third-party fulfillment service that returns standard HTTP status codes. The developer enables API Gateway and Lambda logging in Amazon CloudWatch. CloudWatch metrics for API Gateway show the occurrence of 5XX errors but do not show the occurrence of 4XX errors. The Lambda execution log also states: “ERROR: Rate limit exceeded from fulfillment service.” The developer needs to resolve the errors. Which solution will meet these requirements?
A developer is building a web and mobile application for two types of users: regular users and guest users. Regular users are required to log in, but guest users do not log in. Users should see only their data, regardless of whether they authenticate. Users need AWS credentials before they can access AWS resources.
A developer manages an AWS Lambda function written in the latest version of .NET. The function processes data from an Amazon S3 bucket sporadically throughout the day. The function experiences cold start times of up to 10 seconds , negatively affecting latency-sensitive downstream workloads.
The developer needs to improve the function’s performance.
Which solution will meet this requirement?
A developer creates an AWS Lambda function to publish messages to an Amazon SNS topic. All message content must be encrypted in transit and at rest between AWS Lambda and Amazon SNS.
A portion of the Lambda execution role policy is shown:
" Effect " : " Allow " ,
" Action " : " sns:Publish " ,
" Resource " : " arn:aws:sns:us-east-1:1234567890:secure-topic "
Which combination of steps should the developer take to meet these requirements? (Select TWO.)
A healthcare company uses AWS Amplify to host a patient management system. The system uses Amazon API Gateway to expose RESTful APIs. The backend logic of the system is handled by AWS Lambda functions.
One of the Lambda functions receives patient data that includes personally identifiable information (PII). The Lambda function sends the patient data to an Amazon DynamoDB table. The company must encrypt all patient data at rest and in transit before the data is stored in DynamoDB.
A developer accesses AWS CodeCommit over SSH. The SSH keys configured to access AWS CodeCommit are tied to a user with the following permissions:
The developer needs to create/delete branches
Which specific IAM permissions need to be added based on the principle of least privilege?
A company is building an ecommerce application. The company stores the application ' s static content in an Amazon S3 bucket. The application stores data that includes personally identifiable information (PII). The application makes dynamic requests in JSON format through an Amazon CloudFront distribution to an Amazon API Gateway REST API. The REST API invokes an AWS Lambda function that stores and queries data in Amazon DynamoDB.
The company must ensure that all PII data is encrypted at rest in DynamoDB. The company must also protect specific data fields more granularly. The company must ensure that the specified fields are encrypted at the edge. The specified fields must remain encrypted throughout the full stack of the application.
Which solution will meet these requirements?
An ecommerce company manages its application ' s infrastructure by using AWS Elastic Beanstalk. A developer wants to deploy the new version of the application with the least possible application downtime. The developer also must minimize the application ' s rollback time if there are issues with the deployment.
Which approach will meet these requirements?

